PCI Compliance Numbers Drop as Security Breaches Increase
A mere 27.9% of organizations are PCI DSS compliant — an alarming number in the face of rising security threats…
A concerning issue has arisen for the payment processing industry in recent years, one that could have serious ramifications for both consumers and businesses alike. The amount of security threats facing users is increasing by the day, yet the number of organizations complying with industry security standards continues to fall.
The COVID-19 pandemic crisis has made it worse than ever. We’ve seen more and more businesses reduce their physical footprint or close their doors completely in the face of reduced traffic to their brick-and-mortar locations. Many have shifted their focus to online operations as a result, and they have been left scrambling in an attempt to keep their digital presence secured. With less available resources and smaller budgets, PCI DSS compliance has now become harder than ever for many, and for some it’s even viewed as downright impossible.
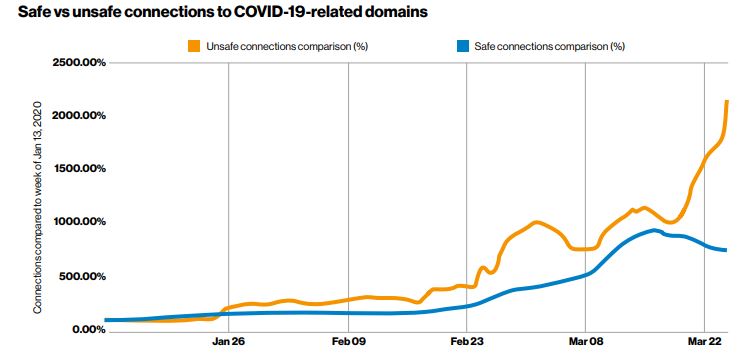
The repercussions have trickled down to consumers too, as the percentage of unsafe connections to COVID-19-related domains drastically increased as the pandemic picked up steam. Within the first few months there was a massive uptick in malicious actors attempting to use social engineering to prey on those impact by the virus, creating scams related to stimulus checks, charitable donations, offers for free COVID testing, and more:
Unfortunately, decreased PCI compliance is a trend that pre-dates the coronavirus outbreak. Thanks to a recent study performed by Verizon, we can see that some alarming industry trends have emerged in recent years. It’s critical that businesses learn how to properly address their compliance shortcomings, both for their own benefit via the avoidance of costly penalties and damage to their reputation, and for the benefit of consumers that are potentially putting their personal and financial data at risk with every transaction.
So, what exactly did Verizon’s comprehensive industry study find? What are the challenges facing organizations with regards to meeting PCI DSS standards? And what can they do to make the process of achieving PCI compliance as smooth as possible?
Let’s hash it out.
The Basics of PCI DSS
Before we get to Verizon’s study, let’s first do a quick review of what exactly PCI DSS is and what it means. For a deep-dive on PCI compliance, check out our previous blog post, “Demystifying PCI DSS Compliance.” For now though, we’ll just go over the basics.
The Payment Card Industry Data Security Standards (PCI DSS) are maintained by the PCI Security Standards Council (PCI SSC), and its members are all of the big guns in the credit industry. Think Visa, American Express, Mastercard, Discover, etc.
Since all the industry giants are on the PCI SSC, essentially any company that accepts credit card payments must abide by the security regulations within the PCI DSS. The individual credit card companies are the ones that actually enforce the PCI DSS, which means that if you break the rules then you could be faced with multiple fines from each creditor you accept, rather than just getting a single fine from one overarching entity.
The fines can top out in the range of hundreds of thousands of dollars, or even into the millions for severe violations by large companies. Plus, there are the intangible effects that come with PCI non-compliance, such as damaged customer trust and brand reputation. So, it’s safe to say you don’t want to run afoul if at all possible.
PCI DSS Compliance by the Numbers
Last week saw the release of Verizon’s annual Payment Security Report. They examined in detail how organizations are meeting compliance requirements, as well as in what exact areas businesses are lacking. The report also looks at data security and compliance challenges facing businesses that process payments, and what they can do moving forward to improve their security measures.
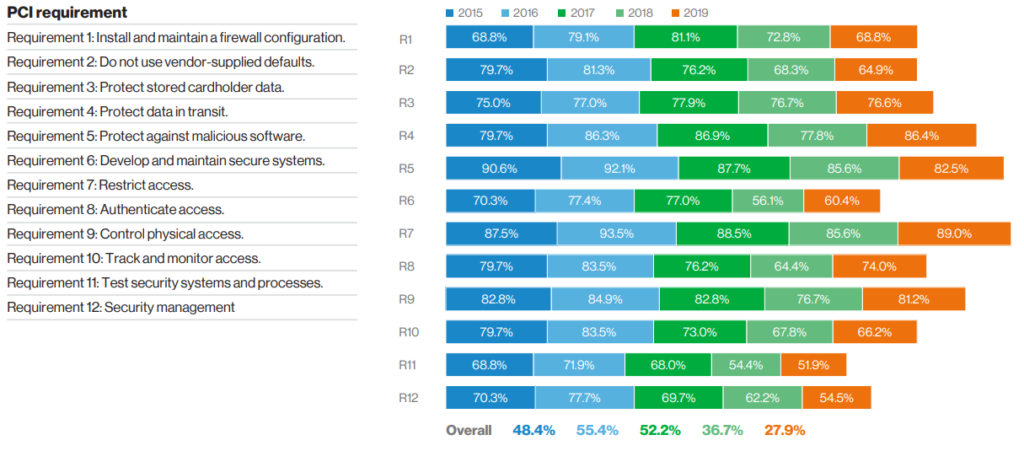
The numbers in the report were sourced from an assessment of PCI-DSS compliance data compiled from 68,992 controls across 60 counties and 334 PCI compliance validation reports. Verizon found that less than 28% of organizations were 100% PCI DSS compliant in 2019, which was an 8.8% drop from the previous year.
Perhaps the most significant concern coming out of the report, one that we touched on earlier, is that this drop is clearly not an anomaly but a continued trend. Since 2016, the overall compliance number has dropped a whopping 28%.
As far as specific problem areas go, the biggest areas of non-compliance were as follows:
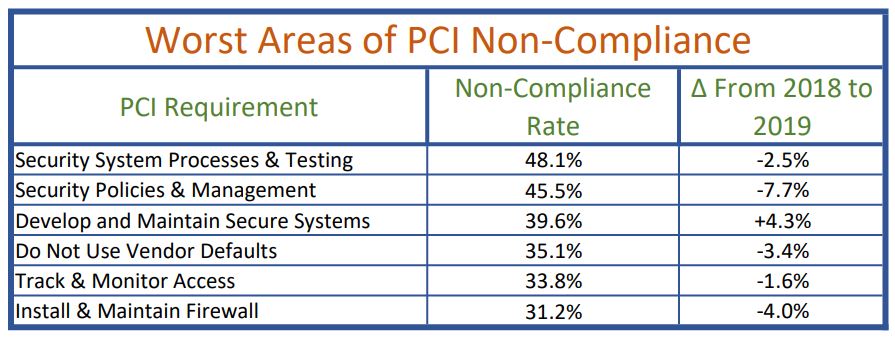
You can see that all but one requirement on this list, “develop and maintain secure systems”, saw decreases in compliance rates from 2018 to 2019. Things weren’t exactly rosy for the areas of high compliance either. The requirement for “thwarting malicious software” for example, saw a 3.1% drop from the previous year, despite an 82.5% rate of full compliance. You can see the full compliance numbers and 5-year trends for each of the primary PCI requirement categories below:
Threat Motivations and Attack Specifics
The least compliant industries were found to be retail, financial, and hospitality. One thing that was common across all industries surveyed however, was that financial gain was the by far the biggest reason for security incidents. Verizon found that 99% of attacks were financially motivated, with payment data and personal credentials “continuing to be prized.” They also saw that web applications, as opposed to point-of-sale devices at physical locations, were the cause of 90% of retail breaches.
In the financial and insurance sectors though, that number is much lower. Only 30% of breaches were made via web app attacks. The report found that the primary goal of these attacks was to access sensitive data in the cloud via stolen credentials. The increased migration to online services was a key factor.
The trends within the healthcare industry diverged from the overall trends, evident by the fact that 31% of breaches were a direct result of basic human error. External breaches, at 51% of the total, were only slightly more common than internal breaches, which accounted for 48%. It remains the industry with the highest number of internal bad actors, due to the levels of access needed for employees to perform their jobs.
Across all industries, social attacks and credential theft (via things like phishing attempts and business e-mail breaches) led to more than 67% of total breaches. Of these, 37% were caused by stolen or weak credentials, 25% resulted from phishing attacks, and 22% stemmed from human error.
Today’s PCI Compliance Challenges
One of the main conclusions that can be drawn from the report is the lack of long-term security thinking within organizations. The focus tends to be on quick fixes that act as a mere band-aid, rather than creating and implementing a long-term strategy. This short-sighted thinking has had a severe impact on the ability of businesses to sustain PCI DSS compliance.
There are several factors at play as to the root causes of this sort of approach, the first being a lack of education. You’ve probably heard the phrase “you don’t know what you don’t know” before, and it very often rings true when dealing with cybersecurity topics. Security needs to be a part of the everyday culture, and this requires both a time and resource investment from organizations. Training must be performed for all staff that is relevant to their specific role, and budgets must be provisioned to allow for the increased automation of threat prevention.
Verizon’s report pointed out that many businesses meet resistance when trying to convince senior management of the measures required to keep data secure. A few different considerations lead to these data security management traps that ultimately cause organizations to fail when trying to implement a culture of strong security. Among them include ill-equipped leadership, a failure to secure strategic support, lack of resources, and inadequate strategic design.
The report also cited such key problem areas as “deficient strategy in execution of security measures, low capability and lack of continued improvement in the system and communication and culture restraints.” You can see below that a significant number of organizations are lacking when it comes to security-focused leadership, budgets, and culture:

Aiming for a Moving Target
It doesn’t help matters that cybersecurity is a continuously changing field. PCI DSS is intended to be evolutionary as well, taking into account the fact that both the payment landscape and associated threats are always advancing. It’s easy to get complacent once your security strategy and security measures are initially in place, and organizations that remain static will inevitably experience a steady decline in the quality of their program over the years. Threat actors won’t stop doing their thing, and organizations must stay on their toes with well-thought out policies and processes that enable that kind of agility.
It’s not just organizational and strategic challenges at play, however. Some businesses fail to perform the routine audits needed to verify PCI compliance simply because they do not or cannot spend the money it takes to get the infrastructure in place. Compliance is non-negotiable, but the costs can simply be out of reach if a lot of remediation is needed. It can lead to a catastrophic snowball effect where you can’t afford the fixes, but then are hit with crippling fines, as well.
SMB’s are especially at risk for this sort of trouble. While they have less data to process and store versus larger corporations, they also have significantly less resources and budgets available for security. It makes it even harder to set aside what is needed to meet PCI DSS compliance. SMB’s are just as at risk as the big boys as far as security incidents are concerned, so the perception must be broken that the required measures to achieve compliance are too costly or time-consuming.
Keep in mind that security is a journey. Start by making the commitment to be more secure this month than you were last month!
Take Action to Be PCI Compliant
The report is certainly a wake-up call to organizations, driving home the point that educated and focused leadership is required to address security failures, adequately manage payment security, and comply with PCI DSS security controls. Interestingly, Verizon found that the primary root causes were not technological, but instead originated from weaknesses that could be addressed by measures such as formalized processes, businesses models tailored to security, and a sound strategy with carefully planned frameworks.
For all of that to occur though, there must be an invested stakeholder to oversee it all. This presents another challenge, since most organizations do not have a single person responsible for security, compliance, and risk-assessment. Long-term data security requires the combined effort of multiple roles, lest even the best laid plans crumble. Chief Information Security Officers, Chief Risk Officers, and Chief Compliance Officers must all work in harmony to achieve the common end-goal. The CISO in particular must implement the proper security standards and technologies, in addition to possessing an in-depth understanding of the threat landscape.
It’s critical that organizational strategy aligns with the security strategy in order to maintain compliance. This doesn’t just mean PCI DSS compliance, but adherence to other regulations as well, such as the EU General Data Protection Regulation (GDPR) and any other location or industry-specific rules whose jurisdiction the organization falls under. Security doesn’t automatically mean compliance, and the same applies in reverse. That being said, security must be aligned with both PCI requirements and organizational requirements in order to maintain customer trust (which can be all too delicate and difficult to repair).
Technological Solutions for PCI DSS Compliance
While the study found that the primary root cause of non-compliance wasn’t technology-based, appropriate solutions can make a world of difference when paired with smart processes and strategies. The report found that 70% of breaches were from on-premise systems, as opposed to only 24% coming from cloud systems. A business doesn’t need to take on all of the security burdens themselves, and a well-configured cloud deployment can be as secure, if not more so, than an on-premise one. The numbers show that most of the cloud breaches that did occur were a direct result of improper configuration.
Leveraging third-party systems also simplifies the auditing process. If customer data is stored in an off-site data vault that’s managed by someone else, then the payment service providers only need to function as an intermediary when transmitting data from there to their own merchants. Thus, the scope of operations requiring examination is decreased.

Use Sectigo HackerGuardian to Help Your PCI Compliance
Sectigo HackerGuardian makes PCI compliance easy with automated scans and ready-to-submit reports.
Tackling the #1 PCI Compliance Deficiency
Verizon’s report showed that the top area companies are falling short is PCI DSS requirement #11: Test security systems and processes.
PCI compliance scanning services are a simple and effective way to audit your website to ensure PCI DSS compliance. They’re the quickest and least costly way to run a check on your entire system, and don’t require investment for in-house resources and development that could be required.
Sectigo’s HackerGuardian PCI Scanner is one such service and lets merchants run a vulnerability scan. It’s actually a requirement of PCI DSS that you perform an external scan on a quarterly basis. Not only that, but the scan must be performed by an Approved Scanning Vendor (ASV).
Sectigo is one such vendor, and their HackerGuardian runs a comprehensive array of tests that include over 30,000 vulnerability tests. It’s also easily scalable to cover additional IP addresses if needed.
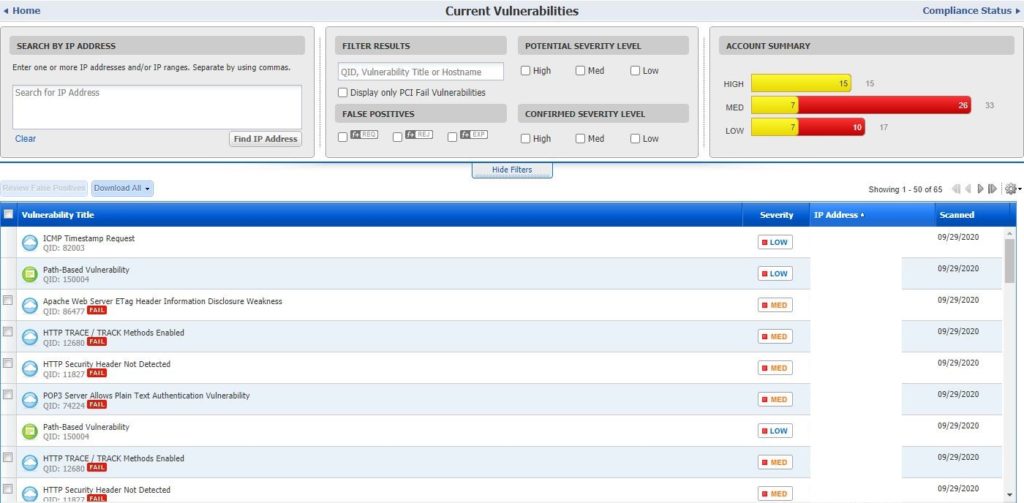
HackerGuardian provides an easy-to-understand, high-level dashboard view, as seen below:
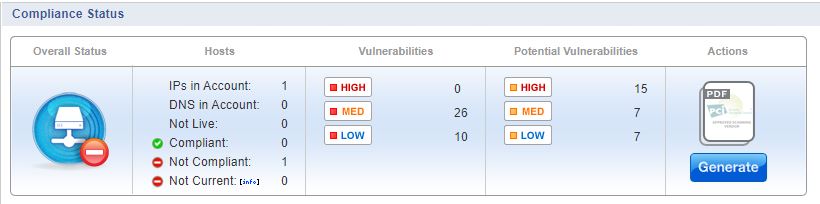
And you can take a more in-depth look at every single vulnerability, as well:
HackerGuardian also lets you automatically generate PCI compliance reports that are ready to send to your merchant bank, reducing the load on your staff and taking away the stress and headache that you’d have to endure by doing it the manual way.
PCI Compliance Moving Forward
PCI compliance has been heading in the wrong direction, and COVID-19 has only made things worse. In fact, a phishing simulation performed in late March with 16,000 participants found that nearly three times as many people clicked the link and entered their credentials than from a similar test run in late 2019. The security strategies required by PCI DSS can help provide security in uncertain times like these.
When companies let cybersecurity slide, their customers often end up paying the bill. FTC data shows US consumers reported losing $1.9 billion to fraud in 2019, and 271,000 people specifically reported being victims of credit card fraud. (And that’s not counting the many people who didn’t bother filing a report!)
With more and more businesses concentrating on their digital presence, consumers have been further driven towards contactless methods of payments. The good news is that each organization controls their own destiny in relation to PCI DSS compliance, but must work smarter AND harder to get where they need to be. As we’ve seen, it starts with organizational strategies, policies, and processes, which then must be implemented in practice with the right technological solutions.
Businesses need to make security a long-term focus, while technology providers must educate and empower them, all with the common goal of keeping customers safe.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown