Re-Hashed: How To Disable Firefox Insecure Password Warnings
We don’t recommend it, but here’s how to disable Firefox Insecure Password Warnings.
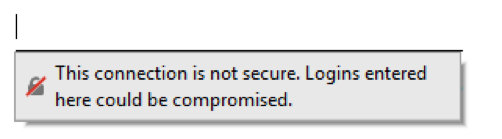
Firefox 52 added a new warning that appears on HTTP forms. It pops up below the field and takes the place of your saved password. It’s been cleverly dubbed the “Insecure Password Warning.”
If you regularly log in to HTTP sites on an intranet, or a website you use simply does not support HTTPS yet, this may annoy you.
Below are simple instructions to disable Firefox insecure password warnings, and instructions to turn autofill on for HTTP logins.
How To Disable Firefox 52 Insecure Form Warning
Keep in mind that your password can very easily be stolen if you are logging into websites over HTTP. If a website you use does not offer secure logins, use a unique password for that site and do not use it anywhere else.
Only follow these instructions if you want to turn off these important security settings in Firefox. Do not follow these instructions if someone else is telling you to.
Here’s how to disable Firefox insecure password warnings:
- Open a new tab, paste about:config into the address bar and hit enter.
- If you see the “This Might Void Your Warranty” page, click the blue “I accept the risk!” button. Understand we are manually modifying Firefox’s default settings.
- In the Search box at the top, paste security.insecure_field_warning.contextual.enabled
- Double click the setting to change it to “false”, to disable Firefox’s insecure password warning.
- Done! Now when you visit pages with HTTP login forms, the warning will no longer appear.
If you also want to restore autofill functionality, so that your saved login/password automatically populates in an HTTP form, keep the configuration page open and follow the next step.
Optional. In the Search Box on the about:config page, paste signon.autofillForms.http
Double click the setting to change it to “true,” this will enable autofill.
A Note About Web Safety
When a website is using HTTP, you have an insecure connection that transmits all your data in plaintext. That means if you log in to an HTTP website, your password is sent over your ISP’s network, across the internet, and to the server as is, with no protections. If your password is “Camaro70!” anyone monitoring the network can see that.
Obviously, this makes it very easy to steal your login information and gain access to your account.
To protect yourself, please set a unique password for each and every site you visit that uses HTTP. Do not even make it similar to other passwords (for example, don’t just change the number or add an extra character to the end).
You may not think your information is at risk, but tens of millions of passwords are stolen every year. If you are logging in on a public/shared network – such as a coffee shop, airport, or municipal wifi – an attacker likely has a computer persistently monitoring traffic looking for anything worth stealing.
We understand that users do not like change and that if a website you use does not support HTTPS, there may not be anything you can do. This is why we have provided instructions to disable Firefox insecure password warnings. But please consider the security implications and the risk of password re-use before doing so.
If you are a website administrator or service provider who tells their users to turns these settings off: We will find you, and we will tell everyone about your bad security practices. Do not encourage or mislead users into reducing their protections online.
Re-Hashed is a regular weekend feature at Hashed Out where we pick one of our more popular stories and share it with our new readers.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown