How to Install a Chrome Extension From Github
Manually Install a Chrome Extension in a Minute
Whether you’ve never manually installed a Chrome extension before, or Github’s layout feels like a foreign land to you, this guide will help you quickly download and install a Chrome extension from Github.com.
Before we get to the guide, we want to make a quick note about security risks:
Security Risks
Chrome extensions can have a lot of access to your data – including the ability to read and change all data on every page you visit. Normally you install extensions through Chrome’s Web Store, where they can be scanned for malicious behavior. But anyone can write and upload an extension to Github, and there are no checks to make sure the extension is safe to use or does what it says.
Be aware of this risk before installing any random extension you happen to find.
How to Install a Chrome Extension From Github:
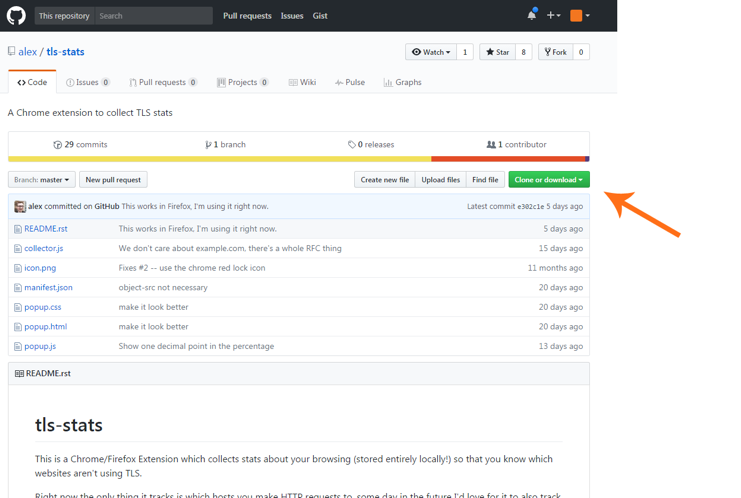
- The first step is to download the extension from its repository page on Github. To give this guide context, we will download and install tls-stats by Alex Gaynor. This extension keeps a local history of the sites you visit most often over HTTP – allowing you to take a look back at the most common pages you browse insecurely.
The tls-stats repository page.
Once you are on the repository page, look for the green “Clone or download” button on the right-hand side of the page.
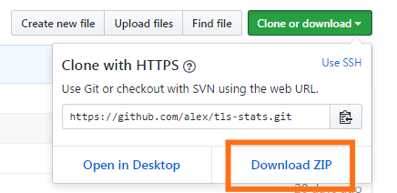
- Click the “Clone or download” button and then click “Download ZIP.”
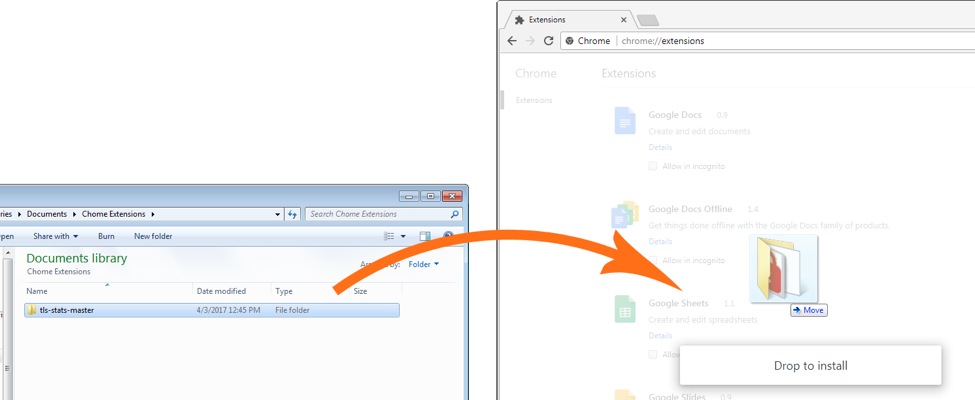
- Take the downloaded ZIP file and extract it. We need to give it a permanent home because Chrome will externally load the files (if they get moved/deleted then the extension will stop working).
- With the extension downloaded and extracted, we can now install it.In Chrome, navigate to chrome://extensions
- Installing the extension is extremely easy. All we need to do is drag-and-drop the folder we extracted onto Chrome’s Extensions page.If the extension is in the “.crx” format, Chrome will ask you to review and approve the permissions before installing.
- The extension is installed! We will now see it in the list of our extensions, and it’s icon (if it has one) will be in the Chrome menu. That’s it! Super painless
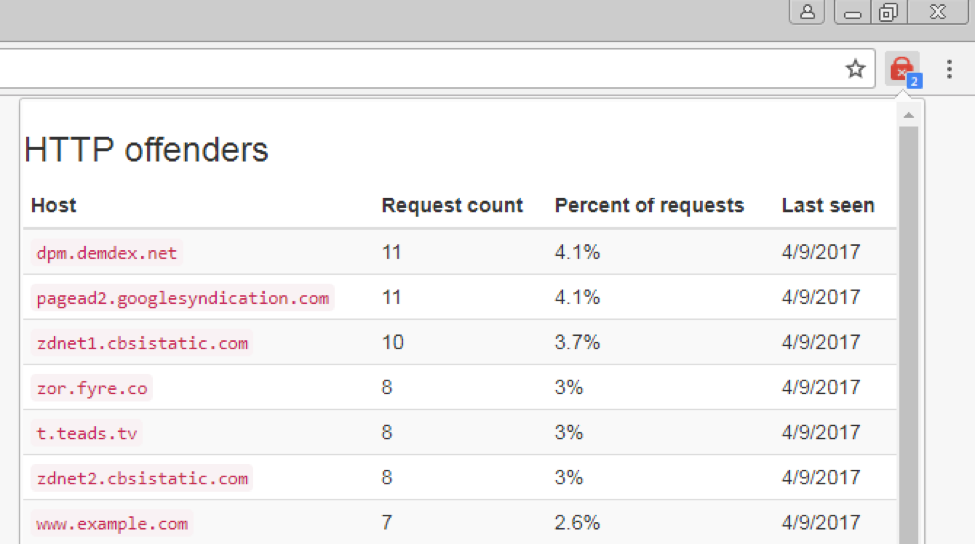
Now you can start using the extension. In our example, tls-stats will now start recording the domains you access over HTTP. As you browse over the next few days and weeks, click on its icon in the Chrome menu to see your worst HTTP-offenders.
You will be surprised by how many requests are made over HTTP, especially on ad-heavy sites which make lots of calls to other origins in the background. The number in the blue square tells you how many new HTTP requests have been recorded since you last clicked the icon.
Note that when you install an extension this way, Chrome will always ask you about disabling developer mode when you open the first new window. Just click “Cancel” to ignore the message and keep the extensions operating.
If you become concerned that the extension is malicious or not doing what is expected, you can click “Disable,” which will immediately turn off all extensions you installed manually through this method. You can visit chrome://extensions/ again to entirely delete the unwanted extensions and re-enable the ones you want to keep.
What extension did you install with this guide? Did you have any problems or questions? Leave a comment below and I am happy to help out.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown