The Ultimate Guide to Key Management Systems
If Your Private Key Gets Compromised, So Will Your Encrypted Data – It’s Why Key Management Systems Are Critical For Any Business Using Encryption
Do you know where your car keys are right now? Your house keys? Considering how important they are, we hope so (or else you’ll be taking an Uber home and then calling a locksmith). You also probably have a set place for them to reside when you aren’t using them – somewhere secure, like inside your house or in your pocket.
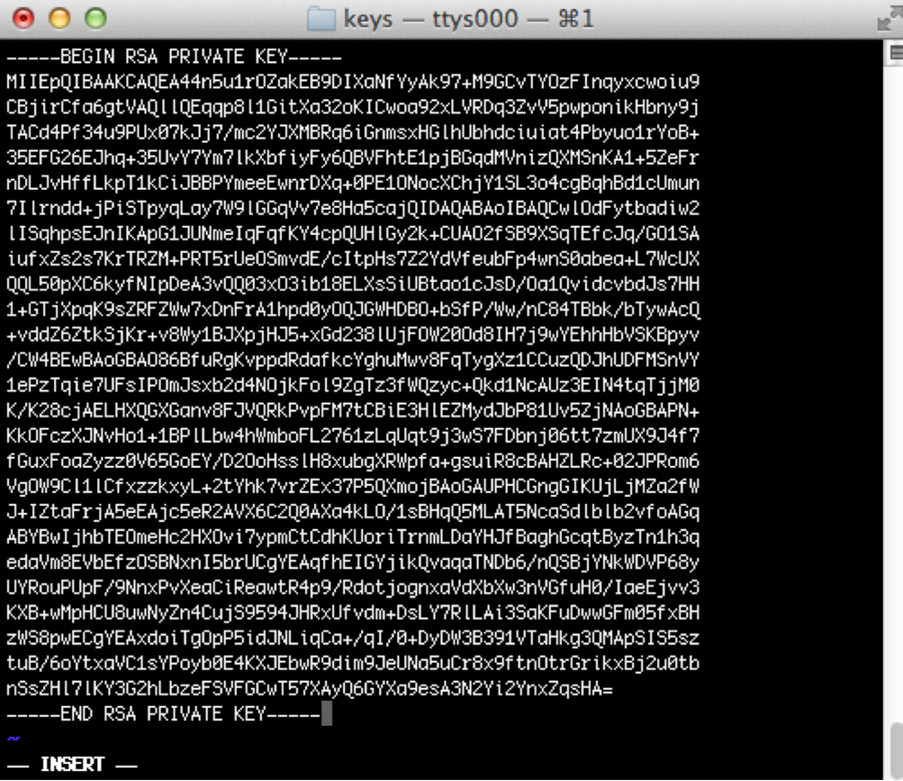
If you’re using encryption for any purpose, then you should have a similar system in place for your private keys. They are the critical piece of the cryptographic equation that, when combined with an algorithm, is the key (pun very much intended) to transforming encrypted ciphertext into plaintext that you and I can read.
One of the best things about encryption is that, if used properly, it is essentially impossible to crack. The private keys are one of the weak points, however. If someone gets their hands on yours then they’ll be able to decipher the sensitive information that you intended to keep safe and secure. Thus, cryptography keys are one of the most crucial assets that any company has, with the value of the key being equal to that of your most vital data.
What’s the best way to keep your encryption keys safe from cybercriminals? That’s where key management systems come into play. They play a critical role in protecting and managing your keys, which can be especially difficult as a business scales and a handful of keys suddenly turns into hundreds, thousands, or more.
So, what does key management mean, exactly? What are the benefits of using a key management service? And what are the different types of key management platforms?
Let’s hash it out.
What Does Key Management Mean?
When we talk about key management, we’re referring to all the tasks relating to cryptographic keys in an encryption system – creation, usage, storage, exchanging, archiving, deleting, and replacing. The overall goal is to protect every key that an organization has, preventing attackers and unauthorized users from getting their hands on the data that has been secured via encryption.
Nowadays, companies possess more data than ever, with significant portions of it being sensitive information that must be protected. Because of the potential value of this data to cybercriminals, more and more businesses have turned to encryption to protect against an uptick in security breaches, prevent costly data losses, and remain compliant to regulatory requirements. It’s now to the point that having thousands of cryptographic keys is commonplace, with key management systems (KMS) becoming the primary way of safely, securely, and efficiently handling them all.
Key management covers all of the keys in a cryptosystem at the user level, between either users or the system itself. An effective key management system should be robust and have comprehensive policies for:
- Key life-cycles – From key generation to activation to expiration and finally, destruction.
- Physical access to the key server
- Controls for accessing the key servers, which should only be permitted for essential business functions
- User-based access controls, granted to the least possible number of personnel
There are three broad approaches that can be taken for key management systems:
- Decentralized – where end users are fully responsible for the own key management and the organization itself does not handle key governance
- Distributed – each department handles key management per their own processes and policies, with coordination between teams not required
- Centralized – there is a single policy that covers the entire organization, with every team, department, and user following the same protocols
We recommend a centralized approach in the vast majority of situations, finding that one single system is much easier to manage (with less potential for mistakes or oversights) and avoids contradictions or conflicts between teams or users. Even if different departments have drastically different needs, it is still better to make sure that everyone is on the same page as far as the basic protocols and requirements. Centralize your KMS as much as possible.
Key Management Challenges
Without a proper management system in place, keys can be lost or compromised, resulting in lost access to critical data. Unfortunately, key management gets harder and harder as the size and complexity of your cryptographic ecosystem increases. Key management systems are designed to address the challenges that organizations face when dealing with cryptographic keys, things like:
- Weak keys – The length of the key should be sufficient to protect against brute-force attacks for the period of time in which the data needs to be protected
- Improper key usage – Only one key should be generated for any specific purpose
- Key reuse – Using a single key for multiple tasks increases risk and is unnecessary
- Poor storage practices – Keys should never be stored on the same server or database as the data they’re protecting
- Key transport – When moving a key between systems, it should be encrypted with a pre-shared transport key to prevent eavesdropping or theft while in-transit
- Governance – Organizations should have processes and policies in place to control access to keys
- Scalability – Manually managing just a few keys isn’t too difficult, but that changes when dealing with large quantities
The Benefits of Key Management
Now let’s go into more detail regarding the benefits that key management bring to a business and the reasons for implementing such systems.
Risk Reduction
The features of key management systems help boost security thanks to technical elements that help prevent lost, stolen, or misused keys by:
- Physically safeguarding keys from malicious third parties
- Implementing role-based access controls to limit key access as much as possible
- Making key rotation an automated process
- Immediately revoking and deleting keys that could potentially be compromised
- Maximizing the availability of keys
- Only generating high-quality keys
- Logging key usage and providing audit trails
Compliance
Many organizations turn to encryption because it’s a requirement of local laws or industry regulations. The specifics of the requirements can vary widely depending on industry, location, and other factors, but no matter what, companies want to avoid the costly fines and penalties that result from non-compliance.
Therefore, key management systems act as a kind of insurance, adding an extra layer of security for data that must be kept safe and confirming that the necessary precautions have been taken ahead of time in order to remain compliant with standards like:
Cost Reduction
Key management systems are designed to simplify, automate, and scale, which translates to reduced costs for organizations by:
- Getting rid of inefficient manual processes
- Centralizing key-related tasks
- Minimizing human error
- Automating different processes
- Providing a smooth way to scale for growth in key quantities
- Reducing the time needed to ensure compliance and perform audits
- Prevent fines in the case of compromised keys
Data Protection
It’s the primary goal of encryption in the first place, and key management systems help maximize data protection. It empowers businesses to be selective about key access, only allowing certain employees, applications, or devices to access the keys, and thus the encrypted data they protect. The controls provided by key management systems play a crucial role in preventing valuable information from making its way into the hands of unauthorized or hostile users.
Key Management Platforms
If a simple spreadsheet or list of keys sounds like a good idea, think again. Modern key management systems give users the ability to easily and efficiently manage their keys at every point in the lifecycle. There are different types of key management platforms that have different advantages and disadvantages depending on the needs of the end user. Regardless though, there’s a few attributes you always want to look for:
- Compatible with different key types and formats
- Secure user authentication methods
- Automates repetitive key tasks
- The ability to customize access controls
- Uses a certified hardware random number generator when creating keys
- Physical protection of stored keys via tamper-resistant hardware
- Provides tamper-proof logs
As far as the platforms themselves, they can be broken down into a few basic types:
HSM
HSM stands for hardware security module, and is a kind of server that has additional levels of security levels in order to prevent breaches:
- Tamper-Evident – Using tamper-evident stickers, seals, or coatings on any removable elements such as covers or doors
- Temper-Resistant – HSMs make use of what’s known as “tamper detection circuitry” that erases all sensitive data if any kind of tampering is detected
- Tamper-Proof – The outside layer of the HSM is completely hardened with latches, screws, and other elements that prevent the kind of tampering that could grant access to an attacker

HSMs can be used to generate keys, keep them safe from electronic or physical attacks, and make use of the keys within while performing encryption or decryption tasks. An HSM can be used as a key management system, but there are downsides:
- Lack of automation and intelligence – many of the lifecycle tasks still must be performed manually, which consumes resources, takes time and is prone to errors
- Scalability becomes an issue as the amount of HSMs increases
- There can be issues when attempting to securely distribute keys to outside entities
Hosted HSM
This is the same as above, except that the HSM is in the cloud, hosted by a third party provider. These are ideal for companies that are lacking in security resources and can’t properly implement an HSM themselves or want to move their security off-site for any other reason. The same hardening measures are still present on the HSMs themselves, they’re just in a different physical location than the end user.
Virtual
Virtual instances of key management systems offer a few different advantages over HSMs. First off, deployment is usually a much quicker process. HSMs are a physical product that need to be shipped somewhere. Then, a physical installation is needed. A virtual instance on the other hand, can be downloaded from a vendor’s server in a few minutes and no physical installation is required. Virtual systems also provide more flexibility than HSMs, since they can be installed on any machine that supports the virtual platform running the key manager, such as VMWare.
The virtual element can also be a downside, however. Because there’s no physical components, the software of the key manager cannot be FIPS 140-2 validated – it can only be FIPS 140-2 compliant. If you’re required to have FIPS-140-2 validation by any particular regulations, then you’ll have to go with an HSM instead. Usually, though, the level of security given by a FIPS 140-2 compliant key manager system is more than enough for the average company.
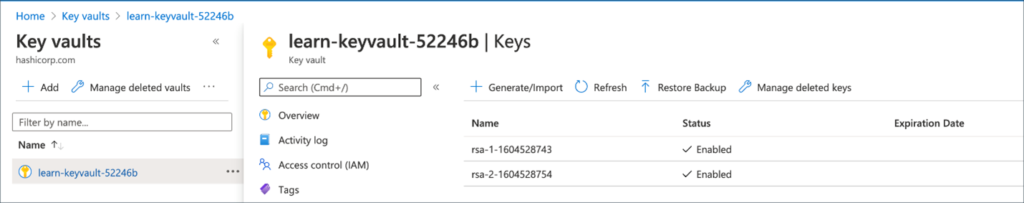
AWS, Microsoft Azure, and Similar
A key manager system can also be dedicated, or “as a service.” This kind of configuration is offered by cloud providers like Amazon Web Services (AWS) or Microsoft Azure, which have marketplace offerings in addition to their own key management as a service (KMaaS) systems. These systems are usually multi-tenant, which can be viewed as a negative since it means that several different end users will have their keys stored on the same key manager instance. For clients with security concerns, this type of system is not ideal. Because of this, dedicated services are also usually offered by providers via independent vendors.
The Keys to Proper Management
It’s critical that every organization make key security a high priority, no matter what type of key management system they end up going with in the end. Key management systems make life much easier for end users, while maximizing security at the same time. Sensitive data needs to be restricted, and key management systems provide the kind of organization and control that will ultimately keep it out of the hands of attackers. By having the right key management system in place and following key management best practices, your organization will have peace of mind that it’s most important information will stay safe.




















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown