Symantec: Energy Sector Targeted by Hacker Group Dragonfly
A report from Symantec claims the re-emergence of an old foe with a new target
According to a report by the cyber security company, Symantec, the energy sector in Europe and North America is being targeted by a wave of cyber attacks. The attacker is a group known as Dragonfly, which has the means to severely disrupt operations.
Dragonfly has been in operation since at least 2011. It was exposed back in 2014 and appeared to go dormant for a while. However, in the past couple of years, the group has re-emerged and is now operating freely again. Symantec has dubbed this second act “Dragonfly 2.0,” given that its tactics and tools are eerily similar to those used in the previous campaign.
A quick aside, what is it with the names of these hacker groups? Fancy Bear. Cozy Bear. Dragonfly. I guess I just always figured hacker collectives were far more metal than EDM.
Anyway, per Symantec:
The Dragonfly group appears to be interested in both learning how energy facilities operate and also gaining access to operational systems themselves, to the extent that the group now potentially has the ability to sabotage or gain control of these systems should it decide to do so.
The Energy Sector is a High-Value Target
Over the past few years, internationally, we’ve seen a number of incidents involving cyber attacks and cyber espionage and the energy sector. Most notably, Ukraine’s power system was victimized in 2015 and 2016, which left hundreds of thousands of people without power.
It’s not hard to see how knocking out a power grid could be advantageous, and – given the news over just the past few months – it’s obvious that many hackers and cyber groups are keenly aware of this.
While Dragonfly certainly isn’t the only group attempting to exploit the power grid, its efforts certainly provide us with some interesting insights into the issue.
Honing in on Dragonfly 2.0
Per Symantec, Dragonfly 2.0 has been active since “at least December 2015,” but its activity has really ramped up this past year. The majority of the attacks have been concentrated in the United States, Turkey, and Switzerland, with some light activity in other areas. The US and Turkey were targeted in Dragonfly’s previous campaign as well, though the amount of activity has definitely spiked in Turkey this time around.
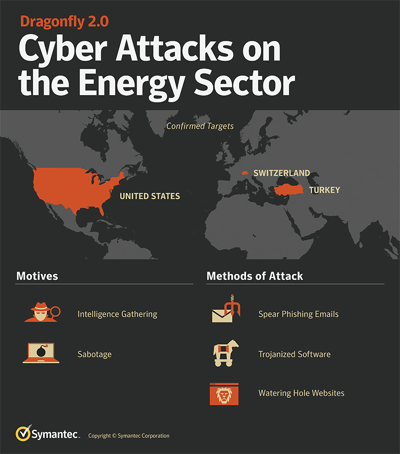
The group’s MO is fairly straightforward—it’s not like it’s reinventing the wheel. The campaign kicked off in December of 2015 with an email phishing campaign disguised as an invitation to a New Year’s Party. From that point, the emails were disguised to look like energy sector, and general business-related emails. After the emails were opened, the attached document attempted to leak the victim’s network credentials to a third-party server.
The group also compromised a number of other websites that were likely to be visited by employees of targeted organizations to conduct watering hole attacks and gather network credentials.
Dragonfly is now using those credentials to attack those organizations, specifically to install backdoors that could give it remote access to compromised machines. Symantec now believes that Dragonfly’s earlier exploits were merely part of an exploratory phase.
What is clear is that Dragonfly is a highly experienced threat actor, capable of compromising numerous organizations, stealing information, and gaining access to key systems. What it plans to do with all this intelligence has yet to become clear, but its capabilities do extend to materially disrupting targeted organizations should it choose to do so.
So, think about that the next time your power goes out.
What We Hashed Out (For the Skimmers)
Here are the key points from today’s discussion:
- Symantec has released a report that outlines a current threat to western power systems
- The threat comes from a group called Dragonfly that has been operational since 2011
- This is Dragonfly’s second campaign, it appears that the group is now beginning to attack using network credentials it has harvested over the past several years.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown