Advanced Encryption Standard (AES): What It Is and How It Works
Understanding advanced encryption standard on basic level doesn’t require a higher degree in computer science or Matrix-level consciousness — let’s break AES encryption down into layman’s terms
Hey, all. We know of security of information to be a hot topic since, well, forever. We entrust our personal and sensitive information to lots of major entities and still have problems with data breaches, data leaks, etc. Some of this happens because of security protocols in networking, or bad practices of authentication management — but, really, there are many ways that data breaches can occur. However, the actual process of decrypting a ciphertext without a key is far more difficult. For that, we can thank the encrypting algorithms — like the popular advanced encryption standard — and the secure keys that scramble our data into indecipherable gibberish.
Let’s look into how AES works and different applications for it. We’ll be getting a little into some Matrix-based math — so, grab your red pills and see how far this rabbit hole goes.
Let’s hash it out.
What is AES (Advanced Encryption Standard) Encryption?
You may have heard of advanced encryption standard, or AES for short but may not know the answer to the question “what is AES?” Here are four things you need to know about AES:
- What’s behind the name? AES is a variant of the Rijndael family of symmetric block cipher algorithms, which is a combination of two Belgian cryptographers’ names, Joan Daemen and Vincent Rijmen. (It’s sort of like those combo celebrity names like “Brangelina” and “Kimye”).
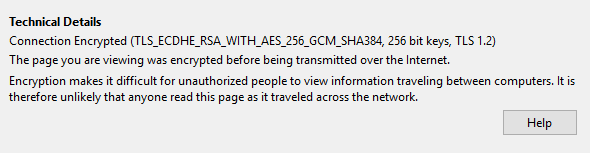
- Where is AES used? AES encryption is commonly used in a lot of ways, including wireless security, processor security, file encryption, and SSL/TLS. In fact, your web browser probably used AES to encrypt your connection with this website:
- Why is AES so popular? AES has proved to be very effective and efficient and, given the correct key, adds little to no-noticeable difference in overhead for any process where it is utilized. Essentially, AES is a fast and highly secure form of encryption that is a favorite of businesses and governments worldwide.
- How secure is AES? With a 256-bit encryption key, AES is very secure — virtually unbreakable. (More on that in just minute.)
Why Advanced Encryption Standard Is the Standard
The National Institute of Standards and Technology (NIST) established AES as an encryption standard nearly 20 years ago to replace the aging data encryption standard (DES). After all, AES encryption keys can go up to 256 bits, whereas DES stopped at just 56 bits. NIST could have chosen a cipher that offered greater security, but the tradeoff would have required greater overhead that wouldn’t be practical. So, they went with one that had great all-around performance and security.
AES’s results are so successful that many entities and agencies have approved it and utilize it for encrypting sensitive information. The National Security Agency (NSA), as well as other governmental bodies, utilize AES encryption and keys to protect classified or other sensitive information. Furthermore, AES is often included in commercial based products, including but limited to:
- Wi-Fi (can be used as part of WPA2)
- Mobile apps (such as WhatsApp and LastPass)
- Native Processor Support
- Libraries in many software development languages
- VPN Implementations
- Operating system components such as file systems
How Strong Is Advanced Encryption Standard? A 256-Bit Key Takes Virtually Forever to Crack
Although it wouldn’t literally take forever, it would take far longer than any of our lifetimes to crack an AES 256-bit encryption key using modern computing technology. This is from a brute force standpoint, as in trying every combination until we hear the “click”/unlocking sound.
Just how long would it take? We are venturing into “a thousand monkeys working on a thousand typewriters to write ‘A Tale of Two Cities’” territory. The possible combinations for AES 256-bit encryption is 2256. Even if a computer can do multiple quadrillions of instructions per second, then we are still in that “eagles’-wings-eroding-Mount-Everest” time frame.
Needless to say, it’s waaaaaaaaaaaaaaaaaaay (there’s not enough memory on our computers to support the number of “a” letters that I want to convey) longer than our current universe has been in existence. And that’s just for a 16-byte block of data. So, as you can see, brute forcing AES — even if it is 128 bits AES — is futile.
That would likely change, though, once quantum computing becomes a little more mainstream, available, and effective. Quantum computing is expected to break AES encryption and require other methods to protect our data — but that’s still a ways down the road.
How Does AES Work? A Look at Cipher Blocks and Keys
To better understand what AES is, you need to understand how it works. But in order to see how the advanced encryption standard actually works, however, we first need to look at how this is set up and the “rules” concerning the process based on the user’s selection of encryption strength. Typically, when we discuss using higher bit levels of security, we’re looking at things that are more secure and more difficult to break or hack. While the data blocks are broken up into 128 bits, the key size have a few varying lengths: 128 bits, 196 bits, and 256 bits. What does this mean? Let’s back it up for a second here.
We know that encryption typically deals in the scrambling of information into something unreadable and an associated key to decrypt the scramble. AES scramble procedures use four scrambling operations in rounds, meaning that it will perform the operations, and then repeat the process based off of the previous round’s results X number of times. Simplistically, if we put in X and get out Y, that would be one round. We would then put Y through the paces and get out Z for round 2. Rinse and repeat until we have completed the specified number of rounds.
The AES key size, specified above, will determine the number of rounds that the procedure will execute. For example:
- A 128-bit AES encryption key will have 10 rounds.
- A 192-bit AES encryption key will have 12 rounds.
- A 256-bit AES encryption key will have 14 rounds.
As mentioned, each round has four operations.
How to Read the Data
So, you’ve arrived this far. Now, you may be asking: why, oh why, didn’t I take the blue pill?
Before we get to the operational parts of advanced encryption standard, let’s look at how the data is structured. What we mean is that the data that the operations are performed upon is not left-to-right sequential as we normally think of it. It’s stacked in a 4×4 matrix of 128 bits (16 bytes) per block in an array that’s known as a “state.” A state looks something like this:
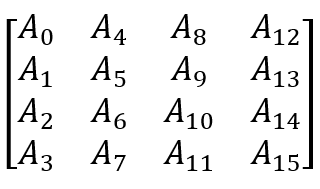
So, if your message was “blue pill or red,” it would look something like this:
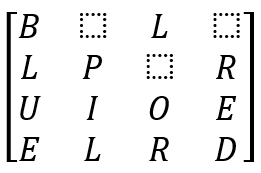
So, just to be clear, this is just a 16-byte block — so, this means that every group of 16 bytes in a file are arranged in such a fashion. At this point, the systematic scramble begins through the application of each AES encryption operation.
What the 4 AES Encryption Operations Are and How They Work
As mentioned earlier, once we have our data arrangement, there are certain linked operations that will perform the scramble on each state. The purpose here is to convert the plaintext data into ciphertext through the use of a secret key.
The four types of AES operations as follows (note: we’ll get into the order of the operations in the next section):
1. Key Expansion and AddRoundKey
As mentioned earlier, the key size determines the number of rounds of scrambling that will be performed. AES encryption uses the Rjindael Key Schedule, which derives the subkeys from the main key to perform the Key Expansion.
The AddRoundKey operation takes the current state of the data and executes the XOR Boolean operation against the current round subkey. XOR means “Exclusively Or,” which will yield a result of true if the inputs differ (e.g. one input must be 1 and the other input must be 0 to be true). There will be a unique subkey per round, plus one more (which will run at the end).
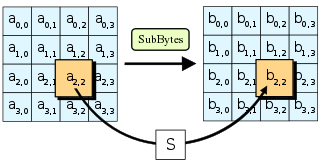
2. SubBytes
The SubBytes operation, which stands for substitute bytes, will take the 16-byte block and run it through an S-Box (substitution box) to produce an alternate value. Simply put, the operation will take a value and then replace it by spitting out another value.
The actual S-Box operation is a complicated process, but just know that it’s nearly impossible to decipher with conventional computing. Coupled with the rest of AES operations, it will do its job to effectively scramble and obfuscate the source data. The “S” in the white box in the image above represents the complex lookup table for the S-Box.
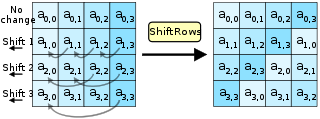
3. ShiftRows
The ShiftRows operation is a little more straightforward and is easier to understand. Based off the arrangement of the data, the idea of ShiftRows is to move the positions of the data in their respective rows with wrapping. Remember, the data is arranged in a stacked arrangement and not left to right like most of us are used to reading. The image provided helps to visualize this operation.
The first row goes unchanged. The second row shifts the bytes to the left by one position with row wrap around. The third row shifts the bytes one position beyond that, moving the byte to the left by a total of two positions with row wrap around. Likewise, this means that the fourth row shifts the bytes to the left by a total of three positions with row wrap around.
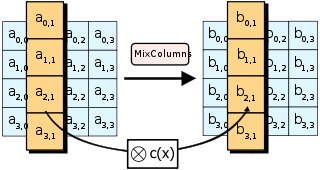
4. MixColumns
The MixColumns operation, in a nutshell, is a linear transformation of the columns of the dataset. It uses matrix multiplication and bitwise XOR addition to output the results. The column data, which can be represented as a 4×1 matrix, will be multiplied against a 4×4 matrix in a format called the Gallois field, and set as an inverse of input and output. That will look something like the following:
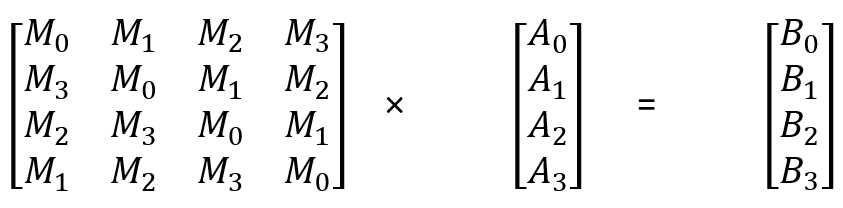
As you can see, there are four bytes in that are ran against a 4×4 matrix. In this case, matrix multiplication has each input byte affecting each output byte and, obviously, yields the same size.
Order of the Operations
Now that we have a decent understanding of the different operations utilized to scramble our data via AES encryption, we can look at the order in which these operations execute. It will be as such:
- Key Expansion sets the round key list which is used on each round plus an additional (and initial, as you’ll see) round.
- AddRound is the first step to obfuscate the data. Immediately, we have scrambled data.
- Now we get into the rounds of intense data scrambling. Again, depending on the selected cipher bit, the number of rounds will differ.
- For 9, 11, or 13 rounds, depending on the cipher bit selection, the following will be performed in such order:
- SubBytes
- ShiftRows
- MixColumns
- AddRound
- At the 10th, 12th, or 14th round, respectively, we perform the final set of operations, which are as follows:
- SubBytes
- ShiftRows
- AddRound
Note: The MixColumns operation is not in the final round. Without getting into the actual math of this, there’s no additional benefit to performing this operation. In fact, doing so would simply make the decryption process a bit more taxing in terms of overhead.
If we consider the number of rounds and the operations per round that are involved, by the end of it, you should have a nice scrambled block. And that is only a 16-byte block. Consider how much information that equates to in the big picture. It’s miniscule when compared to today’s file/packet sizes! So, if each 16-byte block has seemingly no discernable pattern — at least, any pattern that can be deciphered in a timely manner — I’d say AES has done its job.
Final Thoughts on Advanced Encryption Standard Ciphers and Keys
We know the advanced encryption standard algorithm itself is quite effective, but its level of effectiveness depends on how it’s implemented. Unlike the brute force attacks mentioned above, effective attacks are typically launched on the implementation and not on the algorithm itself. This can be equated to attacking users — as in phishing attacks — versus attacking the technology behind the service/function that may be hard to breach. These can be considered side-channel attacks where the attacks are being carried out on other aspects of the entire process and not the focal point of the security implementation.
While I always advocate going with a reasonable/effective security option, a lot of AES encryption is happening without you even knowing it. It’s locking down spots of the computing world that would otherwise be wide open. In other words, there would be many more opportunities for hackers to capture data if advanced encryption standard wasn’t implemented at all. We just need to know how to identify the open holes and figure out how to plug them. Some may be able to use AES and others may need another protocol or process.
Appreciate the encryption implementations we have, use the best ones when needed, and happy scrutinizing!





































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)







 (3 votes, average: 3.67 out of 5, rated)
(3 votes, average: 3.67 out of 5, rated)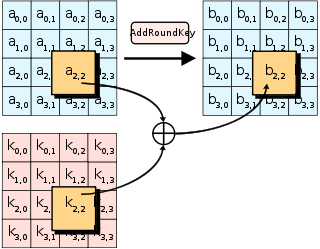







5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown