How Secure is RSA in an Increasingly Connected World?
KeyFactor’s latest study shows that many IoT device manufacturers are generating insecure RSA keys
1 in 172. That’s the number of RSA public key certificates available through the internet that could be vulnerable to compromise due to shared cryptographic key factors.
These findings are according to a recent report on RSA certificate vulnerability from KeyFactor, a leading provider of secure digital identity management solutions and an established authority in the cybersecurity industry. A team of KeyFactor researchers presented their findings at the First IEEE Conference on Trust, Privacy, and Security in Intelligent Systems and Applications in December. The data indicates that due to improper random number generation, many RSA public keys are at risk of compromise because the researchers were able to use them to derive their private keys through a method known as “factoring.”
Essentially, the research indicates that RSA is still secure, but many companies are implementing it in insecure ways. As such, it underscores the importance of organizations and manufacturers being “crypto agile” and adhering to cryptographic best practices to maintain trust and security.
But just how big of a potential impact would compromising RSA keys have? While there’s no single reliable resource we can point you to that shows X% of certificates issued use RSA keys, what we can tell you as a company that sells a lot of them is that it’s a lot. Considering that Gartner forecasts that there will be 25 billion IoT devices in use by 2021, that’s potentially a lot of vulnerable RSA certificate keys in the wild that cybercriminals could exploit.
In this article, we’ll break down the data from the study, rehash what RSA is, and explore the implications of what the research means for your organization.
Let’s hash it out.
How Secure is RSA? Breaking Down the KeyFactor Research Data

KeyFactor, a company we work with at The SSL Store, has made a name for itself as an IoT device security leader in the industry since the company’s inception in 2001. A force to be reckoned with, they’re dedicated to empowering enterprises of all sizes through their award-winning PKI-as-a-service platform. They’re also known for their research collaborations with other respected organizations such as The Ponemon Institute.
This particular report on RSA certificate vulnerabilites, written by JD Kilgallin, states that the company collected and analyzed 175 million RSA certificate public keys — 75 million they discovered on the internet, plus 100 million that were available through certificate transparency (CT) logs. They used a single Microsoft Azure cloud-hosted virtual machine and a greatest common divisor (GCD) algorithm for shared factors to conduct their analysis.
Here’s what they discovered:
- Large numbers of RSA public keys can be collected through multiple sources and mined for common key factors.
- 1 in 172 certificates use keys that share a key factor with other certificates.
- They were able to crack nearly 250,000 distinct keys that correspond with 435,694 digital certificates.
- At least 435,000 weak certificate keys are vulnerable to “factoring” cyberattacks that exploit a key-related vulnerability.
- The majority of the vulnerable certificates were found on emerging IoT devices and network appliances.
The big takeaway here is that some IoT device manufacturers are using random number generators that lack strong entropy. It’s more a matter of operator error than an actual weakness in the RSA algorithm itself. As a result of using random number generators (RNGs) with low entropy, they’re generating prime numbers with poor randomness, which leads to the generation of private keys that can be compromised more easily.
But what does this mean in terms of information security?
Kilgallin cautions the following:
In 2019, with the large number of devices on the Internet and in other data sets like Certificate Transparency (CT) logs, this attack presents a serious threat if proper precautions are not in place. As the number of keys grows, it is more likely that weakly generated factors in RSA public keys will be discovered. Coupled with the availability of cheap computing resources and sensitivity of communications, the attack is as potent as ever.”
How Factoring Factors into RSA Key Vulnerabilities
At the most basic level, RSA public keys are the result of two large, randomly generated prime factors. They’re created using random number generators. This means that the entire security premise of the RSA algorithm is based on using prime factorization as a method of one way encryption. So, in other words, it’s operating under the assumption that no one can determine two randomly-generated prime numbers within a reasonable amount of time — that no one can crack the encryption of an SSL/TLS certificate until long after it’s replaced or expired.
Well, considering that it took a group of researchers more than 1,500 years of computing time (across hundreds of computers) to factor a 232-digit algorithm, that assumption seems plausible. But in reality, RSA is sometimes not as secure as we’d like it to be. It’s not that RSA itself is insecure — it’s that some companies implement it in a weak way.
That’s because some random number generators aren’t really that random. Furthermore, considering that the same RNGs are frequently used time and again, it reduces their effectiveness. If RSA public keys are generated with poor randomness, it means they could be vulnerable to a factoring cyberattack.
In this type of attack, cybercriminals collect large sums of public keys from the internet and analyze them to determine whether any two share the same factor. If two RSA moduli share one prime factor, it could result in a collision when applied to a large dataset. What this does is allow the actor to crack the corresponding private key.
All of this leads to this concern:
As the number of keys grows, it is more likely that weakly generated factors in RSA public keys will be discovered. Coupled with the availability of cheap computing resources and sensitivity of communications, the attack is as potent as ever.”
Yikes. But there is a bit of light at the end of the tunnel.
Why You Should Use CA-Issued Certificates Instead of Non-Trusted Certificates
According to the report concerning the factoring attacks, “only 5 of 100 million certificates found in a sample from Certificate Transparency logs are compromised by the same technique.” What this means is that only the five compromised certificates found in CT logs were publicly-trusted (and no longer in use online) — the rest were “self-signed, privately-rooted, or device certificates.” But, still, that’s five too many for our taste.
We’ve talked about the risks of using self-signed certificates in external-facing applications in the past. It’s one thing to use them on intranets and internal-facing applications; it’s another to use them to secure sites or devices that are discoverable via the internet.
The discrepancy between the number of CA-signed certificates that were compromised and the others, the researchers say, is likely due to IoT devices being more easily accessible on the internet and by the design constraints and entropy limitations of power-restricted devices.
In the report, Kilgallin says:
These concerning findings highlight the need for device manufacturers, website and network administrators, and the public at large to consider security, and especially secure random number generation, as a paramount requirement of any connected system.”
We keep talking about RSA encryption, RSA algorithms, and RSA keys. But what exactly is RSA itself? Let’s take a moment for a brief review for those of us who aren’t as familiar with this type of cryptography.
A Quick RSA Refresher
RSA, named after the MIT cryptographers who created it (Ron Rivest, Adi Shamir, and Leonard Adleman), is one of the two most popular public key encryption algorithms in use today. In SSL/TLS, it can be used for digital signatures and key exchange to establish a secure, encrypted communication channel. This way, you don’t leave your sensitive data at risk by transmitting it through a non-secure channel.
The RSA algorithm is comprised of four essential components:
- key generation
- key distribution
- encryption
- decryption
But, wait, we’re talking about the RSA algorithm. I thought we were supposed to be talking about RSA encryption keys?
We are… in a roundabout sort of way. RSA refers to both a signature algorithm (a cryptographic operation) and an encryption key pair. The RSA algorithm is used to generate an RSA key pair that includes both private and public keys. The first generates digital signatures, whereas the second verifies those created signatures.
But when we talk about an encryption key, what do we really mean?
What Is an Encryption Key?
A cryptographic key, in a nutshell, is a string of randomly-ordered bits (binary digits) — meaning a gargantuan string of hundreds or even thousands of 1s and 0s. Keys are integral to modern day public key infrastructure (PKI) and encryption as a whole. Keys in cryptography are like the rice to your sushi or the cream filling for your Oreo cookies — they’re essential components.
In the olden days (you know, before modern technology), a key was the secret roadmap, if you will, of an encryption technique. It’s what the sender would use to encrypt the message, and the recipient would use to decrypt the message. It’s much the same today, but instead of using hand-written keys that are written in invisible ink or hidden away, they’re digital bits of information that are transmitted electronically.
A key can be either asymmetric or symmetric. RSA keys are asymmetric. Every asymmetric key comes in a pair of mathematically-related but different public and private keys, and each key serves as different purpose — to encrypt (public key) and to decrypt (private key) data, as well as to create a shared key.
If a certificate’s RSA public key that was generated with weak entropy is targeted through a factoring attack, then its shared prime numbers could be used to derive the certificate’s private key, making RSA essentially useless.
But, thankfully, RSA isn’t the only hitter in the game. There’s another type of key that we haven’t mentioned yet — ECC.
Why ECC Needs to Take on a Bigger Role in PKI
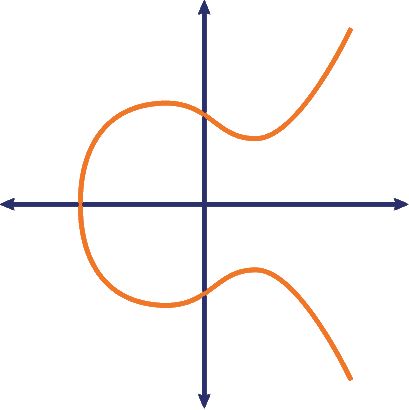
ECC, or elliptic curve cryptography, is an approach to cryptography that offers greater security and performance than RSA. That’s because it doesn’t rely on random number generation. Instead of RNG, ECC takes advantage of the math behind elliptic curves. If you don’t know what I’m talking about, think back to your school days and the joys of plotting using coordinates on the Y- and X- axes (yeah, that’s still a thing of nightmares for me, too).
I won’t get into the actual calculations of elliptic curves here — you can read more about that in one of our other blog posts on ECC. But the point here is that it’s a public key cryptosystem that relies on mathematical calculations based on specific points on an elliptic curve rather than a random number generator that could fail.
Another benefit of ECC over RSA is that ECC scales well. That’s because its keys are smaller, which results in less computational overhead and better performance.
| RSA Key Size (Measured in Bits) | ECC Key Size (Measured in Bits) |
| 1024 | 160 |
| 2048 (standard) | 224 |
| 3072 | 256 |
| 7680 | 384 |
| 15360 | 521 |
See what I mean?
A third advantage ECC has over RSA is that there’s a variation of it — supersingular elliptic curve isogeny cryptography — that’s also less vulnerable to concerns that stem from quantum computing. The National Institute of Standards and Technology (NIST) predicts that the public key cryptography we know and use today will fail once quantum computing becomes mainstream.
But the impact of quantum computing on existing cryptosystems is a whole ‘nother conversation in and of itself. And don’t worry, the sky isn’t falling — CAs are ahead of the curve in developing new cryptographic methods that will be quantum secure.
The drawback of ECC is that it isn’t frequently used because it’s not as widely supported as RSA. While it’s supported by most modern operating systems and web browsers — including Chrome, Safari, Firefox, and IE — ECC isn’t yet supported by a lot of the web hosting control panels (such as cPanel) as of yet. Unfortunately, this means that many website owners can’t yet use ECC even if they want to.
What Does All of This Mean for Your Organization?
Overall, the KeyFactor research showcases how weak some RSA keys are that are currently in use across the internet. It also drives home the point that organizations and device manufacturers in particular need to do more to protect the consumers who trust them to protect their sensitive or confidential information and privacy.
What this means for device manufacturers is that they need to:
- Ensure that their devices have access to sufficient entropy.
- Adhere to cryptography best practices.
- Be more crypto-agile in their approach to IoT security.
KeyFactor researchers define crypto agility as “knowing everywhere cryptography is used across your organization (i.e. certificates, algorithms, protocols, and libraries), and being able to quickly identify and remediate vulnerabilities, without disruption.”
To be crypto agile, you need to stay abreast of compromises and breaches in security and also try to stay one step ahead of cybercriminals. You also need to be responsive to changes. In IoT device security, that means you need to be able to maintain trust by keeping your devices secure throughout their lifecycles.
In PKI, it in part boils down to using automated certificate management solutions. A reliable certificate management solution provides visibility into your network and helps you to easily track, monitor, and renew your certificates to avoid certificate outages. Throw away the spreadsheets and get rid of your manual tracking processes — automation is the name of the game.
TL;DR
So, let us take a moment to summarize everything we’ve really touched on in this article. KeyFactor research shows that:
- RSA is secure, but it’s being implemented insecurely in many cases by IoT manufacturers.
- More than 1 in every 172 RSA keys are at risk of compromise due to factoring attacks.
- ECC is a more secure alternative to RSA because:
- ECC keys are smaller yet more secure than RSA because they don’t rely on RNGs.
- ECC scales well due to its lower computational overhead.
- ECC is more resistant to quantum computing.
- ECC is widely supported by all the major OS and browsers.
- Organizations and IoT device manufacturers alike need to be more crypto agile in their approach to security.


















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown