What is Server Name Indication (SNI)?
SNI: Running multiple SSL certificates on the same IP Address
What is SNI? Server Name Indication is a crucial component of SSL that oftentimes goes under the radar. SNI is what allows multiple websites to exist on the same IP address. Without SNI, each hostname would require its own IP address in order for an SSL certificate to be installed. However, SNI solves this problem.
Now, what does all that mean?
Let’s Hash it Out.
Why Name-Based Hosts Don’t Work Well with SSL
Back in the olden days, which in internet years means 2007, you would solve the issue of multiple websites being hosted on same IP address with name-based hosts. Basically, when a client requests a particular website, it uses a unique HTTP header that includes the intended hostname. In response, the server matches this header to the intended website and transports the user there.
Where this breaks down is when HTTPS enters the picture. That’s because SSL requires an SSL handshake before an encrypted connection can be made between a client and a server. The HTTP header that contained the intended hostname wouldn’t be downloaded until after the handshake has been completed, which means that the server wouldn’t know which website to make the connection to.
What is SNI?
Server Name Indication is an extension to the SSL/TLS protocol that allows multiple SSL certificates to be hosted on a single IP address. The way SNI does this is by inserting the HTTP header into the SSL handshake. Because the server can see the intended hostname during the handshake, it can connect the client to the requested website.
Before Server Name Indication was created, each website that you wanted to encrypt had to have a unique IP address. This proved incredibly costly. It also had the unintended side effect of rapidly consuming IPv4 IP addresses.
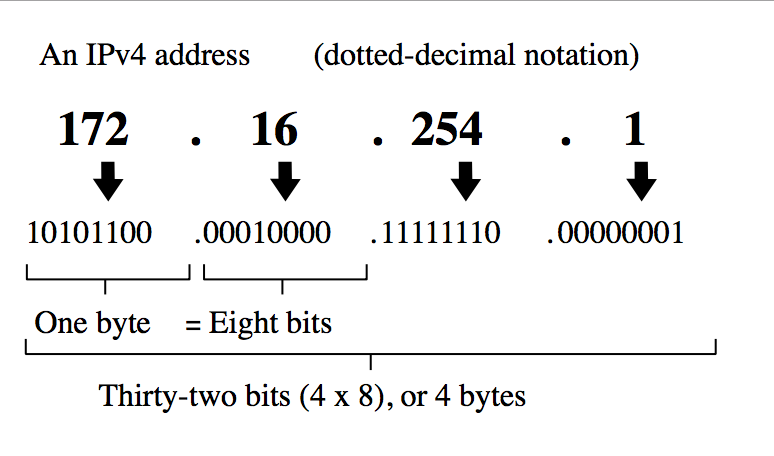
Let’s not go too far into the weeds here, but there are a finite number of IP addresses. IPv4 or Internet Protocol version 4, assigns addresses to each device participating in a computer network that uses the Internet Protocol for communication. An IPv4 IP address looks like this:
There are only around 4 billion IPv4 IP addresses. Eventually, all 4 billion+ addresses WILL be depleted. But before SNI, they were going a lot faster. Server Name Indication helped to stave off that eventual depletion a little longer.
Eventually, the internet will migrate to IPv6 IP addresses. There are potentially 340 undecillion IPv6 addresses—so that list should last a little longer.
What does the future hold for SNI?
The biggest concern over SNI was its scalability. At the outset, some believed that web browsers and servers wouldn’t adopt the technology fast enough. That concern proved to be largely unfounded though. Today, according to Akamai, almost 98% of the clients requesting an HTTPS-enabled site support SNI.
RELATED: What is HSTS?
What we Hashed Out (for skimmers)
Here’s what we covered in today’s discussion:
- What is SNI? Server Name Indication allows multiple SSL certificates to be hosted on a single IP address
- SNI inserts the HTTP header into the SSL handshake to inform the server which website to connect to
- Today, 98% of clients requesting HTTPS support SNI




















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown