Zoom Encryption, Whatsapp Encryption…Wait, Let’s Not Forget About Email Encryption
While you try to lock down your windows, your door could be wide open.
Many of my friends ask me if I get bored writing about encryption day-after-day. Well, this question is quite understandable as they think of encryption as some boring, nerdy topic. It might look lifeless on paper, but it’s actually full of new developments, debates, allegations, and controversies. In the last week or so, we’ve witnessed all of it. Yes, I’m talking about the controversy around Zoom, the popular videoconference app.
But while Zoom’s security holes dominate the headlines, there’s an elephant in the room: millions of unencrypted emails are sent every day, many with sensitive data inside. So, what are the security risks with Zoom, and could the lack of email encryption be an even bigger risk?
Let’s hash it out.
Zoom’s Not-So-Secure Encryption
After a report by Bill Marczak and John Scott-Railton revealing a few Zoom security vulnerabilities came out on April 3rd, it’s become quite a hot topic–it’s quite likely that you’ve heard about it even if you don’t follow cybersecurity news closely. The security researchers discovered several critical security issues in Zoom, and all of the problems are related to encryption – one way or the other, including:
- Insecure encryption mode
- Encryption keys routed through servers in China
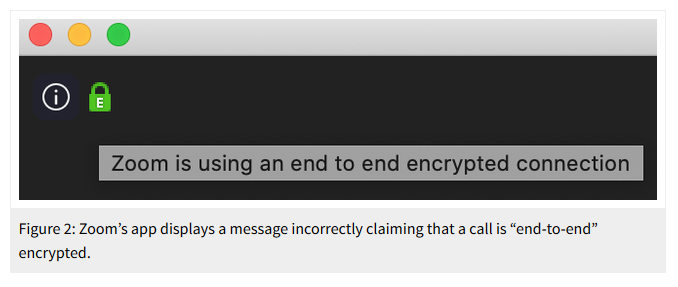
All of this has come at the time when people are working remotely, and they’re using video conference platforms like Zoom more than ever before. Thanks to these revelations made against Zoom, giants such as Google and Space-X have already banned the use of Zoom. This has had its ripple effects, and many small and medium organizations, too, have stopped using Zoom.
This security awareness is definitely a good thing, but it has irony written all over it.
Irony: Concerned About Zoom but Not Email Encryption
Thanks to the scary headlines and the current pandemic the world is going through, this news about Zoom has reached far and wide. (And that’s a good thing—we’re always excited to see increased security awareness!) As a result, even ordinary users have started looking for more secure alternatives. But unfortunately, many of the people (rightly) concerned about Zoom don’t encrypt their emails despite that the fact that many emails contain much more sensitive information compared to video conferences.
Wait, Emails Aren’t Encrypted?
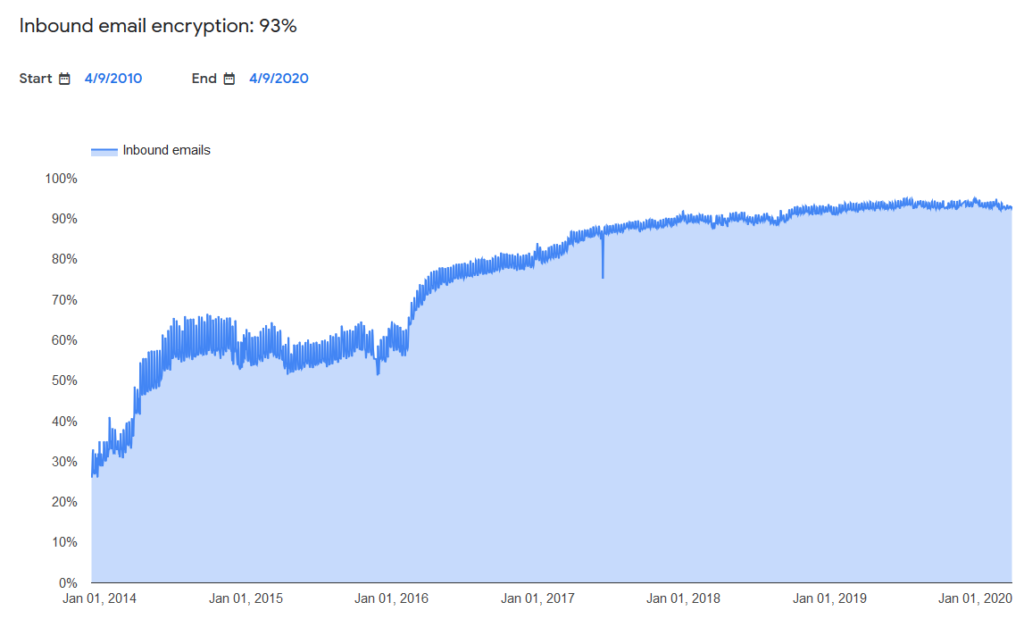
Now you might ask: aren’t emails encrypted by default? Well, they are, and they aren’t. According to Google’s Transparency report, 90% of outbound & 93% of inbound emails recorded by Google are encrypted by installing SSL/TLS certificates on the web servers. There are some concerns regarding Google’s methods of recording the data, but let’s assume the real number is around 90-95%, which is undoubtedly a good thing.
However, encrypting email transmission is just one part of the email encryption story. The other part, which many organizations with private servers ignore, is encrypting emails at rest. So when emails are resting on your email server without encryption, they are being stored there in plaintext. So, if a hacker breaches your server they can extract your sensitive information such as organizational information, financial information, research, etc. If you recall the Hillary Clinton email controversy, that’s part of what happened there.
Encrypting email transmission is good, but it doesn’t encrypt the email itself. The email remains completely vulnerable to hackers when it’s sitting on the server.
Why Email Security Should be on Your Top Priority List
Email might be one of the oldest modes of virtual communication, but it’s still the most preferred method when it comes to business communication. Around 293 million emails are sent every day, and it’s been found that 86% of business professionals prefer using emails when they communicate for business purposes. So it’s no surprise that emails are the foremost way hackers like to breach the security of an organization. Here are some email security statistics that show why you should take email security at least as seriously as you do Zoom, Facebook or WhatsApp security:
- According to Verizon 2018 Data Breach Investigations Report, 92.4% of malware is delivered via email.
- The latest email trends report by Barracuda shows that, on average, more than four-fifths (82%) of organizations claim to have faced an attempted email-based security threat in the past year.
- 66% of organizations claim that attacks have had a direct monetary cost on their organization in the last year. Nearly a quarter of them have reported damage of these attacks to be $100,000 or more.
These statistics are just the tip of the iceberg. Email attacks are a double-edged sword—hackers often attack via email, and emails are often the target they’re trying to steal as well. Ask anyone who has suffered an email attack, and you’ll know why it’s such a big deal.
Most email servers won’t be filled with government secrets that could trigger international diplomatic incidents, but most company email servers do have more than enough passwords, employee data, and customer data for a hacker to wreak havoc with—that’s why email encryption is so important.
S/MIME Certificates: A Wall to Protect Your Emails
When you’re storing every email conversation on your server in plaintext, you’re basically sending an invitation to an attacker to attack your emails. There are lots of ways hackers get their hands on emails–they could get your emails by taking control of your server, by infecting your server with malware, by fooling one of your employees through phishing, by attacking the recipients of your emails, etc. Not only could they steal your emails, they could tamper with your emails if you haven’t protected them. You might not be able to stop all these attacks, but one thing you can do is store these emails in an encrypted form so that even if they’re stolen, they remain undecipherable, thereby increasing overall security and protecting your organization’s privacy.
That’s where S/MIME (Secure/Multipurpose Internet Mail Extensions) certificates come in. These certificates work vie the S/MIME protocol to increase email security.
An S/MIME certificate…
- Facilitates email authentication by showing the verified sender of the email. Therefore, an S/MIME certificate makes sure that both the parties — recipient and sender — know who they’re communicating with.
- End-to-end encrypts the emails (including while stored on email servers) so that no unauthorized 3rd-party can see or tamper with your emails.
In simple words, an S/MIME certificate builds a wall around your emails that hackers will find challenging to cross. Want to start protecting your emails? Here’s everything you need to know about S/MIME certificates, or you can get your certificate(s) right on our website:
Final Word
Sometimes, there’s so much buzz surrounding one specific topic that we forget to look at the bigger picture. That’s exactly what happens whenever a controversy surrounding encryption on platforms such as Zoom, Facebook, WhatsApp, etc. comes up. I’m 100% in support of improving security on these platforms, but let’s not forget to also secure our emails, which are probably a much bigger vulnerability for the typical organization. There’s no point in locking down your windows while keeping the door open. Right?



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown