Let’s Encrypt Warns of Reduced Compatibility Beginning January 2021
An Expiring Root Certificate Means 1 in 3 Android Devices Will Be Blocked From Millions of Sites Protected by Let’s Encrypt
Editor’s Note: Since the publication of this article, Let’s Encrypt has come up with a solution that allows Android devices to maintain compatibility with their certificates. You can read more about it here.
The new year is fast approaching, and with it comes some unfortunate news for users of Let’s Encrypt certificates. Starting in January of 2021, compatibility with Let’s Encrypt certificates will be reduced, impacting both website owners and users alike.
The impending issue is a result of Let’s Encrypt no longer cross-signing with a third-party root certificate. Because of this switch, certain website visitors will be blocked from accessing websites that are secured with Let’s Encrypt, and they’ll be greeted with an error message similar to what you see below:
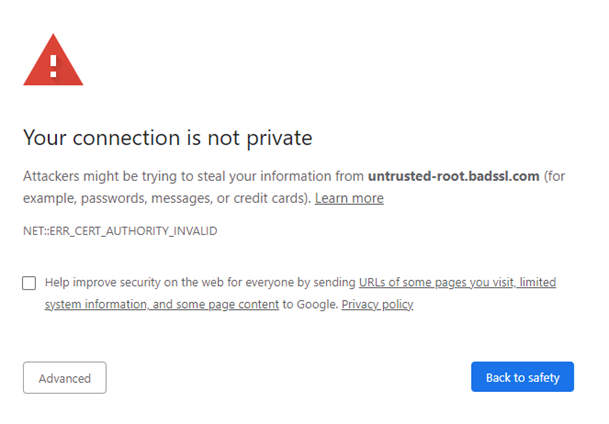
It’s certainly not something that users like to see when visiting a website. Similarly, site owners do not want anything presented that would raise doubts about the security and trust of their page.
So, what exactly lead to this turn of events? Who will be affected by the change? And what can site owners do to mitigate the damage?
Let’s hash it out.
Why the Issue?
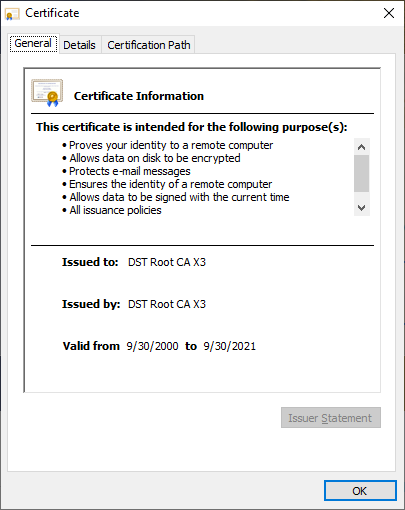
The genesis of the problem goes all the way back to 2015, when Let’s Encrypt was founded by the Internet Security Research Group (ISRG) and their various partners. Because their own root certificate could take years to be trusted by all the major browsers and operating systems, they cross-signed their certificates with an existing CA’s trusted root. It’s a typical course of action for new CAs, and in this case Let’s Encrypt went with IdenTrust and their DST Root X3 certificate.
This allowed Let’s Encrypt to immediately start issuing certificates that would also be trusted across the internet. Fast forward to the present day however, and the IdenTrust DST Root X3 is getting closer and closer to its expiration date of September 30, 2021.
Let’s Encrypt did attempt to prepare themselves for this expiration event, issuing its own root certificate, ISRG Root X1. Unfortunately, though, it doesn’t yet have the comprehensive trust that their soon-to-be-former IdenTrust root did.
Despite that fact, Let’s Encrypt will begin issuing root certificates chained to their ISRG Root X1 certificate on January 11, 2021. Since their own root doesn’t have the wide-ranging trust of the IdenTrust root, users on certain older platforms will be blocked from accessing any website that employs a Let’s Encrypt SSL/TLS certificate.
Who Exactly Is Affected?
While the good news is that the issue primarily effects older platforms, the bad news is that there are still a very large number of people using them.
The most significant group affected is everyone that’s using Android 7.1.1 or earlier. You might be wondering if anyone is still using such old versions, and the answer might surprise you – a total of 33.8% of all Android device are currently running them. And whenever they visit a Let’s Encrypt-protected site (currently 225 million domains fall in this category), they’ll encounter certificate errors and warning screens like we saw above.
It’s a difficult position for Let’s Encrypt to find themselves in, and it’s understandable considering the nature of the industry. Software update cycles can be glacial in their slowness, particularly with the Android operating system. It’s nothing new, and the causes are difficult to remedy.
To be clear, the root problem here isn’t Let’s Encrypt’s fault—the real problem here is the slowness of software updates for many platforms.
Manufacturers and/or mobile carriers often modify the OS before loading it on to their own devices and passing them on to end-users. Thus, when Google releases updates to Android, the manufacturers and carriers can’t simply just push the update on to their customers. They have to go back and incorporate the changes into their own proprietary software versions. Most of the time, especially for all but the newest devices, they just don’t. In some cases, the phone hardware may not even be capable of running newer software versions. Which is why we currently have millions of Android devices with out-of-date operating systems floating around.
Older Java versions are also be affected by the root change. Any clients that are using Java versions prior to 1.8.0_141-b15 will receive warnings and/or errors when encountering Let’s Encrypt certificates.
Those are the main ones we know about so far, but as we’ve seen previously with root expirations, more compatibility issues may arise with other platforms.
Recommended Actions
Site owners have a few different options at their disposal as far as mitigating the impact of the root expiration. First off, you can warn visitors that are using older versions of Android that they need to upgrade before using your site. They can upgrade Android or switch their browser to Firefox Mobile thanks to the fact that it relies on its own (and regularly updated) list of root certificates, rather than that of the operating system’s.
While this is a great remedy in theory, it’s also unlikely to be very effective since most users won’t want to go through the trouble of upgrading their device or switching browsers just to visit a site.
You could also stop supporting older versions. However, this could lead to frustrated users, an uptick in support requests, and lost revenue from reduced traffic.
Site owners that use ACME can modify their client settings to continue to use the cross-signed Let’s Encrypt certificates. However, this will only work until September 2021. It can buy you some time to get your long-term solution in place, though.
The most practical solution that doesn’t require any action on the user’s end is to switch to a CA with ubiquitous roots that are trusted by all major platforms (including older systems). Certificates from trusted and established authorities have used their own trusted roots for many years and cross sign using their own older roots to ensure full compatibility.
Tip: if you’re not sure how this will impact your website users, you can use Google Analytics to identify how many of your site users are using Android 7.1.1 or older. Our website gets about 4,000 visits per month from people using these older versions of Android, but the impact may vary depending on the audience your site targets.
Moving Forward
Let’s Encrypt will start using their new, less-trusted root in just over a month, so it’s best to figure out how you’re going to proceed as soon as possible. Especially since nearly one-third of all Android devices will be affected. No option is perfect. You can put the onus on your users, but then you’re depending on them to upgrade their devices or else be blocked from your site. Or you can switch to a CA with a root that’s fully trusted on both new and old devices. It requires some effort on your end, but that seems a small price to pay to maintain the trust you’ve built with your userbase and take the problem off their laps. Either way, make sure you’re prepared for January 11!



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown