Social Engineering Statistics 2025: When Cyber Crime & Human Nature Intersect
These 30 social engineering attack statistics reveal human vulnerabilities and how bad guys love to exploit them (to your detriment)
Social engineering doesn’t hack your company’s devices or digital assets; it “hacks” the people who have access to them.
Bad guys have been influencing the behaviors of others throughout recorded history. Whether it’s conning someone into buying a mule they don’t own or manipulating others into sharing secret intel, criminals will continue using human emotions and psychology to get what they want. But in the years since criminal activities moved into the digital world, we’ve seen how heavily cybercriminals rely on these same basic social engineering skills.
Cybercriminals continue to use these psychology-based tactics to trick, coerce, manipulate, threaten, or otherwise get targeted individuals to do their bidding.
So, what insights do the top social engineering statistics for 2025 offer?
Let’s hash it out.
TL;DR: Key Social Engineering Statistics You Should Know
Don’t have time to read an entire article about social engineering statistics? No worries — we’ve cultivated the top handful for you:
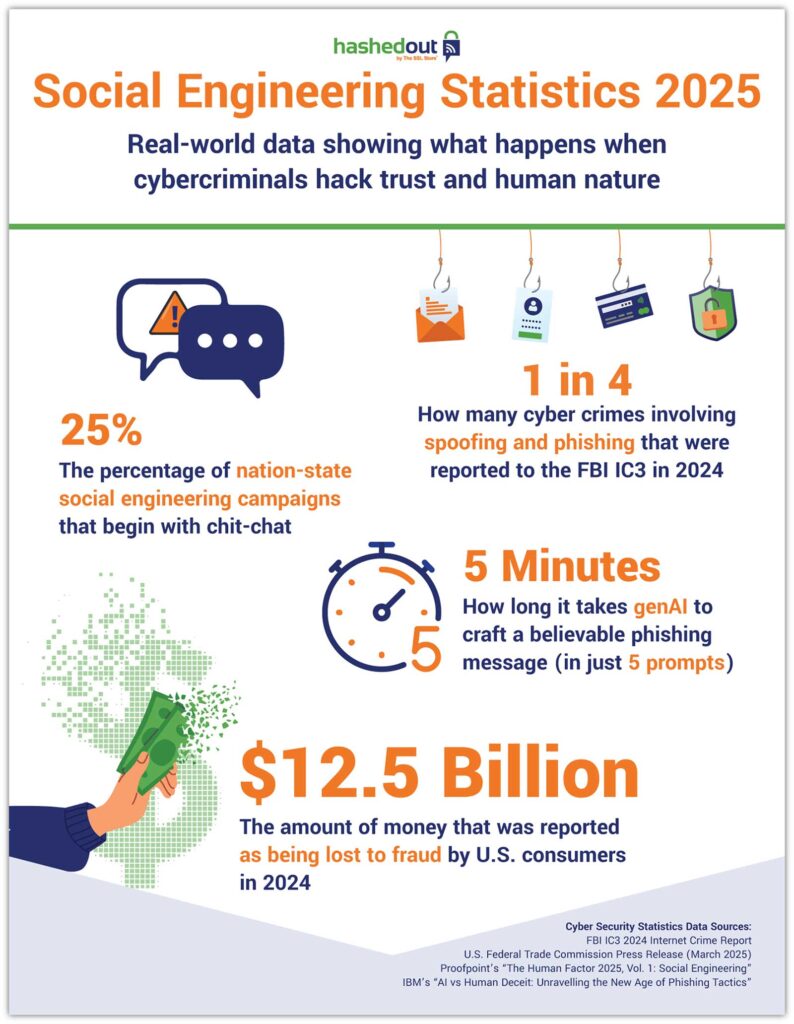
- Consumers reported fraud-related losses of $12.5 billion in 2024. (Source: U.S. Federal Trade Commission’s “New FTC Data Shows a Big Jump in Reported Losses to Fraud to $12.5 billion in 2024.”)
- One in three people who reported a scam also suffered financial losses. (Source: FTC’s “A Scammy Snapshot of 2024”)
- Phishing & spoofing attacks comprise nearly 1 in 4 cyber crimes reported to the FBI’s Internet Crime Complaint Center (IC3) in 2024. (Source: FBI IC3 2024 Internet Crime Report)
- A quarter of nation-state campaigns begin their attacks with chit-chat to disarm targets. (Source: Proofpoint The Human Factor 2025, Vol. 1: Social Engineering)
- Generative AI streamlines crafting a believable phishing message to just 5 minutes. (Source: IBM’s AI vs. Human Deceit: Unravelling the New Age of Phishing Tactics)
Want to Check Out Other Cyber-Related Statistics?
We’ve got you covered with the latest cyber crime statistics for 2025 and cyber security statistics.
Social Engineering Statistics: The Cost of These Attacks
While it’s true that social engineering attacks have far-reaching implications in terms of the reputational harm and loss of customer trust, let’s be real — you want to know the bottom-line impacts.
- U.S. consumers reported $12.5 billion in fraud-related losses in 2024 alone. Government impostor scams alone cost consumers $789 million in that period. (U.S. Federal Trade Commission’s “New FTC Data Shows a Big Jump in Reported Losses to Fraud to $12.5 billion in 2024.”)
- Social engineering is no longer the #1 threat (although it remains in the top three attack patterns) — exploits have claimed that “honor.” Verizon’s latest data indicates that social engineering is slowly shifting down the rankings as an initial access vector as vulnerability exploits move up the list. (Source: Verizon’s 2025 Data Breach Investigations Report [DBIR])
- A social engineering attack costs organizations an average of $130,000 in stolen data or monetary theft. If the attack is paired with other attack methods, that number can often skyrocket into the millions. (Source: CRC Group’s “Social Engineering & Cybercrime Remain Top Cyber Insurance Concerns”)
- More than $1 trillion globally has been lost to online scammers in the past year. (Source: WEF Global Cybersecurity Outlook 2025 report)
- Call center scams targeting seniors and crypto traders raked in a sickening $1.9 billion in reported losses in 2024. (Source: FBI IC3’s 2024 Internet Crime Report)
- North Korea’s IT worker scam is estimated to generate $250-600 million annually. (Source: United Nations’ Security Council Report S/2024/215)
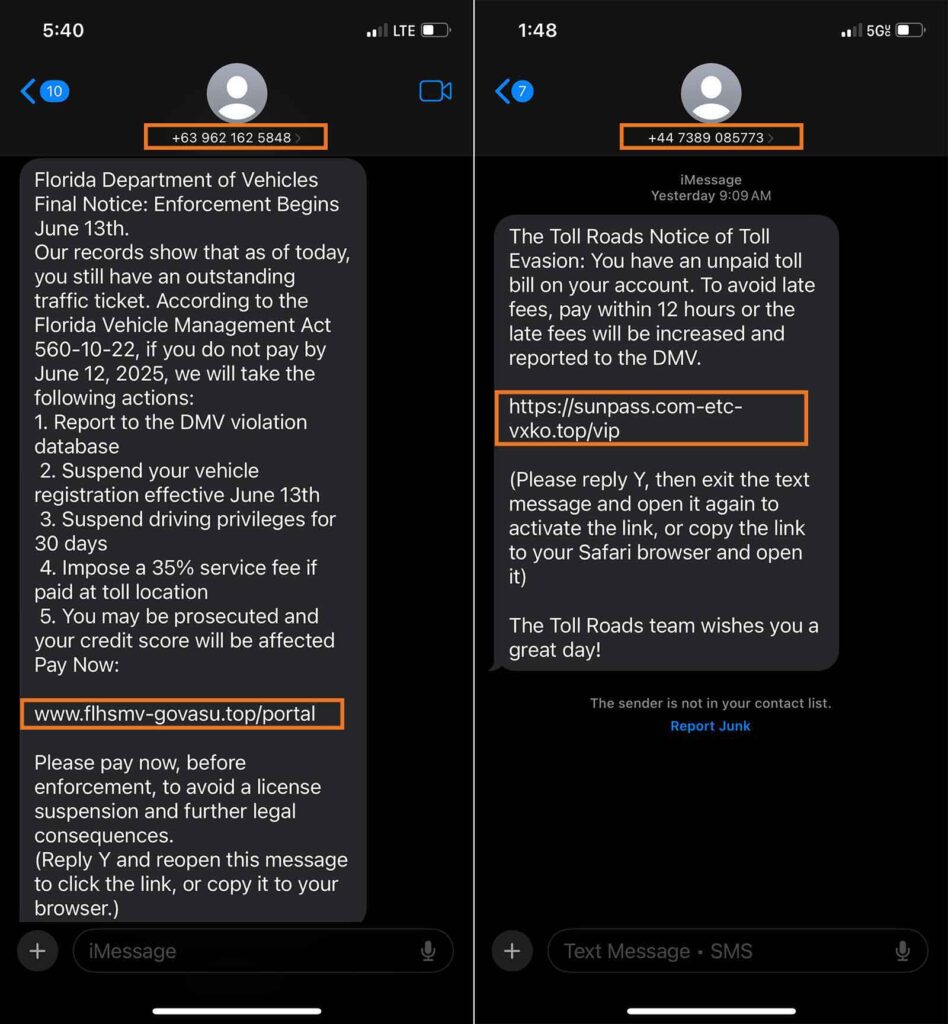
- Those annoying fake road toll scams you keep getting? They cost U.S. victims nearly $130k in reported losses in 2024 alone. (Source: FBI IC3’s 2024 Internet Crime Report)
Social Engineering Statistics: A Look at the Frequency of These Attacks
- The number of phishing attacks decreased by 20% globally in 2024. However, these attacks are becoming increasingly targeted and hyper-focused as bad guys shift to voice and video to avoid email security measures. (Source: Zscaler’s ThreatLabz 2025 Phishing Report)
- Phishing attacks targeting the United States dropped nearly 32% in 2024. However, the country still firmly ranks #1. (Source: Zscaler’s ThreatLabz 2025 Phishing Report)
- Social engineering attacks represent 22% of data breaches involving external threat actors specifically. Of those, phishing accounted for 57%. (Source: Verizon’s 2025 Data Breach Investigations Report [DBIR])
- Phishing and spoofing attacks rank #1, accounting for nearly 23% of all the cyber crime complaints reported to the FBI’s IC3 in 2024 alone. That’s 193,407 of the 859,532 complaints, which is bad on its own but even worse when you consider that’s just the number of reported complaints — it doesn’t account for the crimes that have gone unreported. (Source: FBI IC3 2024 Internet Crime Report)
- FBI’s IC3 receives 100+ reports of scammers impersonating the cyber crime-fighting agency. (Source: FBI IC3 2024 Internet Crime Report)
- Small businesses are targeted nearly 4x as often as their larger counterparts. (Source: Verizon’s 2025 Data Breach Investigations Report)
- Fake road toll scams have skyrocketed 2900% from 2,000 scams reported in 2023 to 60,000 in 2024. (Source: FBI IC3 2024 Internet Crime Report)
- The “human factor” still reigns supreme as a factor in 60% of data breaches. According to Verizon’s 2025 DBIR report, “breaches involving humans were responsible for the majority of cases we received.” (Source: Verizon’s 2025 Data Breach Investigations Report)
- ~20% of businesses report experiencing one or more ATO incidents per month. These attacks often involve attackers using social engineering tactics to phish account holders for information or steal credentials. (Source: Barracuda’s 2025 Email Threats Report)

Social Engineering Statistics: Taking a Closer Look at Attackers’ Methods
So, how do bad guys do what they do?
- The detection of voice phishing attacks, paired with social engineering tactics, increased by a whopping 442% from 1H to 2H of 2024. According to CrowdStrike’s researchers: “Various eCrime adversaries are increasingly adopting vishing, callback phishing, and help desk social engineering attacks to gain a foothold into networks.” (Source: CrowdStrike 2025 Global Threat Report)
- ~25% of state-sponsored social engineering campaigns begin with idle conversations. (Source: Proofpoint The Human Factor 2025, Vol. 1: Social Engineering)
- One in five phishing emails relies solely on social engineering. (Source: KnowBe4’s Phishing Threat Trends Report)
- One crypto startup founder suspects that around 95% of the job applications he receives for legitimate positions in his firm come from North Korean operatives pretending to be American IT workers. (Source: Fortune’s article “North Korean IT Workers Infiltrating Fortune 500 Companies.”)
- A woman in Arizona used 60 stolen identities to help North Korean IT workers fraudulently get jobs at 300 companies. This netted millions of dollars for the North Korean government. (Source: Fortune’s article “North Korean IT Workers Infiltrating Fortune 500 Companies.”)
- 90%+ of pure social engineering advanced persistent threat (APT) campaigns use collaboration as their “in” to get targets to cooperate. (Source: Proofpoint The Human Factor 2025, Vol. 1: Social Engineering)
- 39% of cloud initial assets had email phishing as the initial infection vector. Another 12% was split between SIM swapping and voice phishing, both of which attacks often rely on social engineering tactics. (Source: Mandiant M-Trends 2025 Report)
- 220,000+ people are trafficked in South-East Asia and forced to work in online scam farms, where they often carry out social engineering attacks. (Source: WEF Global Cybersecurity Outlook 2025 report)
- Bad guys can exploit gaps in email security, as nearly half of organizations don’t have a configured DMARC policy in place. This leaves legitimate organizations at risk of being impersonated by cybercriminals who can spoof their sender domain. (Source: Barracuda’s 2025 Email Threats Report)

Social Engineering Statistics: Crime in the Age of Generative AI & LLMs
Generative AI (genAI) and language learning model (LLMs) are now taking social engineering attacks to a whole new level. Messages that previously required time and resources to meticulously hone can now be generated at near rapid-fire speed.
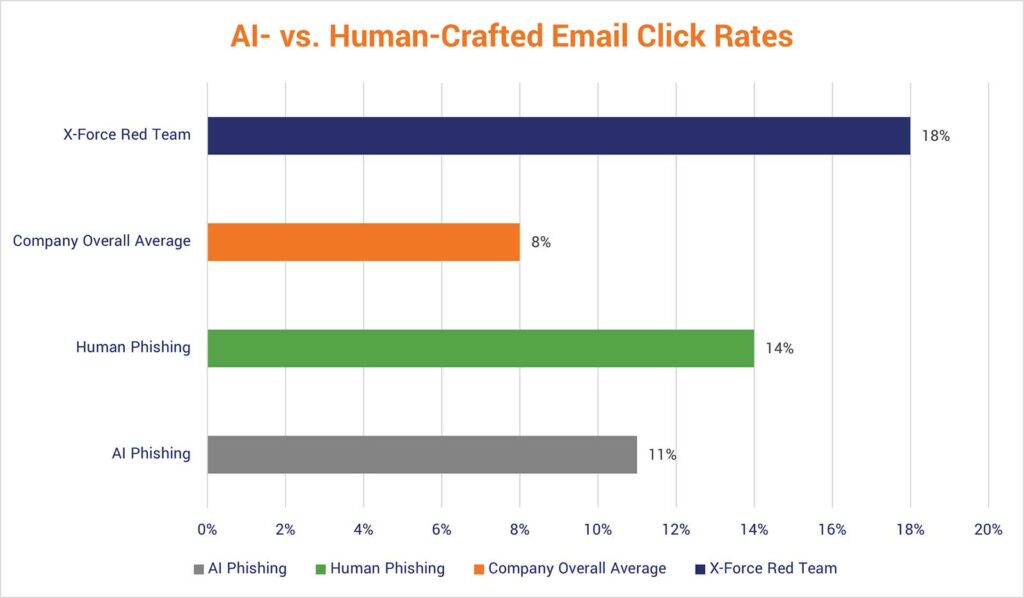
- In 2023, a genAI tool was able to craft an effective phishing email using five simple prompts in just 5 minutes. Compare this to the 16+ hours on average that IBM’s X-Force team says it takes their seasoned social engineers to research in depth and write the message for the intended target. Imagine how much faster genAI tools have likely become over the past two years… (IBM’s AI vs. Human Deceit: Unravelling the New Age of Phishing Tactics)
- What makes matters worse is that three in five of these organizations indicate that they’ve sustained successful ATO attacks. (Source: Proofpoint Research: 2024 Account Takeover Statistics)
- Phishing emails generated entirely by AI outperformed the control group by 42%. AI-generated emails with “human-in-the-loop” expert interventions performed even better, having a click-through rate of 56%. (Source: “Evaluating Large Language Models’ Capability to launch Fully Automated Spear Phishing Campaigns: Validated on Human Subjects” by Heiding, Lermen, Kao, Schneier, and Vishwanath)
- Nearly half (47%) of organizations indicate that genAI-based threats are their biggest concern. (Source: World Economic Forum’s [WEF] Global Cybersecurity Outlook 2025 Insight Report)
- 99% of Proofpoint’s monitored customers were the targets of account takeover attacks in 2024. (Source: Proofpoint Research: 2024 Account Takeover Statistics)
Editor’s Note: This blog post was published originally by Casey Crane on Jan. 13, 2023. It was updated and republished by the same author with new content and the industry’s latest social engineering statistics data on June 20, 2025.












































 (6 votes, average: 4.33 out of 5, rated)
(6 votes, average: 4.33 out of 5, rated)






5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown