3-2-1 Backup Rule: The Rule of Thumb to Solve Your Data Loss Problems
Downtime from ransomware attacks results in an average of 16.2 days of downtime for businesses, according to Coveware’s Q4 2019 Ransomware Marketplace report
While it may sound like a rule for kids, the “3 2 1 backup rule” is something that helps save organizations from the brink of disaster.
Whether you’re an individual who loves to take photos of your pet, or you’re an enterprise dealing with tons of data on a daily basis, data loss is a threat that’ll always be a risk to you. Unfortunately, there’s no singular method by which we can stop all forms of data loss as there’s no way to know when and where it hits you. And by the time you realize it, it’s always too late. That’s where having a digital backup — a not-so-exciting term — comes into play.
The thing about backups is that nobody likes doing them — that is, until you lose your primary data and the blood and sweat you’ve invested after backups finally pays off. But until that time, it’s a thankless job that one must keep on doing time after time. Simply put, the choice is clear: you must take regular backups or suffer the consequences. Going with the former seems the obvious and wise choice, but making that decision isn’t enough here as the data you’ve backed up could be compromised or lost.
So, what’s the best way to protect your organization and customers?
Let’s hash it out.
Why Following the 3-2-1 Backup Is the Solution
We don’t blame you for thinking that the 3 2 1 backup rule (or “3-2-1 backup rule,” if you prefer) sounds like a psychological trick that tells you to stop procrastinating and take backups. The reason behind this is that this not-so-nerdy sounding name was suggested by a photographer (yes!) named Peter Krogh. He coined this term in his book “The DAM Book: Digital Asset Management for Photographers” and, since then, it’s become a mainstream method for making backups, even among the techie crowd.
The popularity of this method lies in its effectiveness. So much so that even the US-CERT recommends it for creating backups.
In contrast to what it sounds like, the 3-2-1 backup is not a rule — rather, it’s a thoughtful backup strategy that aims to minimize the risk of data loss.
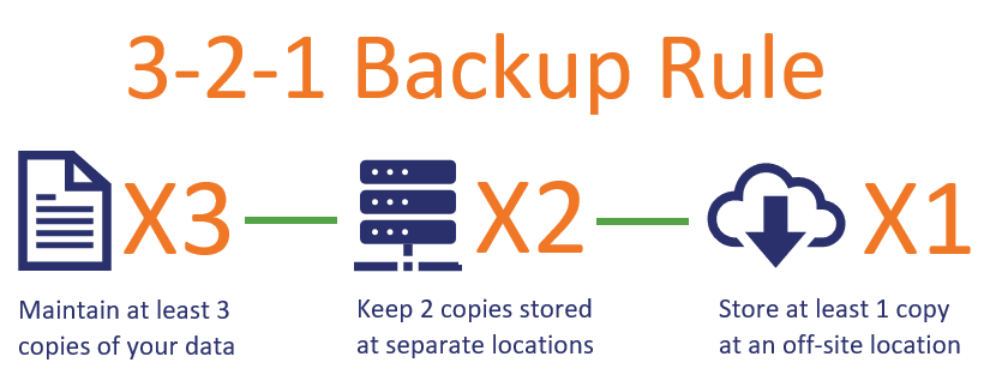
At its core, the 3 2 1 backup strategy involves:
- Keeping at least 3 copies of your data;
- Backing-up data on 2 different storage types;
- Storing at least 1 copy of the data offsite.
To better understand this concept, let’s consider the following example of backing up documents stored in your computer:
Now, according to the 3-2-1 rule, you must regularly back up all of your pertinent files and documents on two devices of different types or storage media. Therefore, you must store your documents on a device that’s not attached to your computer. These formats include:
- External hard drive,
- Optical disks,
- Digital tape,
- USB drives, or
- Cloud storage.
A highly recommended option is to store your documents on Network Attached Storage (NAS). These devices are affordable, easy-to-access on-site storage back up solutions. A major advantage when it comes to NAS devices is that you can access them anytime you want and they won’t be affected by most threats as they act independently from your main system. (Kaspersky reports that there is a growing threat to NAS storage by a specific type of ransomware, but you can take steps to protect your devices.)
Backing up your data on an external on-site device will surely do you good, but it’s not enough as it could be damaged in case of a local disaster. That’s where the “1” in the 3 2 1 backup rule comes into play. This part of the 3-2-1 rule states that you must store at least one copy of your data at an off-site location such as a cloud server in another part of the country.
Even if it’s not on cloud that you want to use, the storage location/device should be located as far away from the primary data location as possible. This way, if an earthquake, wildfire, or another natural (or manmade) disaster were to impact the region where your primary storage backups are located, you’d still have a backup at another regional location that you can fall back on.
Why the 3-2-1 Rule Works
Thanks to the on-site back up you’ve created, you won’t have to go running around in the event that your primary device gets compromised. You’ll be able to restore your data promptly by using the two on-site backup devices that you have available.
Now, what if the unimaginable happens, and both the primary device as well as both the on-site device get lost or damaged? That’s where the off-site storage comes in to save you from all the anguish you’d otherwise face. The off-site data that you’ve stored will protect your data in case both devices — your primary and back up devices — suffer damage and lose your data. This might seem unlikely, but it’s certainly a possibility in disasters such as tornadoes, earthquakes, floods, etc.
The double-layer protection and greater data-access flexibility are the reasons why the 3-2-1 backup rule is a strategy that’s recommended by security experts the world over. But there is one important thing to remember with all of this…
The 3-2-1 Backup Rule Is Great — But Only When You Implement It Properly
No matter how good a plan looks on paper, it must be implemented correctly to make it work the way it’s supposed to. The 3-2-1 backup rule is no exception here. The 3-2-1 backup rule sounds like a fool-proof plan that won’t let your data go away anywhere, but there are things that you need to consider.
Whether you’re an individual who wants to back up your cute cat photos or an organization that wants to back up a ton of organizational or customer data, the 3-2-1 backup strategy can be your rule of thumb for data protection and disaster recovery because it minimizes the chances of data loss, thanks to its double layer of protection.
Having three copies of your data is, of course, great but it’s not enough as there are factors that matter immensely to make or break your backup strategy. Here are four tips to ensure your backups are there when you need them:
- Implement access measures to ensure the security of your backups. You must ensure that the devices and backups you use can be accessed only by authorized individuals. These devices must be secure so that the data doesn’t get damaged, lost, or stolen.
- Schedule and perform frequent backups. You must take backups at short, regular intervals to ensure that the all data is backed up.
- Use encryption to protect your at-rest data. If your data is sensitive and could affect you or your customers should an unintended user gets access, then you must encrypt it so that an unauthorized person won’t be able to see or tamper with it.
- Perform regular quality checks to ensure the backups are working. What if your backup device has become infected with malware and it’s corrupting your data? And what if you don’t even notice until it’s too late? That’s why, you must regularly perform quality checks to ensure that the data is working so it’s there when you need it.
A Final Word on the 3-2-1 Backup Rule
It’s never a pretty sight to see someone lose all their data, and it’s even more painful if you’re that person. Nobody wants to lose their data and that’s why everyone needs to back up their data, no matter how boring or monotonous the task may seem.
The 3-2-1 backup strategy might sound like a lot of work, but it could save you a lot of time, frustration, and money when things eventually go wrong. And if Murphy’s Law is true, things inevitably always will go wrong at some point.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown