When it Comes to Phishing the Best Defense is Education
Users need to know what to look for before they’ll know if they’re being phished
Phishing is one of the biggest threats facing internet users. Period. That’s largely due to the level of human ingenuity needed to successfully phish someone—especially nowadays. Phishing requires social engineering to succeed, when it’s executed properly a phishing scam can border on the genius. As in, there’s no way you’d ever see it coming.
It’s been all over the news lately. We’ve covered the fact that PayPal phishing sites are running rampant. Just this week a report on INC.com warned users of an Amazon phishing scheme. And last week a Canadian University discovered it had been swindled out of nearly 12-million dollars in a phishing scam.
That last example, at MacEwan University, serves as an excellent case study for just how clever phishing scams can be. After building fake websites for over a dozen Edmonton-area construction companies, the hackers began to send phishing emails to those companies’ potential business partners and collected handsomely.
Now let’s dissect that a little bit. There’s no way that, as the owner of a construction company in Alberta, you’ve pegged phishing as one of your biggest threats. There are frankly a number of misnomers about phishing. One of them is that you have to be a certain kind of company to be a target. That is patently untrue. Case in point, these construction firms.
Then there’s the school, MacEwan University, which probably never suspected that hackers would try to infiltrate using faked credentials from a construction partner. But that’s what happened, a well-constructed email led to a convincing spoof website and errant payments were made.
Education is the Best Defense for Phishing
We stress the need for education so frequently that it’s starting to sound like a platitude—and that’s a dangerous thing. Because education is the best defense against phishing.
There are some defenses that can offer a limited benefit, SSL for one can offer a degree of authentication that can differentiate real websites from fake ones, for instance. But the benefits of higher validation SSL certificates are non-existent without adequate education. And I’ll be the first to admit, many on the CA-side of the SSL industry overstate the value of authentication without properly stressing the need for education.
Here’s the crux of the current phishing issue:
- Inadequate and oftentimes inconsistent education have created a misperception among internet users about connection security, its indicators and what they mean.
- Recent browser changes have further confused this issue by adding the label “secure” to websites with properly configured SSL encryption. Many users mistakenly confuse “secure” for safe.
- Phishing websites have begun adding free DV SSL certificates, which activate the “secure” visual indicator from browsers and add an air of legitimacy to illegitimate websites.
The last item on that last, regarding free SSL and phishing websites, is perhaps the most complicating factor as many users already don’t know what to look for and are now being told a website is “secure,” which can easily be confused for safe.
Once again, the only surefire defense is better education.
The Value of Extended Validation is Entirely Dependent Upon Education
Extended Validation SSL is known for activating the green address bar. Or rather, the address bar used to be green, now it just adds the verified name of the organization that owns the website to the address bar. In green font. So, the name still kind of works.
Regardless, there’s actually a debate going right now about whether or not EV has value or if it’s just a marketing ploy by the certificate authorities (as some in infosec community have alleged). The truth is that EV is only valuable if users understand what the indicator means and know when to look for it.
To that end, Paul Walsh, the CEO at MetaCert, made an excellent suggestion in a recent post on Medium. After discussing how Extended Validation can reduce the risk of phishing scams targeting crypto-currency companies, he proposes a banner that specifically points out the EV indicator.
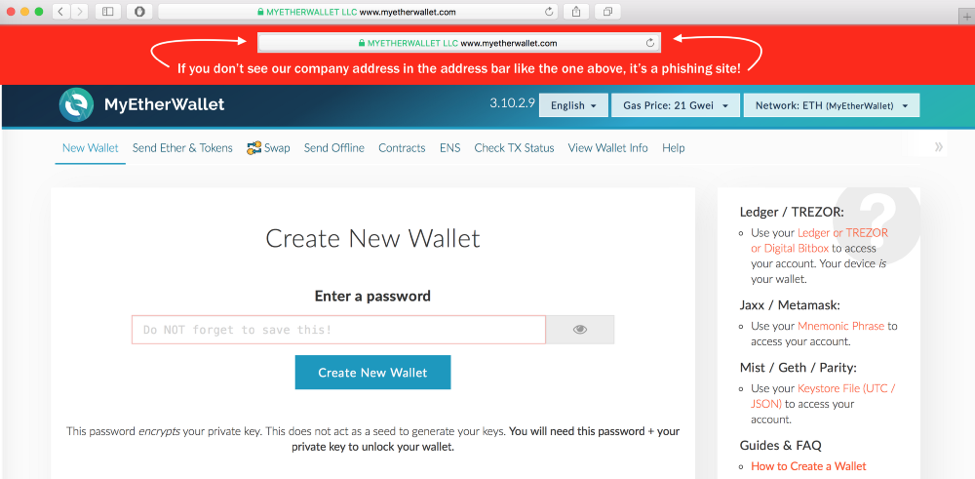
While Walsh concedes there is a little bit of overhead in the form of design and development costs, the result is that users will have a clear idea of what to look for before trusting a website that claims to be this entity, MyEtherWallet.
By placing a screen shot of what the address bar should look like, I think it should increase the likelihood of visitors noticing that the phishing sites aren’t real. I could be wrong. But I don’t think I am. The warning message doesn’t need to be permanent. You can design it with some slick animation and have it disappear after x-number of seconds.
I couldn’t agree with this suggestion more. Even if users only see it the first few times they visit, the idea should stick. And though this is intended for crypto-currency sites, it’s a lesson that can be carried over to other domains as well, giving this idea a great degree of utility.
EV has the power to be an absolute game changer, and when employed properly it has proven to be. But without proper user education, EV is little more than snake oil. And while there’s still a lot the industry as a whole needs to do to better educate users on connection security and the accompanying indicators, Paul’s suggestion is great advice for any online business or organization that is using EV SSL.
What We Hashed Out (For Skimmers)
Here’s a look at the key points we covered during today’s discussion:
- Phishing can affect any business with an internet presence, lately phishing sites have been adding free DV SSL certificates that activate the “secure” visual indicator and make the website look more legitimate.
- Extended Validation SSL certificates can help defend against phishing by offering a unique visual indicator, but without educating users on the indicator EV is of limited value.
- Paul Walsh, the CEO of MetaCert, suggests adding a temporary banner with a screen shot of your website’s EV indicator to educate users what to look for on your website.





































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)













5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown