Browser Watch: Firefox 52 Adds Insecure Password Warning
Browsers Continue To Add Warnings About Insecure Content.
Firefox 52 is out now, and with a new release comes a new warning about HTTP.
There is a pattern here: browsers are incrementally adding warnings for HTTP, raising their expectations each month as the web moves further towards a fully-encrypted future.
So if you have not yet moved your site to HTTPS, you should really consider it.
This time the warnings are targeting login forms on insecure HTTP pages.
On any HTTP page, a new insecure password warning will appear directly below login fields when they become active (when a user clicks on/tabs to them). The warning makes sure any users will see the dangers of submitting data over HTTP.
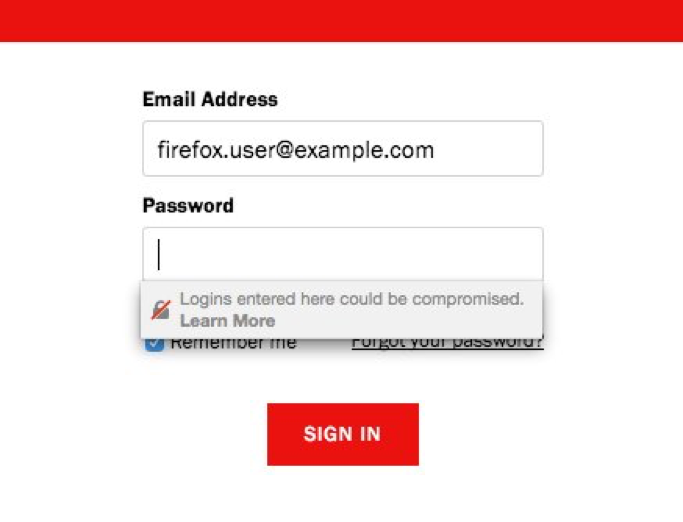
The warning reads, “This connection is not secure. Logins entered here could be comprised.” The Learn More link goes to this Firefox support page.
The entire page will also receive the broken padlock icon which displays the same warnings when clicked.
If you want to see the warnings in your own browser visit http-login.badssl.com.
Google Chrome 57, which is due out next week, adds similar in-form warnings. In addition to password fields, Chrome also detects insecure credit card forms.
For now, auto-fill will continue to work on HTTP forms, but developers should expect this to change in the near future as browsers continue to restrict functionality on HTTP web pages in order to preserve user privacy.
Firefox developers noted that since enabling this feature by default in the Developer release, the number of HTTPS secured login forms increased from 40% to just about 75%.
Remember that ALL websites need to be HTTPS. Why? Because believe it or not, most sites expose some sort of personal information – be it search queries, passwords, etc. HTTPS also provides integrity guarantees, stops content injection, and allows you to use HTTP/2 which is lightning fast. If you want to know more, start here.





































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)













5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown