19 Security Awareness Statistics You Should Know Before Offering Training
Knowing what to focus on can be tough when planning what to cover in your organization’s cyber security awareness training. Hopefully, these security awareness statistics will help you identify “trouble” areas that you’ll want to cover with your employees
Cyber awareness training is key to helping secure your organization’s “human firewall” (i.e., your employees). Your employees’ ability to recognize cyber threats depends largely on their knowledge of common cyber attack methods and tactics. If they don’t know what to look out for, how can they protect your organization against those threats?
Cyber awareness training is part of the NIST Cybersecurity Framework (v1.1), which falls under the Protect core function (PR.AT). It’s about educating your employees, partners, or other relevant parties (such as contractors) on cybersecurity-related threats, responsibilities, policies, and procedures. It’s also critical in helping organizations comply with industry data security and privacy regulations.
Unfortunately, only 25% of organizations allocate “two or more hours” to formal training annually, Proofpoint’s 2022 State of the Phish report shows. And what makes matters worse is that employers are “punishing” and “disciplining” employees for real and simulated attacks even though they hardly receive training. Not good.
This article will focus on 19 important security awareness statistics you should know before offering your next cyber awareness training event. The idea here is that you’ll know what areas to focus on and how your organization stacks up against others when training your team. It’s time to improve your organization’s cybersecurity posture and drive home the importance of cyber security awareness with your employees (and other network users).
Let’s hash it out.
19 Security Awareness Statistics That Can Help You Tailor Your Training Offerings
When it comes to making your organization’s cyber defenses as secure as possible, there are steps you can take to make this happen. This includes hardening your technical defenses by implementing email server security best practices and carrying out regular cybersecurity risk assessments. But there’s more that you can do to take your security to the next level — and it involves training your employees to increase their awareness. (This is known as security awareness training or cyber awareness training.)
Here are 19 cyber security awareness statistics you should know when planning your organization’s next training session.
1. 82% of Data Breaches Are Tied to “Human Element” Related Security Weaknesses
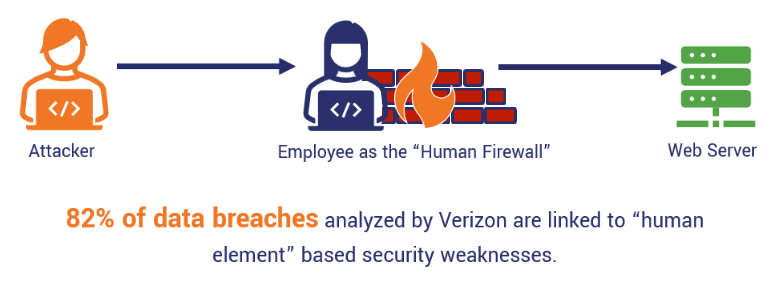
Alright, first up on our list of security awareness statistics is data from Verizon. The communication giant’s 2022 Data Breach Investigations Report (DBIR) shows that eight in 10 data breaches involved human-related vulnerabilities. For example, this includes employees falling for phishing attacks, other social engineering tactics, and bad guys using stolen employee credentials. This is why we decided to make this No. 1 on our list of security awareness statistics.
So, how can you mitigate these vulnerabilities? One of the most effective ways is to arm your employees with the knowledge they need to recognize potential threats and know how to safely respond to them. This includes:
- Providing real-world examples of phishing scam emails, text messages, and other examples of social engineering tactics.
- Educating employees about what they should do when they receive or open suspicious messages.
- Informing them about who they should report security-related issues and concerns to within your organization.
- Helping them understand the processes for reporting these issues.
2. 13% of Ransomware Cyber Crime Targets Fall Within the Consumer/Retail Category
Data from Microsoft’s October 2021 Digital Defense Report shows that consumer and retail businesses are the leading target for ransomware-related cyber crimes. Their Detection and Response Team (DART) showed that the other two most targeted sectors included manufacturing/agriculture and insurance/financial, which tied with 12%.
3. 69% of Companies’ Are Increasing Their Investments in Their Cybersecurity Budgets
It seems that more companies are starting to put their money where their mouths are. PwC shares in its 2022 Global Digital Trust Insights report that nearly 70% of organizations predict to increase their cybersecurity budgets in 2022 — nearly a quarter of which expect those budgets to increase by at least 11%.
This research aligns relatively well with what Gartner expects — the research firm predicts that 66% of CIOs intend to increase their cybersecurity and information security investments this year.
4. 36% of Organizations Report Implementing At-Scale Cyber Security Awareness and SecOps Cross-Training
More than one-third of organizations report that they’ve implemented security awareness training and cross-training security operations at scale, according to PwC’s global digital trust report. Another 16% report that they’ve already experienced benefits from doing so, and another 46% say they’ve already started implementing or plan to start implementing these training sessions in the future.
As far as at-scale implementations go, security awareness training and cross-training security operations rank highest among the 3,602 respondents regarding how those organizations prioritize their cyber security budget investments.
5. 79% of Organizations Report Increasing Email Volume
Nearly 80% of organizations report that email usage is on the rise, Mimecast reports in its State of Email Security 2022 report. Along with this jump in email volume, Mimecast researchers also reported an increase in email-based threats over the past year — 26% of which they labeled as “significant” threats.
This shouldn’t come as a surprise considering that emails are one of the leading attack vectors in cybersecurity incidents and phishing attacks. This is why this item ranks so high on our list of security awareness statistics.
6. APWG Reports That Website Phishing Attacks Have Tripled Since Early 2020
Website phishing attacks are a big problem, but to say the issue is alarming is a huge understatement. The Anti-Phishing Working Group (APWG) reports that phishing website detections reached an all-time high (316,747 in December 2021 alone) at the end of 2021. That’s a record-setting number for APWG’s reporting history.
7. Employees’ Understanding of Phishing Dropped 15% over 2021
Survey data from Proofpoint’s State of the Phish 2022 report shows that fewer people understand the term “phishing” than you’d think. Phishing is a term that’s both an attack method as well as a category of attack methods. It’s sometimes used interchangeably with social engineering, which is a series of tactics that are used by cybercriminals to get targets to cough up sensitive information — their login credentials, employee or customer information, etc.
In some cases, some subcategories of phishing attacks (e.g., CEO fraud) can even be used to try to get you to make fraudulent wire transfers to accounts the attackers own.
Basically, it’s a way for bad guys to target your organization’s people instead of hacking their way through your cybersecurity technical defenses. (Why should they spend weeks or months trying to hack through your firewall when they can simply sweet-talk, trick, or coerce one of your employees into giving up their credentials?) So, knowing that employees are less likely now than they were last year to understand (and, potentially, recognize) phishing threats is a big deal.
8. Cyber Simulation Training Makes Employees 50% Less Susceptible to Phishing
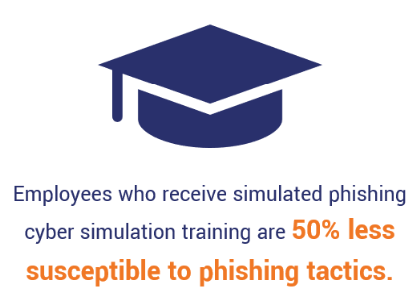
Want some good news on this not-so-happy list of security awareness statistics? Simulated phishing training seems to have a notable impact on employees’ ability to withstand phishing attacks. Microsoft’s report that we mentioned moments ago shows that when employees receive simulated phishing training, they’re 50% less likely to fall for phishing.
9. 10% More Employees Recognize What Ransomware is
Proofpoint’s State of the Phish 2022 survey data shows that while the “unsure” responses are about the same, 10% more survey respondents indicated that they are aware of ransomware. That’s all well and good, but the bigger question is: do they know how to recognize this type of method of attack before it’s too late?
10. 88% of Businesses Experienced a Ransomware Attack
Alright, we’re more than half way through our list of cyber awareness statistics. Let’s continue on with a not-so-fun stat from Veeam.
Nearly nine in 10 organizations experienced at least one ransomware attack in the previous year. Veeam’s 2022 Data Protection Trends in Small and Medium Business (SMB) study of 201 small and medium-sized businesses. However, what makes matters worse is that 44% of the respondents’ data was deemed unrecoverable due to the attacks. So, not only did those organizations face the direct costs associated with trying to stop the attacks, but they then also faced the resulting potential costs associated with:
- Trying to recover their data,
- Sustaining regulatory fines, and
- Defending against lawsuits or providing settlements.
11. Germany Leads the Way with 85% of Employees Recognizing the Danger of Email Attachments
The cyber security awareness of Germany’s workforce outperforms all other Proofpoint State of the Phish 2022 survey respondents from different countries globally. Compare this security awareness statistic to the 42% of U.S. workers who have the misconception that if an email contains a familiar logo, it must mean that they’re safe.
Considering that another Proofpoint survey shows that 80% of businesses are breached via compromised third-party vendors, this security awareness statistic is particularly disturbing.
12. 15% of Organizations Report Cybersecurity Events as the Most Common Cause of Outages in 2021
While there are many causes of outages, cyber attacks seem the most common and impactful. Research from Veeam’s (a data backup service provider) 2022 Data Protection Trends Report lists “Cybersecurity Event” as the most common and impactful reason why outages occurred 2021. This reason was followed closely by accidentally deleting, overwriting, or corrupting data and general network and infrastructure-related outages — both of which tied for second place with 14% each.
13. Organizations Rank CEO, Board Cyber Awareness Training for CEOs a Top Factor for Improving Cybersecurity
Educating organizations’ leaders is the best way to help them better serve their cybersecurity goals of creating a more secure digital society by 2030. This is according to PwC’s 2022 Global Digital Trust Insights report, which shows that survey respondents across four geographic regions — Africa, APAC, Eastern Europe, and Western Europe — view that as the top priority.
14. 88% of Board Members Saw Cyber-Based Threats as a “Significant Business Risk” in 2021
Gartner’s November 2021 research shows that nearly eight in 10 board members view cybersecurity issues as business risks. This definitely makes sense considering that cyber crime is on the rise and has been for the past several years. But what doesn’t make sense is that less than one-eighth of Boards of Directors (BoDs) have dedicated cybersecurity committee that board members participate in or lead.
Needless to say, this is something we hope to see change the next time we write about this topic and update this list of security awareness statistics.
15. Compliance is the No. 1 Cost Factor Regarding Data Breaches

IBM Security’s 2021 Cost of a Data Breach report shows that having high-level compliance failures costs organizations $2.3 million more than those with low levels. Translation: Organizations that emphasize and prioritize compliance are more likely to spend less on penalties, fines or lawsuits resulting from data breaches than their counterparts that don’t.
In a previous role, I worked at a state college. There, our president at the time hammered home the idea that every employee — whether you’re a janitor or a vice president — plays a role in helping students get to class in the best condition for learning. Virtually every presentation he made to staff and faculty included some variation of this message.
The same idea translates to your organization. Even if you’re someone whose job isn’t related to compliance directly, you still can have an indirect impact on your organization’s compliance. (Keeping up a human firewall helps you prevent sensitive data from being compromised.) Therefore, you should have at least a basic understanding of the compliance requirements and what they entail. Why? Because compliance is important and affects all our jobs in one way or another. Therefore, helping the company remain compliant is every employee’s responsibility.
Every step we take as employees — whether it’s accessing company systems or emailing information to a colleague — has a potential impact on the company’s compliance. If one employee falls for a phishing attack and their credentials get stolen, bad guys can use them to access any data or systems that employee has access to. This can result in a data breach and lead to non-compliance with various privacy regulations.
16. 62% of CloudStrike Security Cloud Attacks in Q4 2021 Didn’t Involve Malware
CloudStrike’s 2022 Global Threat Report shows that most attackers have moved beyond malware and are focused on malware-free attacks. This approach, known as Living Off the Land (LOTL) attacks, involves attackers using built-in tools and legitimate user credentials to avoid detection by traditional anti-malware and antivirus-related products.
17. 79.5% of Websites Using HTTPS as the Default Protocol
HTTPS, or the secure hypertext transmission protocol, is the data transmission protocol that makes the little padlock icon appear in your web browser when you visit your favorite websites. Basically, this protocol allows two parties to exchange secure, encrypted data. Data from W3Techs shows that nearly 80% of websites use this protocol automatically.
During your cyber awareness training events, teach your employees the importance of visiting secure websites only. But if you really want to help them (and your organization), then teach them the importance of evaluating websites and looking for the site’s digital identity information in its SSL/TLS certificate. If they can’t verify the identity of the organization that owns the website, it’s best to leave the site immediately and never provide any sensitive information.
18. 52% of Workers Report Always Using a Virtual Private Network When Working Remotely
Here’s some good news followed by bad news: more than half of YouGov-polled workers report using a virtual private network (VPN) all of the time when working remotely on a company device. Another 14% say they do so “sometimes.” But this means that everyone else either doesn’t use one at all or, if they do use one, they do so infrequently.
But why is using a virtual private network (VPN) a critical step when working outside your organization’s physical office? Because it means that they’re relying on an external network that may (or may not) be secure. This leaves their accounts and your organization’s systems and data at risk of compromise.
For example, say that one of your employees is attending an industry conference across the country. After leaving their airport, they’ve got time to kill before checking into their hotel, so they stop off at a local coffee house. When they turn on their device’s Wi-Fi, they spot “Café Complimentary Wi-Fi” and think, “jackpot!” So, they connect to it and spend a few valuable hours getting work done.
But what they don’t realize is that it’s not the coffee house’s network — rather, it’s an evil twin network (i.e., a wireless network that’s controlled by an attacker who can intercept your communications and steal or modify your data in transit). So, now, an unknown attacker now has all the login credentials your employee used throughout their connection. Now, any accounts that they logged into while connected to that network are compromised — and so are all your affected systems.
19. 70% of Users Whose Credentials Were Exposed in Breaches Are Still Using the Same Passwords
Last but not least on our list of security awareness statistics: password reuse. The rule of thumb is that if you are informed that your account has been compromised (i.e., your email address or username and password), you’ll want to update your credentials as soon as possible. This action aims to help prevent attackers from using your compromised credentials to access sensitive systems and data.
However, what’s face-palm worthy is that SpyCloud’s 2022 Annual Identity Exposure Report data shows that nearly three-quarters of people choose to reuse passwords that were exposed in breaches. This is like choosing to secure your house with a key you know your ex (husband, wife, significant other, etc.) still has a copy of — it’s just not a good idea and leaves you and your valuables at risk.
Bonus Stat: IT Users Were the Worst Offenders For Downloading Malicious Files
Data from Terranova Security’s November 2021 Gone Phishing Tournament Phishing Benchmark Global Report shows that some industries are more serious offenders than others when it comes to clicking on phishing emails or, worse, downloading malicious attachments. The top three offenders for clicking on phishing emails were education (27.6%), finance and insurance (26.6%) and information technology (25.6%).
The last one may come as a surprise since IT pros are supposed to be more knowledgeable about security-related risks than other industries. But what makes matters worse for the IT crowd is that the report data shows that IT sector end users had a click-to-download ratio that surpassed 84%. This was nearly 5% worse than Agriculture and Food and Education (79.4%), which were the next highest offending sectors. This data was collected as part of the Gone Phishing Tournament, which is a two-week phishing simulation event that involved nearly one million phishing simulation emails.
So, don’t count out any employees when it comes to requiring phishing and cyber awareness training. No matter what their role or specialization, every employee who touches your network or any company devices needs to receive regular training.
Final Thoughts on the Importance of Cyber Security Awareness
Now, we know some key cyber awareness statistics and why cyber security awareness training is so critical. So, what can you do to help teach your employees how to be more “cyber aware” and harden your organization’s human defenses?
- Integrate cyber awareness into your company culture. Help them feel comfortable reporting suspicious emails and potential security incidents without fear of reprimand or reprisal.
- Require employees to complete cyber awareness training. You’ll want to offer this training annually as a minimum. Ideally, you’ll do it more frequently — and be sure to provide it to all new employees as part of their onboarding.
- Train employees in account security best practices. Help employees understand the importance of using unique passwords for every account. Password reuse is a dangerous approach that leaves their account — and your overall organization — at risk.
- Provide real-world examples of phishing emails and websites. Looking at real examples of phishing emails and websites can help your employees better understand how to recognize potential threats.
- Carry out regular phishing simulations. Sending fake phishing emails to your employees is a great way to test their cyber awareness and knowledge to see how they respond to potential phishing emails. This provides you with an opportunity to see how they apply what they learn in your training and to identify new or additional areas to address in future trainings.
- Teach employees to use VPN to remotely (and securely) connect to network resources. Connecting to insecure networks is one of the most dangerous things employees can do. Bad guys can intercept their sensitive data — such as login credentials — in transit and use them to do a lot of damage. This is why it’s essential to teach employees to use a secure, encrypted connection when traveling, working from home, or access any company resources while away from the physical office.
- Make email signatures part of your email security strategy. Require employees to digitally sign their emails and teach them how to verify digital signatures in emails they receive from others. Cryptographic digital signatures harness the power of public key infrastructure (PKI) to add verifiable identity to emails and help protect the integrity of the messages themselves.
Alright, that concludes our list of security awareness statistics. We hope you’ve found this list informative and useful. Be sure to check back with Hashed Out for other statistics-oriented content.






































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)












5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown