Nearly 21% of the world’s top 100,000 websites still aren’t using HTTPS
6.8% of the top 100,000 still support SSL 2.0 and SSL 3.0, too
For as quickly as HTTPS has proliferated, there are still a few stragglers out there. Quite a few actually. In fact, nearly 21% (20,911) of the Alexa Top 100,000 websites still aren’t using HTTPS.
That’s one of several interesting takeaways from WatchGuard’s Q3 Internet Security Report, which came out earlier this week. Among other interesting tidbits: despite calls to deprecate support for SSL 2.0 and SSL 3.0 from a number of different industry and regulatory bodies—they both persist.
So today we’re going to break down WatchGuard’s report.
Or at least the parts that are in-scope for us.
Let’s hash it out.
Before we start, let’s put the Alexa Top 100,000 in context
For all intents and purposes, the Alexa 100,000 doesn’t exist in a practical sense. There is no list you can pull down off the internet. They used to publish a top 1,000,000, but discontinued it in 2016. Scott Helme will occasionally publish some information on it, but other than that this data isn’t terribly accessible.
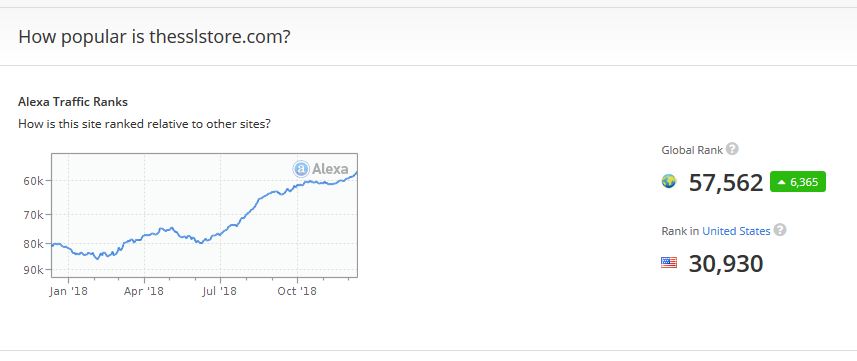
If you want know the ranking of a specific website, you can go to Alexa.com and search individually by URL.
There is a ready-made list of Alexa rankings, you just have to pay for it. And it’s not like they make it easy to find, which makes work like this even more valuable—given the barrier to entry with this kind of research.
There is some necessary context before we start slinging around statistics though. As the report states it:
We suspected the top websites make up most of the Internets users’ page visits. To prove this, we used the Alexa top 100,000 results and results from similarweb.com. Alexa compiles a list of the top one million websites in order of the most visited. Similarweb.com also compiles the top websites by the most visited and provides estimated visits per month for the most popular websites.
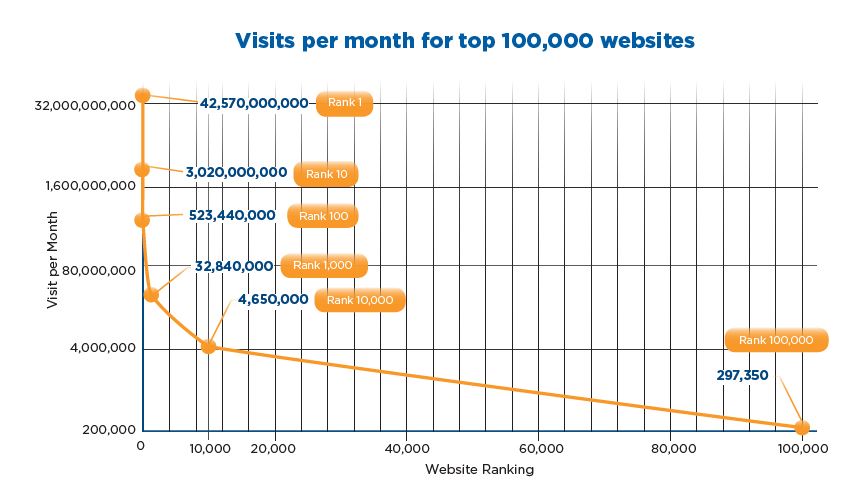
The numbers back that up. Not all is equal within the top 100,000. The traffic is largely consolidated amongst the top 100 or so websites. The difference between the world’s top site (Google) and the world’s 100,000th is staggering, with no. 1 receiving over 143,000 times the traffic the 100,000th site receives each month.
Or to put that in even starker terms: Google receives as much traffic every 20 seconds as the world’s 100,000th most trafficked website receives in one month. Here’s a visualization of how the traffic stacks up across the top 100,000, courtesy of WatchGuard.
Now let’s get to the fun stuff.
Nearly 21% of the world’s top 100,000 websites still aren’t using HTTPS
Let’s start right at the top with the most worrisome statistic: one in five of the Alexa Top 100,000 websites is still being served via HTTP. At this point it feels like I’ve been beating this dead horse for three years (I have), but we should be past the stage where whether to use HTTPS is even a conversation.

The internet was not designed to be secure because it didn’t need to be secure when it was designed. I realize that’s a confusing sentence, but at the time the internet was being developed and these protocols were being created, there wasn’t a whole lot of private, sensitive information on the internet. Commercial activity was banned back then, the main use case was the free exchange of information between government entities and academia.
Obviously, that couldn’t be further from the reality of today’s internet. And just like cars didn’t have seatbelts when they were first created and we had to mandate them later, we’ve now mandated that websites should be connecting securely via port 443 instead of spraying plaintext from port 80. HTTP connections are not secure. Anyone that’s eavesdropping on any of the dozens of devices your connection routes through on the way to its destination can easily harvest or manipulate any information being exchanged.
Seriously, we wrote about this a few weeks ago, if people actually knew how many points their connection passes through when they visit a website, the mere mention of HTTP would be met with pitchforks and torches. Even Google – of the ‘don’t be evil’ ethos – has been kneecapping websites for not using HTTPS.
So, with that in mind let’s check out the breakdown of websites in the Alexa top 100,000 that use HTTPS versus the incorrigible websites still being served over HTTP.
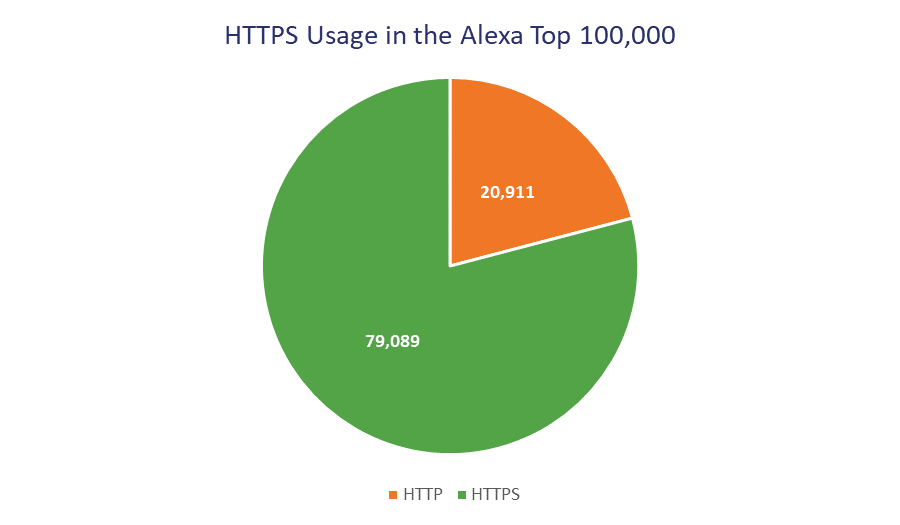
Again, the majority of these websites are going to be towards the back half of the top 100,000, but 20+% is not negligible, either. Clearly there is still plenty of work to be done on the HTTPS migration front.
6.8% of those HTTPS websites still support SSL 2.0 and/or SSL 3.0
Let’s talk about SSL and TLS protocol versions. And this harkens back to an old conversation about the difference between SSL and TLS. SSL or Secure Sockets Layer was the original protocol, developed in the mid-90s by Netscape. The initial version, SSL 1.0, never got off the ground. SSL 2.0 was published but short-lived. SSL 3.0 was the final iteration of the SSL protocol, after that it became TLS or Transport Layer Security, which is a similar protocol, but the two aren’t necessarily interchangeable, either.
We’re currently on TLS 1.3. Currently, best practice is not to support SSL 2.0 or SSL 3.0 – both are considered unsecure as a result of known exploits like POODLE and DROWN – with TLS 1.0 and TLS 1.1 due to be completely deprecated by 2020 (the payment card industry has already mandated this deprecation).
So now let’s look at SSL/TLS version support across the Alexa top 100,000. We’ll start by looking at the highest protocol supported:
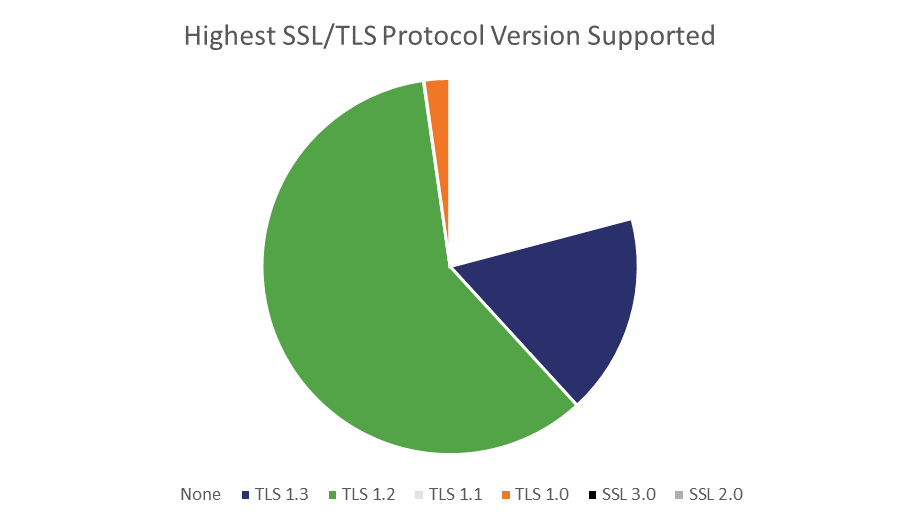
| None | TLS 1.3 | TLS 1.2 | TLS 1.1 | TLS 1.0 | SSL 3.0 | SSL 2.0 |
| 20,911 | 17,345 | 59,830 | 53 | 2,221 | 5 | 0 |
There were some interesting tidbits that came up when WatchGuard rolled up its sleeves and really got elbow deep in the data. For instance:
- 24 websites tested support SSL 2.0, but not SSL 3.0
- All but five of the sites that support SSL 2.0 or SSL 3.0 do support higher versions
- 349 sites that support SSL 2.0 support its weakest cipher suite
- Two sites only support TLS 1.3 and won’t downgrade to previous versions
- TLS 1.1 appears to be the redheaded stepchild of the TLS family
On the plus side, TLS 1.3 adoption seems to be going well, with just over 17% of the top 100,000 now supporting it.
Getting back to outmoded SSL/TLS protocol versions though, the five sites that don’t support anything above SSL 3.0 definitely need to get it together, but there’s also a disturbing number of websites that support more recent versions, but still haven’t deprecated support for those outmoded SSL protocols yet.
This is important because it opens the site and its visitors up to downgrade attacks that can basically render the encryption useless.
In our opinion, there is no good reason for these sites to support SSLv2 or v3. Luckily, many of these sites will still accept a more secure protocol when offered. However, retaining support for older SSL protocols can allow hackers to force downgrade attacks.
Well said. Here’s the breakdown, and keep in mind these figures only include the 79,089 websites using HTTPS:
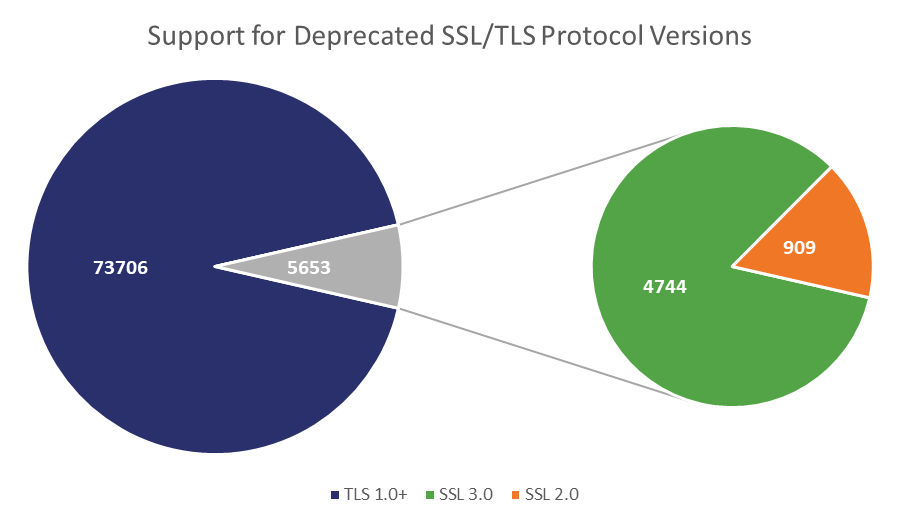
For the statistic-minded, that equates to about 5.7% of the top 100,000 sites supporting SSL 3.0, while an additional 1.1% also support SSL 2.0.
Again, given the breakdown of traffic across the Alexa top 100,000, these statistics can feel a little overblown. But this is still a good barometer for the general health of the SSL/TLS ecosystem. There’s progress on one end with over 17% of the world’s top sites now supporting the recently finalized TLS 1.3. But, at the other end of the spectrum we have websites dragging their feet on version support while they continue to exercise lax cybersecurity.
We’ll end with this: there are plenty of things in the world of cybersecurity that are beyond the control of even the most skilled of professionals. Connection security is not one of those things. Any website can have a well executed SSL/TLS implementation. And every website should.
It’s low hanging fruit and the price for not taking the time to get it right can be steep.
As always, leave any comments or questions below…




















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown