Everything You Need to Know About ARP Spoofing
ARP Spoofing Attacks Lets Hackers Impersonate Your PC and Steal All Your Traffic
It’s a common trope in spy movies. You’re happily watching, popcorn in hand, when suddenly a character does something completely unexpected and unlike them. You’re in shock. You ask yourself “What just happened? I thought they were both good guys? Why did he shoot that other guy?!” Then, you’re hit with the plot twist – it turns out the bad guy was wearing a mask the whole time and impersonating another to achieve his nefarious goals! In the cybersecurity world however, the “bad guy in a disguise” is a great illustration of how ARP spoofing attacks work.

ARP spoofing occurs when an attacker manipulates the relationship between Media Access Control (MAC) addresses and Internet Protocol (IP) addresses. The end is result is that they appear to be someone else to all the other devices on your network (and thus they receive all the traffic meant for the real user). The ramifications can be severe, as ARP spoofing attacks can lead to not only the theft of your data, but session hijacking, distributed denial of service (DDoS) attacks, and more.
So, what is ARP in the first place? How does ARP spoofing work? How can you detect it? And most importantly, how can you prevent it?
Let’s hash it out.
What is ARP?
To fully understand what ARP spoofing is and how it works, we first need to know what ARP itself is. It stands for Address Resolution Protocol, and its primary function is to resolve internet layer addresses into link layer addresses. Another way to think of ARP is that it translates MAC addresses to Internet Protocol addresses (and vice-versa).
Basically, ARP is how your devices are able to contact the router or gateway and ultimately connect to the internet. Hosts keep a mapping table, also known as an ARP cache, that gets called on when an IP packet is sent between hosts on a local network. It’s basically a cross-reference between MAC addresses and IP addresses, and it facilitates connections between different destinations on the network.
If the MAC address of a certain IP is unknown to the host, then a broadcast packet gets transmitted (also referred to as an ARP request). The machine that has the IP address found in the ARP request then replies with their MAC address. Then, it gets added to the ARP cache in case there are more requests from the same machine.
Security in ARP
Unfortunately, ARP wasn’t created with security in mind. ARP is also a stateless protocol, and hosts will cache ARP replies even if an ARP request was never sent. Also, ARP entries that haven’t expired are overwritten when a new ARP reply is received.
Most importantly, there’s no sort of verification performed that confirms an ARP requests is coming from an authorized user. This weakness in ARP is what allows for ARP spoofing attacks to occur.
ARP only works with the IPv4 standard and 32-bit IP addresses. IPv6, on the other hand, addresses some of the inherent security issues present in ARP. It uses a protocol called Neighbor Discovery Protocol (NDP) instead, which employs cryptographic keys to confirm the identity of hosts. The majority of the internet still uses IPv4 however, so ARP continues to be widely used.
What is ARP Spoofing?
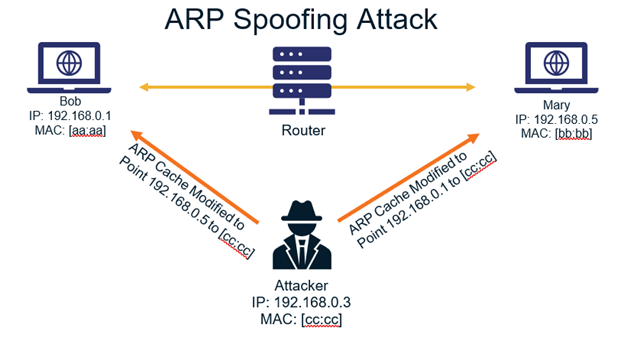
ARP spoofing is also known as ARP poisoning, and occurs when malicious ARP packets are sent to a default gateway on a LAN. This is done to alter the IP/MAC address pairings in the ARP table. The hacker tells the gateway that their MAC address should now be associated with the target victim’s IP address. The converse also occurs, with the target’s MAC becoming linked to the attacker’s IP address.
Then, the default gateway caches the new IP/MAC relationships and sends out that information to the other devices on the network. This means that all subsequent communications will go to the attacker’s machine first, rather than the intended recipient.
ARP spoofing attacks occur on a relatively low level, which benefits the hackers because it can be difficult for the victims to detect that their traffic is being affected (but as we’ll get to shortly, there are ways to both detect and prevent ARP spoofing attacks).
The Steps of an ARP Spoofing Attack
ARP spoofing attacks usually follow the same general steps:
- The attacker gains access to the local network and then scans it to find device IP addresses.
- The attacker uses a spoofing tool, like Driftnet or Arpspoof, to forge ARP responses.
- The tool’s IP address is set to match the IP subnet of the victim.
- ARP packets are sent that contain the attacker’s MAC paired with the victim’s IP address, tricking the router and PC to connect to the attacker instead of each other.
- The ARP cache is updated, and thus the PC and router keep communicating with the attacker.
- Other hosts see the spoofed ARP cache entries and will now transmit data to the attacker instead.
You can see how all of the pieces fit together in the diagram below:
What ARP Spoofing Is Used For
A large part of why ARP spoofing is so dangerous is that it’s commonly used as a launching point for other, more sophisticated kinds of attacks. Once an attacker successfully pulls off an ARP spoofing attack, they are then able to easily transition to performing:
- DDoS attacks – Instead of their own MAC address, the attacker can instead use the address of the server they wish to attack in order to launch a DDoS attack. By repeating this for a large quantity of IP addresses, the victim will be overwhelmed with traffic.
- Session hijacking – The hacker can get your session ID via ARP spoofing and then use it to access accounts that the victim is logged into.
- Continued packet theft – The attacker doesn’t necessarily need to do anything further. They can keep sniffing your packets and stealing your data (which is why, as we’ll get to later, encrypting your communications via TLS and HTTPS is so important).
- Altering communications – This would essentially be a man-in-the-middle attack. The hacker intercepts and modifies traffic, and can push malicious files or websites to the victim’s machine.
How to Detect ARP Spoofing?
There are a few different options out there for detecting ARP spoofing attacks. First off, there’s third-party software programs. These fall into two categories. First, there’s more general networking tools like Wireshark (which is also free and open source) that allow you to view all your network traffic and help with all sorts of troubleshooting and analysis. Then, you have programs built solely to detect ARP spoofing, like XArp (free and premium versions available), that continuously monitor your network for ARP spoofing attacks.
Prefer not to install an additional, external program? Then you’re in luck because you can also use the built-in functionality of your operating system to detect ARP spoofing. In this article we’re going to look at how to do it using Windows and Linux (the commands are the same for both):
- This method utilizes the command line, so we begin with opening an operating system shell as an administrator. In Windows 10, it will look like this:
- Enter the following command to display the ARP table:
arp -a
The result should look similar to the following:
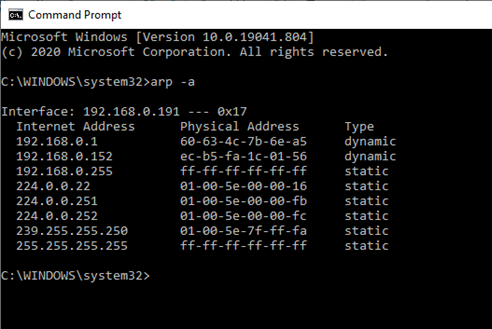
- Next, you’ll want to check if there are multiple IP addresses with the same MAC address (called “Physical Address” above). This is what indicates that an ARP spoofing attack is occurring.
Thankfully, we are safe. However, if an attack were occurring, it would look something like what you see below. The duplicate MAC addresses corresponding to two different IP addresses (circled in red) are the smoking gun:
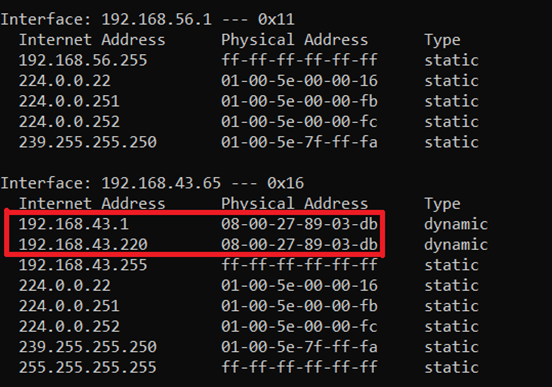
In the above example, the IP address 192.168.43.1 is most likely the router, so therefore it’s safe to assume the attacker’s IP address is 192.168.43.220.
If you’re dealing with a large network, then the command prompt method is more cumbersome and difficult to use since you’ll have to review tens, hundreds or even thousands of entries (as opposed to just a handful if you’re on your home network, for example). In that case, the specialized programs we mentioned earlier, like Wireshark or XArp, are probably your best bet for detecting ARP spoofing.
How to Prevent ARP Spoofing
There are several things your organization can do to help minimize the chances of an ARP spoofing attack happening on your network. Some are specific actions for you to take and others are general best practices that should always be followed:
- Use packet filtering to help identify poisoned ARP packets. It works by checking if there’s conflicting source information within the packets and if so, stops them from reaching other devices.
- Avoid trust relationships that rely on IP addresses for authentication. These make it easy for attackers to carry out ARP spoofing attacks.
- Use a Virtual Private Network (VPN) – VPNs encrypt all your communication, and therefore make your traffic worthless to any hacker that’s attempting an ARP spoofing attack. However, this becomes less feasible as your network size increases, since there needs to be a VPN connection between every single computer and server (resulting in a negative performance hit for your network).
- Use Static ARP – ARP allows for static entries for any particular IP address. By using a static ARP entry, you can prevent others from eavesdropping on ARP responses for that address. If a certain machine always connects to a particular router, for example, you can define a static ARP entry for the router and thus prevent ARP spoofing attacks.
- Use cryptographic network protocols such as Transport Layer Security (TLS), Secure Shell (SSH), or secure HTTP (HTTPS) to encrypt data in-transit.
- As we discussed in the previous section, use ARP spoofing detection software to detect attacks. They function by inspecting and verifying data before transmission and blocking data from spoofed sources. In addition to XArp, other popular tools include Arpwatch, which can be found here, and ARP-Guard.
- Intrusion-detection software, such as Snort, can also help stop ARP spoofing attacks by monitoring address resolution.
- Finally, after going through the rest of the items on this list, simulate an actual spoofing attack to check if your defenses are working as they should. If the attack does succeed, find the weak points and fix them.
Finding the Invisible Man (or Woman)
If you don’t know what to look for, ARP spoofing attacks can be difficult to detect. When you think about it, that’s really the whole point – an attacker is impersonating a particular device on your network and is leveraging their invisibility to steal data that they shouldn’t have access to. As we’ve seen, ARP spoofing can lead to further attacks that can spell disaster for your organization.
Make sure that your staff is aware of ARP spoofing and the dangers it poses and deploy tools on your network that can detect such attacks. Then, the invisible attackers won’t have anywhere to hide, and your data will stay safe.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown