Re-Hashed: How to clear HSTS settings in Chrome and Firefox
A quick look at what HSTS is and how to clear it on two of the most popular browsers.
HSTS stands for HTTP Strict Transport Security, it’s a web security policy mechanism that forces web browsers to interact with websites only via secure HTTPS connections (and never HTTP). This helps to prevent protocol downgrade attacks and cookie hijacking.
HSTS was originally created in response to a vulnerability that was introduced by Moxie Marlinspike in a 2009 BlackHat Federal talk titled “New Tricks for Defeating SSL in Practice.” The particular vulnerability that HSTS defends against is the one illustrated by Marlinspike’s SSLStrip tool.
Essentially the tool works by converting secure HTTPS connections back to unsecured HTTP ones. HSTS remedies this by communicating to the browser that an HTTPS connection should always be in place. HSTS can also help to prevent cookie-based login credentials from being stolen by common tools such as Firesheep.
Unfortunately, some HSTS settings can inadvertently cause browser errors. For instance, if you’re using Chrome, you might run into:
“Privacy error: Your connection is not private” (NET::ERR_CERT_AUTHORITY_INVALID).
If you attempt to reach the same site on another browser and don’t run into the same issues, it could just be a problem with how the HSTS settings have affected your original browser. In that case, you will need to clear them. Here’s how to clear HSTS settings on Google Chrome and Mozilla Firefox.
Clear and Forget HSTS Settings In Popular Browsers.
If your browser has stored HSTS settings for a domain and you later try to connect over HTTP or a broken HTTPS connection (mis-match hostname, expired certificate, etc) you will receive an error. Unlike other HTTPS errors, HSTS-related errors cannot be bypassed. This is because the browser has received explicit instructions from the browser not to allow anything but a secure connection.
HSTS settings include a “max-age” option, which tells the browser how long to cache and remember the settings before checking again. In order to immediately proceed past the error, you will need to delete your browser’s local HSTS settings for that domain. Instructions on how to do so are below.
These settings need to be cleared in each browser. As a developer, you may run into this error if you are testing an HSTS configuration. In Chrome, you can receive this error on localhost. If you have deployed HSTS onto a live site for end users, it may be infeasible to correct the errors they are having depending on the size of your audience. Each user needs to delete their local HSTS settings or wait for them to expire according to the ‘max-age’ that was set.
Also note that if the website is still serving the HSTS header, your browser will store it as soon as you visit the site again. So you must first stop sending that header if you don’t want the error to reoccur.
Neither Chrome nor Firefox have a unique error code for HSTS errors, but the interstitial error pages will include information about HSTS.
Delete HSTS Settings
Note that these instructions are mainly useful for developers who were testing HSTS and now need to delete the settings. For a website you do not control, deleting your browser’s local HSTS settings will not help if the website is still serving an HSTS header as your browser will simply save the settings again on each visit/refresh.
In Chrome you may see the error “NET::ERR_CERT_COMMON_NAME_INVALID.” If you click “Advanced” in Chrome the error message will include “You cannot visit domain.com right now because the website uses HSTS.” That will confirm the error is HSTS-related. On localhost you may see the error “This site can’t provide a secure connection.”
In Firefox the interstitial page will read: “This site uses HTTP Strict Transport Security (HSTS) to specify that Firefox may only connect to it securely. As a result, it is not possible to add an exception for this certificate.”
If you have determined the error is due to cached HSTS settings, follow the following instructions to resolve the error:
How to Delete HSTS Settings in Chrome:
- Navigate to chrome://net-internals/#hsts
This is Chrome’s UI for managing your browser’s local HSTS settings.
- First, to confirm the domain’s HSTS settings are recorded by Chrome, type the hostname into the Query Domain section at the bottom of the page. Click Query.If the Query box returns Found with settings information below, the domain’s HSTS settings are saved in your browser.
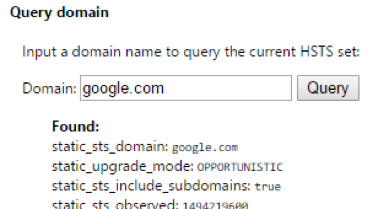
Note that this is a very sensitive search. Only enter the hostname, such as www.example.com or example.com without a protocol or path.
- Type the same hostname into the Delete domain section and click
Your browser will no longer force an HTTPS connection for that site! You can test if its working properly by refreshing or navigating to the page.
Note that depending on the HSTS settings provided by the site, you may need to specify the proper subdomain. For example, the HSTS settings for staging.yoursite.com may be separate from yoursite.com so you may need to repeat the steps as appropriate.
How to Delete HSTS Settings in Firefox:
We will cover two different methods for deleting HSTS settings in Firefox. The first method should work in most cases – but we also included a manual option if needed.
- Close all open tabs in Firefox.
- Open the full History window with the keyboard shortcut Ctrl + Shift + H (Cmd + Shift + H on Mac). You must use this window or the sidebar for the below options to be available.
- Find the site you want to delete the HSTS settings for – you can search for the site at the upper right if needed.
- Right-click the site from the list of items and click Forget About This Site.This should clear the HSTS settings (and other cache data) for that domain.
- Restart Firefox and visit the site. You should now be able to visit the site over HTTP/broken HTTPS.If these instructions did not work, you can try the following manual method:
Manual Method for Firefox
If the above steps do not work, you can try the following method.
Start by locating your Firefox profile folder through your operating system’s file explorer. You can find this folder through Firefox by navigating to about:support
Halfway down the page, in the Application Basics section, you will see Profile Folder. Click Open Folder.
Now close Firefox so that the browser does not overwrite any settings we are about to change.
In your Profile folder find and open the file SiteSecurityServiceState.txt. This file contains cached HSTS and HPKP (Key Pinning, a separate HTTPS mechanism) settings for domains you have visited. It may be very disorganized.
Search for the domain you want to clear the HSTS settings for and delete it from the file. Each entry beings with the domain name. Delete the entirety of the entry from the beginning of the desired domain name to the next listed domain. As an alternative, you can rename the existing file from a .txt to a .bak (in order to save the existing file, just in case) and allow Firefox to create an entirely new file on next start up.
Here is an example of a simple HSTS listing:
www.thesslstore.com:HSTS 0 17312 1527362896190,1,0
As mentioned, the formatting for this file can be messy. Below is a sample from my profile. Each domain’s settings are shown in a unique color to make separation clear. In this case, part of the settings for the previous domain appear the beginning in red:
1527363079029,1,0www.thesslstore.com:HSTS 0 17312
1527362896190,1,0scotthelme.co.uk:HPKP 0 17312 1498419087277,1,1,9dNiZZueNZmyaf3pTkXxDgOzLkjKvI+Nza0ACF5IDwg=X3pGTSOuJeEVw989IJ/cEtXUEmy52zs1TZQrU06KUKg=V+J+7lHvE6X0pqGKVqLtxuvk+0f+xowyr3obtq8tbSw=9lBW+k9EF6yyG9413/fPiHhQy5Ok4UI5sBpBTuOaa/U=ipMu2Xu72A086/35thucbjLfrPaSjuw4HIjSWsxqkb8=+5JdLySIa9rS6xJM+2KHN9CatGKln78GjnDpf4WmI3g=MWfCxyqG2b5RBmYFQuLllhQvYZ3mjZghXTRn9BL9q10=
api.github.com:HSTS 0 17312 1527362865303,1,1
Note: Re-Hashed is a regular weekend feature at Hashed Out where we select an older post to revisit. This week we take a look at the answer to one of the questions we get asked the most: How to fix SSL connection errors on Android phones.













































 (5 votes, average: 3.60 out of 5, rated)
(5 votes, average: 3.60 out of 5, rated)






5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown