SSL Certificates – Best Way to Go for Web Security
In the recent years we have seen an explosion in cyber espionage across the world. Obama’s national security adviser said in remarks before the Asia Society in New York City: “Increasingly, U.S. businesses are speaking out about their serious concerns about sophisticated, targeted theft of confidential business information and proprietary technologies through cyber intrusions emanating from China on an unprecedented scale. The international community cannot tolerate such activity from any country” (Tom Donilon, National Security Advisor).

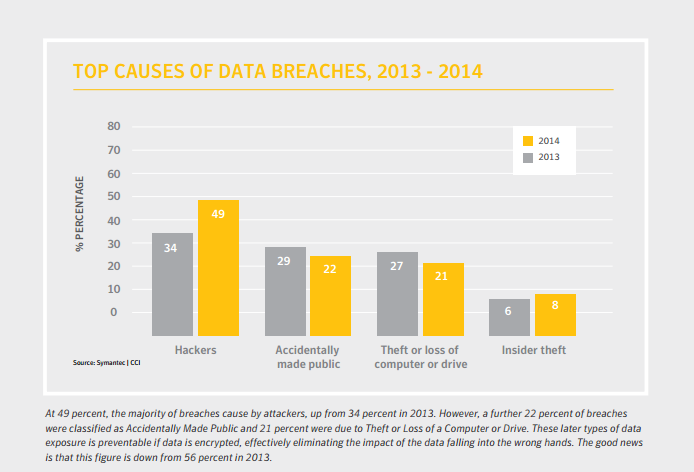
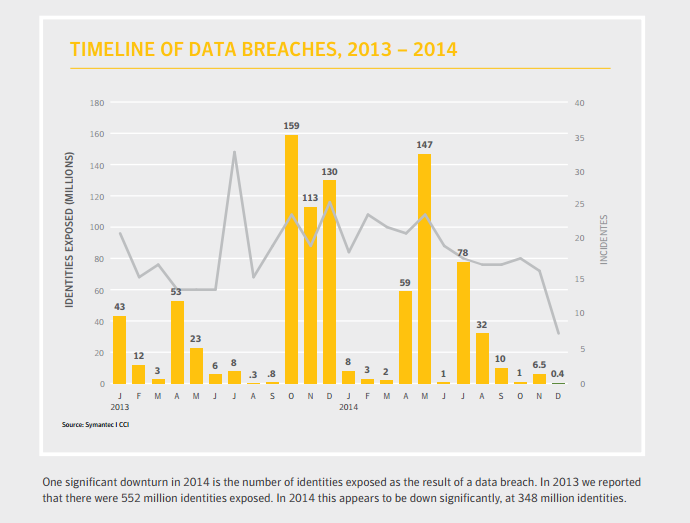
Spam, phishing, and malware are major web security threats that continue to wreak havoc and ruin people’s lives across the world. Hackers are targeting organizations such as aerospace, IT, Governments, satellites and telecommunications, scientific research, energy, transportation, and other business sectors. They are stealing a wide range of information; including credit cards, social security numbers, manufacturing procedures, and business plans. These hackers are draining companies of their competitive advantage and intellectual property rights. In 2014 alone, bugs like Heartbleed, Poodle, and Shellshock effected millions of people worldwide. Luckily these bugs have been fixed and new SSL hashing algorithms and ciphers have been put in place to stop the hackers from getting your information. Take a look at the graphs below to see how many people’s identities have been exposed. The number will shock you!
2014 Data Breaches Analysis:
One of the best examples of cyber espionage is an American Bank: JPMorgan Chase, who acknowledged the data breach related to 83 million total accounts. 76 million were households and around 7 million small business were affected by one of the biggest data breaches in history.
Health Care Industries – New Target:
As healthcare technology is improving, the industry has adapted new ways to maintain data electronically in the cloud. With this technology comes along many new security risks and new loopholes. Hackers are targeting medical information of patients. There have many cases of medical and health insurance fraud. Hackers are targeting “Personal Identifiable Information” or PII, as well as “Protected Health Information”, PHI. Cybercriminals use this information to receive government identification numbers, details regarding bank accounts and credit cards, information of insurance plans, medical history and much more. This type of data can be misused in several ways like obtaining visas or passports, or other identification documents which can ultimately cause big harm to recover your identity.
Social Media as the Next Target:
Social media sites are also the main targets when it comes to cyber-attacks. Hackers target email scams, spamming, account hacking, and social engineering. They also attack mega social media sites like Facebook, Pinterest and Twitter. Hackers will post links on the users account, then other users will click on the link which then forwards to a dangerous malicious site. As web security technology is advancing, so are the hackers. Therefore companies should be using the latest web security standards and protocols as well as educating employees.
SSL, the Game Changer:
Regardless of vulnerabilities and loop holes faced during 2014, SSL remains a crucial web security product to provide top notch security. In 2014, the SSL protocol migrated to the SHA2 hashing algorithm which made the certificate stronger than ever. Almost all Certificate Authorities have moved to SHA-2 as their default hashing algorithm. Tech giants Google and Microsoft announced depreciation of SHA-1 Certificates by the end of 2016. So it’s wise to move to SHA-2 as soon as you can. Technology is constantly advancing and ECC algorithms are coming to market which are cryptographically stronger and faster compared to RSA as well as ECC is supported by all major browsers, and mobile phones with latest platforms.
The SSL Store™ has the web security product you need. Whether it’s a code signing or SSL Certificate we got your back. We are Platinum Partners with leading brands Symantec, GeoTrust, RapidSSL, Thawte, Comodo and Certum. The Digital security certificates we offer, are the same ones which are sold directly by the Certificate Authority. With us, you will get the benefit of affordable price, because we purchase in large quantities with highly discounted price. Due to bulk purchases, we can easily forward the benefit of discount to our resellers and clients. Apart from that, you will get the best customer service and technical support offered within the industry. Our expert web security specialists are quirky, and fun to work with. Our Customer Experience Team provides 24×7 support. Our goal is to make sure you have a painless experience getting your SSL or Code Singing Certificate. Take advantage of the power of SSL and keep your site and business protected!





































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)











5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown