Wait – Some People Still Aren’t Using Always-on SSL?
Always-on SSL, Default SSL – whatever you call it, you should be using it.
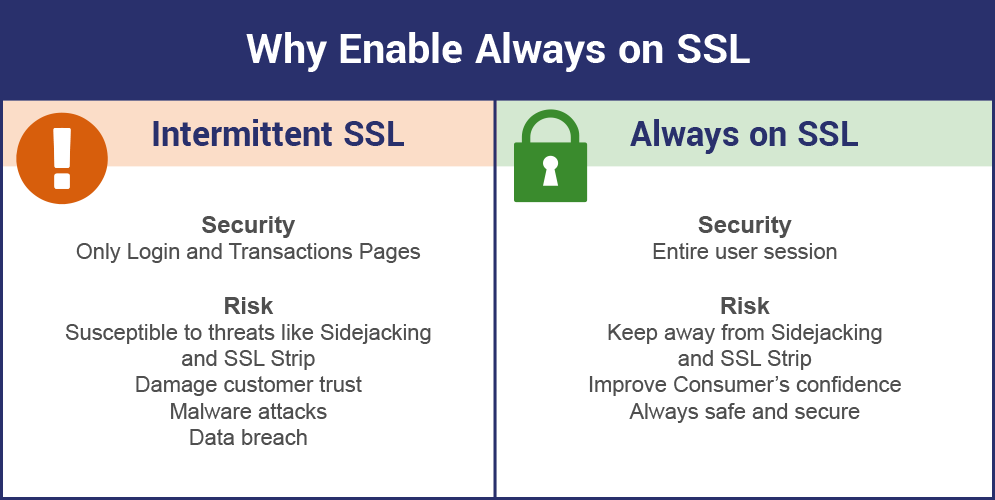
Here’s a free bit of advice: if you have an SSL certificate make sure it’s deployed across your entire website, this is sometimes called “Always-on SSL” or “Default SSL.” And while it may seem obvious to some, you would be surprised how many websites still serve pages over HTTP, despite having SSL installed.
Now, unlike my former colleague, Vince, I don’t actually lose any sleep over this. But it does perplex me quite a bit when I’m awake. It’s like baking a cake but only icing certain pieces. You’ve got that whole tub of White frosting right there—why aren’t you getting the most out of it?
Ok, so maybe my culinary metaphor doesn’t really hold up, but you get the point I’m making. You’re paying the same amount for an SSL certificate regardless of whether you use it to encrypt one page on your website or all of them. Why not encrypt all of them?
There is no reason not to have Always-on SSL
In the past, there have been arguments made as to why having your SSL certificate encrypt your entire website could cause performance issues. I’m here to tell you, that got worked out a long time ago.
Now, there are numerous examples of how serving a website over HTTPS is actually faster than via HTTP. And with the release of HTTP/2 in 2015 – remember, HTTP/2 requires secure connections – HTTPS has only gotten faster. So if you’re still covering your lack of Always-on SSL with the old performance issues argument, it may be time to rethink.
Why do I need HTTPS on every page?
For starters, as of 2017 the browsers – Chrome, Firefox, Safari and Edge/IE – are beginning to warn users when they visit pages without encryption. Google has been the strongest in its attempts to mandate encryption, even going so far as to label websites without SSL “Not Secure.”
In the coming months, other are expected to follow suit.
So obviously, there’s the impact having any part of your website labeled “Not Secure” can cause on your traffic and bounce rate. And then there’s also the SEO angle. As of 2016, some experts were suggesting that SSL could add as much as a 5% boost to a website’s search rankings. Frankly, I’ve always thought that number sounded a little high, but the logic behind it is sound.
Think about it: a search engine’s job is to deliver its users to the best possible result. Well, all things considered equal, if one page is decidedly more secure than another—that’s an advantage. It would make sense search engines would reward pages that are more secure than their competitors. That provides a better experience to the search engine’s users.
Related: Google says move your entire website to HTTPS at once
A Holistic Approach to Security
Think of your website’s security as an immune system, you wouldn’t take steps that would undercut your own immune system—would you? Because that’s what you’re doing when you piecemeal SSL on your site, choosing only to encrypt certain sections while leaving others over HTTP.
For starters, bouncing back and forth between encrypted and unencrypted connections taxes your servers—especially if you’re employing perfect forward secrecy, which requires a new handshake and session key every time a secure connection is terminated. You’re also potentially opening new attack vectors as hackers can try downgrade attacks and a whole new range of options aimed at stripping away SSL’s protections.
And then there’s also just consideration for your customers and visitors. Bouncing back and forth between encrypted and unencrypted pages can be annoying, it makes it easier for ISPs and third parties to track movement across pages and it just generally makes your website more vulnerable.
A Final Word about Always-on SSL
The entire internet wants you to be encrypted. Not just your homepage or your checkout page or pages with text fields—everything. Google will not be satisfied until your whole website is encrypted. Every page, every image, every asset.
Besides, why have an SSL certificate if you’re not going to use it like it’s supposed to be? SSL certificates are meant to encrypt your entire website, not just parts of it. So remember to let it do its thing. Always-on SSL, Default SSL, HTTPS Everywhere—whatever you call it, just make sure you’re using it.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown