The Final Countdown To The End of SHA-1
Starting 2017, SHA-1 Warnings Will Get Ugly
We have written about SHA-1 a lot, but it can’t hurt to have one more reminder. We are only a few months away from 2017, and when we do enter January it will be the end of SHA-1. Seriously. Very very dead.
If you do not know about SHA-1, here is a one paragraph summary: To prove authenticity of SSL certificates, computers check the certificate’s signature. This signature is created with a cryptographic algorithm. For years, SHA-1 was the most widely used algorithm but it is now insecure and has been forbidden in all new certificates since the beginning of this year. Instead, you should be using SHA-2, the new industry standard. Now you are caught up!
Currently, SHA-1 certificates are treated with safety gloves. Browsers usually take away the coveted padlock icon or display a subtle warning.
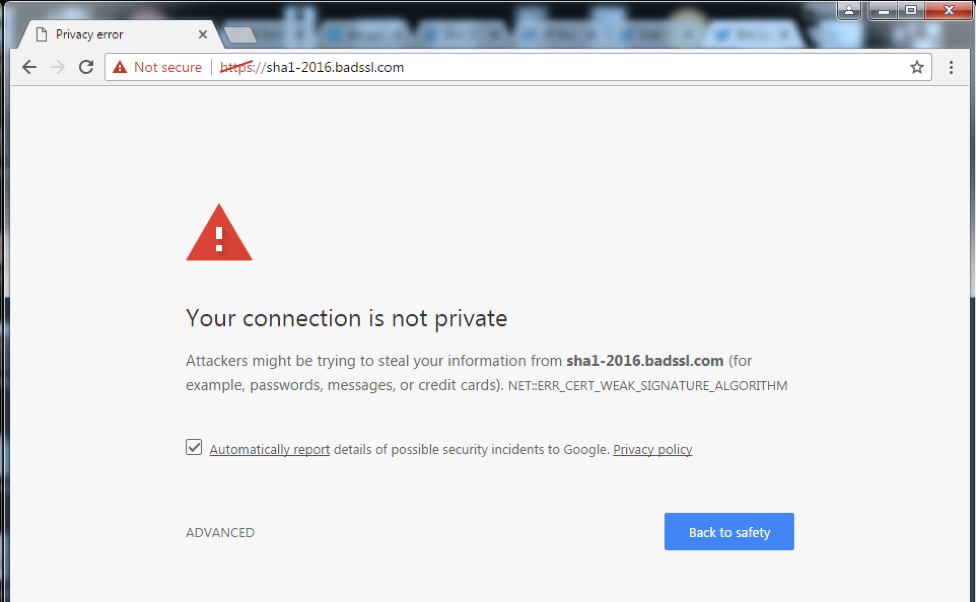
But In 2017, the gloves come off. All the major browsers – Chrome, Firefox, Internet Explorer 11, and Edge – will fully block SHA-1 certificates.
Chrome and Firefox will be the first to flip the switch. When Chrome 56 releases, which should be near the end of January, a full-page warning will be displayed for all SHA-1 certificates. Firefox 51, due out around the same time, will also show a similar warning.
Microsoft’s browsers, Edge and Internet Explorer 11, will join in shortly after. Starting February 14th, 2017, their browsers “will prevent sites [using] a SHA-1 certificate from loading,” and present an invalid certificate error.
SSL Labs, one of the most popular (and free) tools for testing your website’s SSL configuration, will also be giving poor grades to SHA-1 certificates in 2017.
The errors in all these browsers will be overridable, but with warnings this severe you should expect the vast majority of users to leave your site. And eventually browsers will remove any bypassing altogether.
These behaviors will not apply (or be configurable) for locally imported/manually-installed roots. So, those of you still using SHA-1 with local trust you will have the ability to turn these off.
If you are still using SHA-1 you have very little time to get upgraded to a SHA-2 certificate. Remember, it is no longer possible to get publicly-trusted SSL certificates that use SHA-1. Even if you have an existing SHA-1 cert valid in 2017, browsers will still apply this treatment.
If you have any questions about SHA-1/SHA-2, or are still using SHA-1, please get in touch or leave a comment. We are here to help.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown