All posts in
Beyond Hashed Out
It’s getting harder to tell what’s real and fake online. A new technical standard from Adobe, Microsoft, Sony, DigiCert and dozens of other industry leaders aims to solve this problem….
From organizations paying massive noncompliance fines to consumers shunning companies they perceive as insecure, we’ll break down the impact of cyber attacks on businesses and individuals from businesses’ and consumers’…
Looking to make a purchase online? Want prospective customers to feel confident making purchases on your website? We’ll walk through how to know if a website is safe (and what…
Step-by-step guides (with illustrations) showing how cryptographic key pairs work in five different public key infrastructure (PKI) scenarios. We know private-public key pairs are used in a multitude of ways…
Verified checkmarks are no longer just for social media. On May 3, Google began displaying blue verification checkmarks for email senders that have BIMI and verified mark certificates (VMCs). Here’s…
Farewell, lock symbol: Google Chrome will retire the padlock icon as the next step in making HTTPS the default for all websites. Billions of people around the world associate a…
Holding executives and employees personally responsible is seemingly gaining traction within IT and cybersecurity communities and global political arenas. Let’s explore a few examples and see what this might mean…
The White House’s updated National Cybersecurity Strategy calls for greater regulation and enhanced security of our country’s critical infrastructure. Here are our top 5 takeaways from a public key infrastructure…
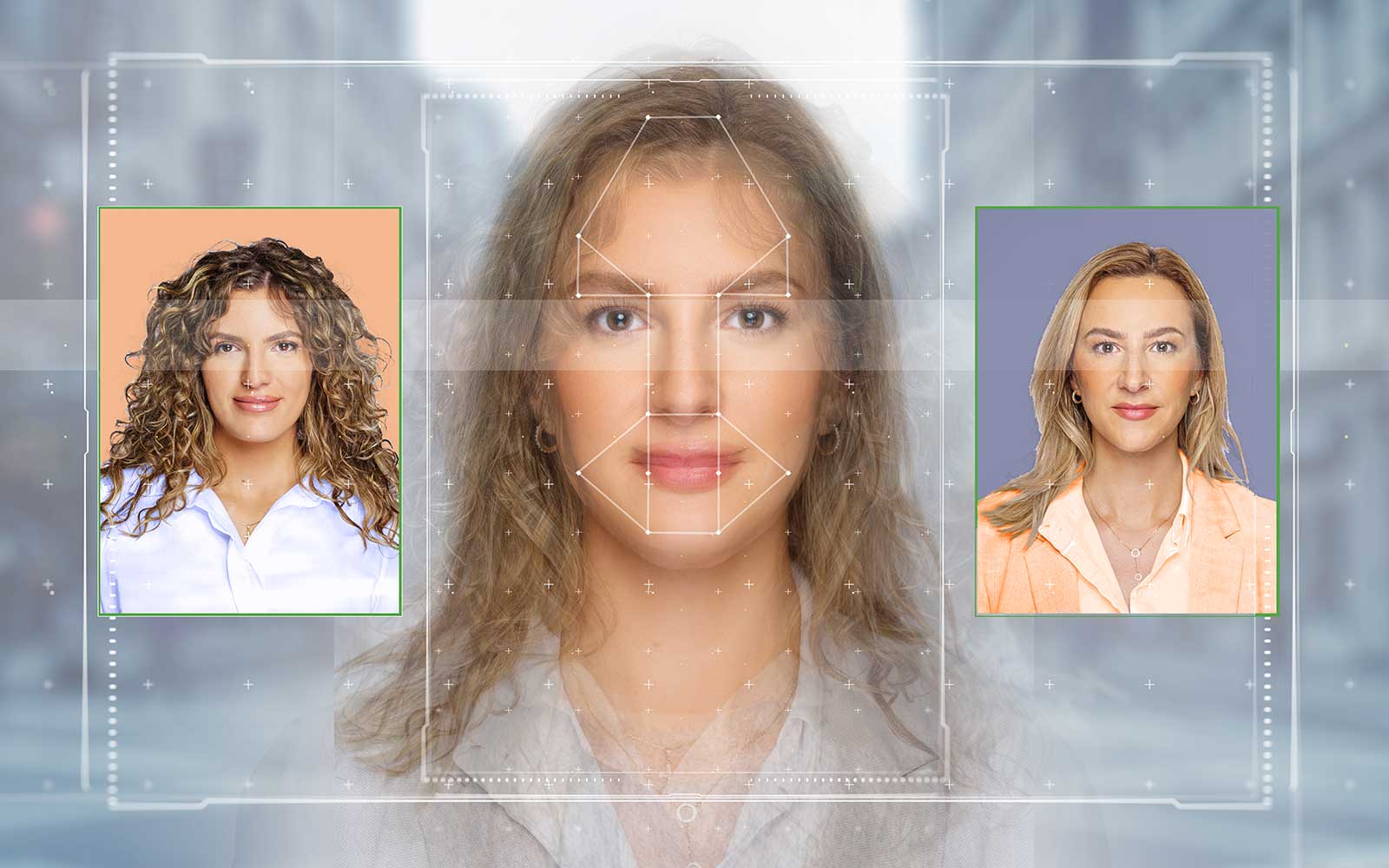
47% of organizations reported experiencing a vishing or social engineering attack in 2021 — let’s explore how artificial intelligence can catch your employees off guard and what you can do…
Penetration testing is one of the most effective steps toward maintaining cloud security. But knowing how to pentest effectively is easier said than done — here are some insights from…





































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)












 (5 votes, average: 4.40 out of 5)
(5 votes, average: 4.40 out of 5)
5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown