What is a Man-in-the-Middle Attack? How do you prevent one?
Don’t let the man in the middle fool you
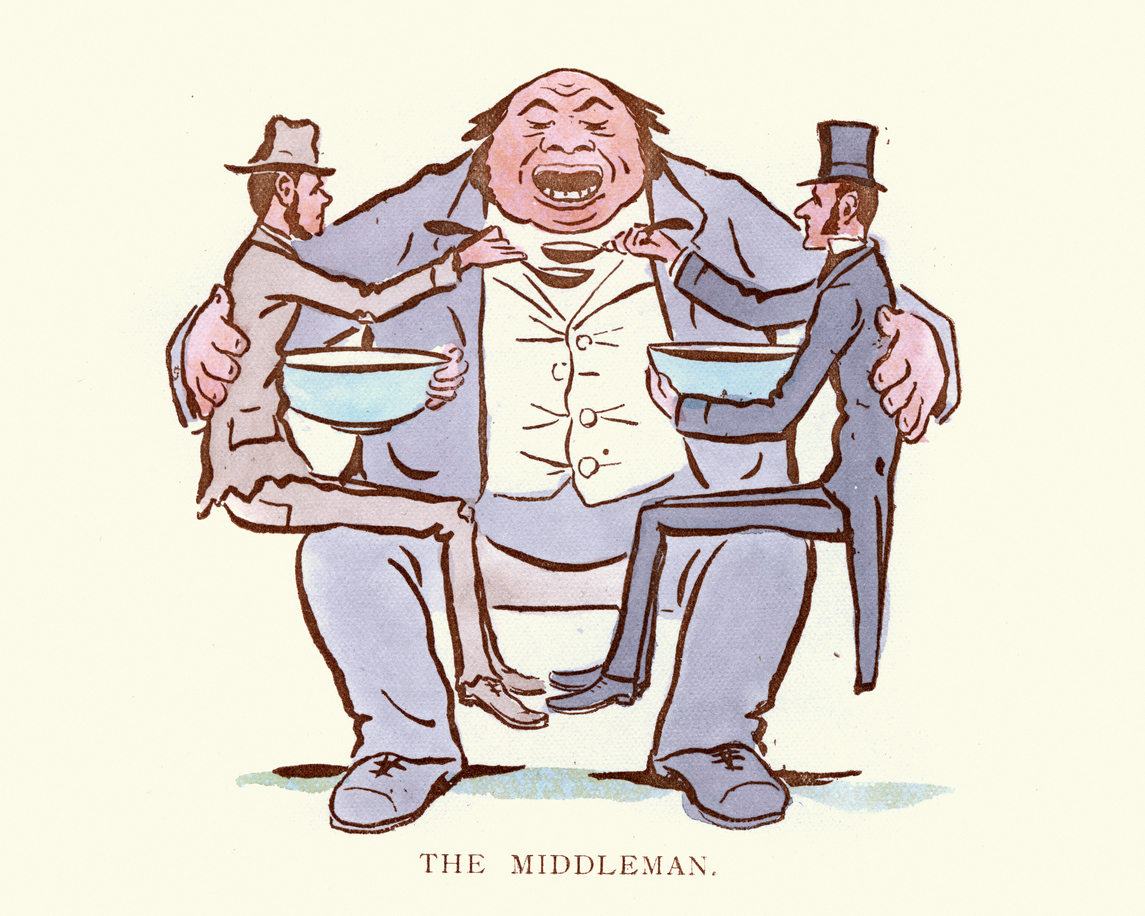
You may have heard the term ‘Man-in-the-middle (MiTM) Attack.’ You may even have a blurred idea of it. But you’re still wondering ‘What exactly is a Man-in-the-middle attack?’ Right? Let us hash it out for you. As implied in the name itself, this kind of attack occurs when an unauthorized entity places him/herself in between two communicating systems and tries to intercept the ongoing transfer of information. To put it simply, an MiTM attack is a modern-day version of bugging.
We’ll get more into the man-in-the-middle (MiTM) attacks in a minute but first look around you. Look at your smartphone, look at the apps in it, look at your PC, look at those smart-connected devices gossiping with each other, look at the website you’re on right now. Had a good look at them? Good. Now take a step back and think about everything you just looked at. What’s driving all these things? The answer would be data/information. The thing about data is that it travels. Whether it’s from one PC to another, one server to another, one country to another – data knows no bounds.
Unfortunately, all this traveling brings in the inevitable questions of security and privacy. When data leaves from one end-point to another, the period of transmission is where the control over it is somewhat lost. When an attacker positions him/herself in between the end-points and intercepts and/or tampers with this data-in-transit, it’s called a man-in-the-middle (MiTM) attack. In layman’s terms, it’s a lot like eavesdropping.
That’s right, when you try to overhear a conversation between two people without them knowing, it’s kind of like a man-in-the-middle attack. I personally like to do my snooping with my headphones over my ears, but turned off. And just to be clear with my colleagues, I don’t do this in the office… for the most part.
So, What Exactly is a Man-in-the-middle Attack?
While data transmission is taking place between a device (PC/Phone) and web server, an attacker using his skills and tools places him/herself between two endpoints and intercepts the data. While the two parties believe that they’re talking to each other, they’re communicating with (and through) the perpetrator in reality. That’s what a man-in-the-middle attack is.
Basically, it’s a con trick.
These attacks not only take place during device-server communication, but they also can occur wherever two systems are exchanging data virtually.
How does it work?
When it comes to MiTM attacks, there isn’t just one single method that can cause damage—there are four! Generally speaking, there are Sniffing, Packet Injection, Session Hijacking, and SSL Stripping. Let’s have a brief look at them.
- Sniffing: Sniffing or Packet Sniffing is a technique used to capture the packets of data flowing in and out of a system/network. Packet Sniffing in networks is equivalent to wiretapping in telephones. Keep in mind that Packet Sniffing is legal if employed correctly, and many enterprises do it for “security purposes.”
- Packet Injection: In this technique, an attacker injects malicious packets of data along with regular data. This way a user doesn’t even notice the files/malware because they come as a part of a legitimate communication stream. These files are a common commodity in man-in-the-middle attacks as well as denial-of-service attacks.
- Session Hijacking: Have you ever come across a “Session Expired” error? If you’ve ever made an online payment or filled out a form, you’d know this term. The time between when you log in to your bank account and log out of it is called a session. These sessions are often the targets of hackers as they potentially contain discreet information. In most instances, a hacker establishes his/her presence in the session, and ultimately takes control of it. These attacks can be executed in various ways.
- SSL Stripping: SSL Stripping or SSL Downgrade attacks are a rare species when it comes to MiTM attacks, but also the most dangerous one. As we all know, SSL/TLS certificates keep our communication safe online via encryption. In SSL Stripping attacks, attacker strips off the SSL/TLS connection and the protocol is turned from secure HTTPS to insecure HTTP.
How to prevent man-in-the-middle attacks?
Keep in mind that these attacks are not as easy as turning your headphones off, they’re highly complicated in nature. You need to have some serious skills and must be aided by right tools. But just because a MiTM attack is difficult to pull off, doesn’t mean you shouldn’t actively protect against them.
RELATED: How to spot a fake website
Here are our recommended practices to protect against man-in-the-middle attacks:
- Make sure that the websites you visit have HTTPS in front of the URL
- Before clicking on emails, check the sender of the email
- If you’re a website admin, you should implement HSTS
- DO NOT make a purchase or send sensitive data on a public Wi-Fi network.
- Make sure your website doesn’t have any mixed content
- If your website is using SSL, make sure you have disabled insecure SSL/TLS protocols. You should only have enabled TLS 1.1 and TLS 1.2
- Don’t click on malicious links or emails
- Do not download pirated content
- Secure your home/work network
- Have proper security tools installed on your systems



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown