A SHA-1 Collision Has Been Created
But has this SHA-1 Collision truly broken SHA-1?
“We have broken SHA-1 in practice.”
That is the opening sentence on shattered.io, the official website for the first practical demonstration of a collision with the SHA-1 hashing algorithm. The new research was a combined effort by Marc Stevens and Pierre Karpman of the CWI Institute in Amsterdam, and a team from Google.
A hashing algorithm is supposed to create a unique hash value for every file. That hash can then be used to compare and identify files. In some systems, a hash is used as a digital signature and computers rely on them to judge the authenticity of a file.
“…there is much more to “breaking” a hashing algorithm than just demonstrating a collision.”
A collision is when two distinct files, made up of different bits, produce the same hash. This means that a computer comparing the hashes cannot identify one file from another, which attackers could use in a variety of attacks.
In systems where hashes are used for secure purposes, this collision is now undeniable proof that SHA-1 is not safe to use.
But while this is major progress on breaking SHA-1, this publication does not mean that a switch has been flipped and every SHA-1 hash is suddenly unreliable.
The SHA-1 hashing algorithm has been known to be weak since 2005. For the last few years many in the infosec community considered a SHA-1 collision to be imminent, and while that had yet to be proven, it was a serious enough concern that many fields sought stronger replacements. This spurred the SSL industry to start transitioning away from SHA-1 about 3 years ago.
According to Valerie Aurora’s “Reactions to stages in the life cycle of cryptographic hash functions” table, the first demonstration of a practical collision means it is now time to marvel at the technical feat of how it was done, but it’s hardly a DEFCON situation.
That’s because there is much more to “breaking” a hashing algorithm than just demonstrating a collision. This is only the first in a series of demonstrations necessary to truly declare an algorithm broken, and then there is the practical matter of actually using these attacks.
Because this is an identical-prefix attack, the current attack scenarios are very limited. In plain language, an identical-prefix attack requires that the attacker can produce, control, or influence both files: the ‘original’ and the collision. This means that creating a collision for an existing file, such as a third-party website’s SSL certificate, is not yet feasible.
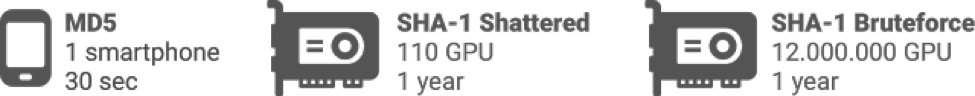
Even if the attack you had in mind worked with these restrictions, you have to be ready to deal with the cost. It took nine quintillion SHA-1 computations to produce a SHA-1 collision with the Shattered technique. That’s 9,223,372,036,854,775,808, the bolded red digit represents trillions, to put it in the context of a big number we are familiar with.
Crunching that many calculations requires a lot of computing power.
There were two distinct phases to the technique, the first requiring 6,500 years of CPU compute time, and the second using 110 years of GPU time. If you were to use a cloud-computing service like Amazon Web Services, this amount of computational power would come with a 6-figure bill. That’s all to produce a single collision.
At that cost, creating a SHA-1 collision is not yet feasible for most organizations and people, and likely not worth it for many more who could foot the bill. Though that isn’t to say it’s totally out of reach for the top targets of nation states. Some governments have spent more than a million dollars on 0-days and other assets to attack political targets, so it is feasible they could add this to their arsenal.
But most of us aren’t hunted political activists. So, for everyday people and the infosec community, what does the Shattered collision really mean?
For the SSL industry, luckily not much. Publicly-trusted SSL certificates have been using the SHA-256 hashing algorithm and that will be secure for many years to come. The most recent version of Chrome completely blocks all SHA-1 certs from trusted roots, and Firefox has just announced it will immediately do the same as a result of this collision.
But other systems and software still use SHA-1, and those communities will now need to deal with the fact that a collision means realistic threats are now on the horizon. For instance, the GIT version control system uses SHA-1 hashes to identity repositories and commits. The email encryption system PGP also heavily relies on SHA-1 signatures, and it is a common practice to print digests of PGP keys on business cards.
While the Shattered collision is not likely to cause any harm tomorrow, it’s a near-future risk that will require some major changes, and push some systems to move on to a new hashing algorithm for the first time in more than a decade.




















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown