Google Restricts GeoLocation to HTTPS in Chrome Version 50
Geolocation only available over HTTPS in Chrome 50.
With the release of Chrome v50, the Geolocation API has officially been restricted to HTTPS-only. What does this mean? If you want your website to be able to request the user’s location over the internet, you need to serve your site over HTTPS.
Attempting to get the user’s location over HTTP will simply fail. The user will not ever know you wanted to request their location (unless they happen to have the developer console open).
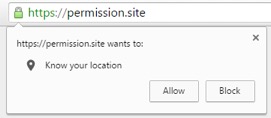
Remember that using Geolocation results in a permissions prompt. Adding HTTPS support to your site does not automatically give you permission to get the user’s location. They still get to choose to allow or block that information.
For any developers who may be panicking about testing or prototyping: Don’t worry! HTTPS is not the only secure origin. Anything done on localhost is also considered secure origins (for a full list of secure origins click here).
Powerful Features & Secure Origins
This is part of a bigger campaign by Google Chrome’s Security team known as “Deprecating Powerful Features on Insecure Origins”. That’s a mouthful, huh? In plain language, this means that connections which cannot be trusted will not have full access to certain browser functionality.
These “powerful features” either handle sensitive user data (personally-identifiable information, user credentials, payment information, etc), or make changes to the user’s experience that should only be done over secure (and authenticated) connections. This set of features includes: device motion / orientation, geolocation, and accessing the user’s camera and microphone).
So far, only Geolocation and getUserMedia (access to webcam / microphone) have been given the HTTPS-only treatment. We put together a handy chart (look below) showing the features slated to go secure origins-only for reference.
Google Chrome’s Security team continually evaluates the real-world use and posts warnings to their blink-dev mailing list before removing any features, which makes predicting difficult. But if you are on the lookout you should never be left in the dark.
| Feature | HTTPS Only? |
| Device motion / orientation
|
Not yet |
| Encrypted Media Extensions (EME)
|
Not yet |
| Fullscreen
|
Not yet |
| Geolocation
|
Yes (Chrome 50) |
| getUserMedia (access to users’s camera and microphone) |
Yes (Chrome 47) |
| AppCache
|
Not yet |




































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)














5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown