Re-Hashed: 2018 Cybercrime Statistics: A closer look at the “Web of Profit”
Cybercrime will generate at least $1.5 trillion this year—and that’s conservative
Two weeks ago we discussed the impressive work done by Dr. Michael McGuire on a cybercrime study that found the industry’s profitability to be in excess of $1.5 trillion. But while that’s an impressive figure, it’s hardly the entire story.
As McGuire said, cybercrime has evolved into an entire economy rife with professionalization and filled with parallels to legitimate industries.
“The emergence of a complex and multi-layered cybercrime economy has also begun to suggest a fundamental shift in the very nature of crime itself. In this context, overt acts of crime become less central features of the criminal ecosystem when compared to the services and platforms that feed off and support crime – which become increasingly low-investment, high-yield and low-risk operations.”
The existence of “platform models of cybercrime” are, in McGuire’s opinion, comparable to “platform capitalism,” which has been a major trend in the global economy owing to the likes of Google, Facebook, YouTube, Uber, LinkedIn, etc. – companies that can make money simply by offering a platform to others and collecting data.
That has led to a spike in profitability that would make Cybercrime – were it a nation state like the US or Russia – the 13th largest GDP in the entire world. Let’s take a look at some more of the 2018 Cybercrime Statistics that give us a greater insight into how cybercrime is evolving.
Cybercrime will create over $1.5 trillion in profits in 2018
Before we get to the charts and tables, let’s talk for a second about the methodology that Dr. McGuire used to arrive at this $1.5 trillion figure. Using data from the financial industry and law enforcement, Dr. McGuire attempted to construct a conservative estimate that looked at “the current state of play.”
“By erring on the side of caution, by making projections from a small, rather than large number of revenue categories and by opting for lower, rather than higher points on the estimate range, the aim was to understand whether the assumption that cybercrime is a lucrative form of offending has any basis in what is actually happening within the cybercrime economy. The surprisingly high figures that were eventually derived certainly suggest that we need to think more seriously about the attractions and how these might be tackled. For even if the figure for total revenues from cybercrime is only accurate up to a point, the fact that it is a deliberately conservative one means that its inaccuracies at least involve only underestimates, rather than overestimates.”
In other words, there’s a very good chance that the actual numbers skew much, much higher.
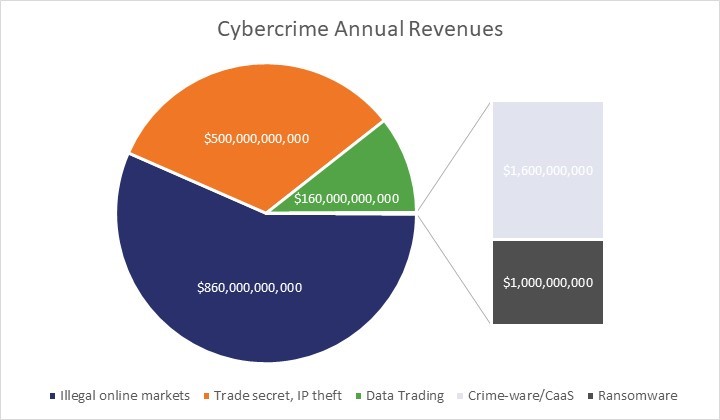
| Crime | Annual Revenues |
| Illegal online markets | $860 Billion |
| Trade secret, IP theft | $500 Billion |
| Data Trading | $160 Billion |
| Crime-ware/CaaS | $1.6 Billion |
| Ransomware | $1 Billion |
| Total Cybercrime Revenues | $1.5 Trillion |
FACT: Over 50% of cybercrime revenues are generated in online markets.
What’s not included in that figure
For the sake of this study, “cybercrime revenues are identified as any revenues arising from crimes where computers play an obviously direct role.” However, there were some categories omitted, things like mass communication scams (phone scams) were not included.
In the U.K., such frauds earned around £3.6 billion ($4.9 billion) in 2015 (CCFS, 2016), in the U.S. they earned approximately $25 billion (ICE, 2010) and in Australia, they earned around AU$94 million ($74 million) (Whitty, 2015); thereby generating an estimated total of over $29 billion.
However, reliable data on these kinds of activities was scant outside of the UK and given that they were unlikely to do much to the $1.5 trillion total figure, they were left out.
How much money does Ransomware make?
In 2016, the US Federal Bureau of Investigation estimated that Ransomware payments would reach $1 billion. Two years later that shows no signs of slowing down. Here’s a sampling of some of the highest-profile Ransomware from the past five years as well as how much money it made.
| Ransomware | Date | Profits |
| CryptoLocker | 2013 | ~$3 million |
| CryptoWall | 2014-2016 | ~$18-320 million |
| Locky | $7.8-$150 million | |
| Cerber | $6.9 million | |
| WannaCry | 2016 | $55,000-$140,000 |
| Petya/NotPetya | $10,000 |
As you can see, some of the higher-profile cases of Ransomware didn’t see much return financially. The Petya/NotPetya figure in particular is fairly eyebrow-raising given how prolific the ransomware seemed to be at the time. But, there is a distinction to be made between ransomware that was designed to make money and ransomware that was designed primarily for disruption. Petya/NotPetya would appear to be in the latter category.
“Researchers who have looked at high profile ransomware – like WannaCry or the Petya/NotPetya – found that monetisation of the ransom demanded has not been conducted very effectively. The implication being that there is a distinction between ransomware products designed for revenue generation and those designed for disruption – possibly at the behest of state actors.”
Cybercrime Operations: Big to Small
One of the most interesting aspects of the current cybercrime economy is the way it’s stratified, with large operations functioning almost as multi-national corporations and smaller operations mirroring single proprietor small businesses. Large cybercrime operations can make profits totaling over $1 billion per year while smaller operations tend to make between $30k-$50k.
How much money do cybercriminals earn?
For an individual with the right skillset, cybercrime can be incredibly lucrative. An individual cybercriminal can make upwards of half a million dollars in a year simply by trafficking in stolen data.
Like real criminality, cyber criminals can generally be broken down into levels. Not every hacker is exceptional. Some, like low-level criminals, are content to execute petty crimes that don’t pay all that well. Others, are highly specialized and only work when the money is good.
In general, cybercriminals earn about 10-15% more than their counterparts in traditional crime, with high earners taking home upwards of $167k per month, middle earners in the $75k range and low earners making 3.5k per month. Also, while a talented hacker can make somewhere near $30k on a job or two, a platform manager offering multiple card data forums can earn up to $2 million per month.
FACT: Ross Ulbricht of Silk Road reputedly made a personal fortune of over $1 billion.
What is a “Cybercrime Platform?”
To understand this concept, we need to backtrack a bit and start with a quick point on “platform capitalism.” The cybercrime economy mirrors our global economy in that it has seen a decisive shift towards a platform model, much as the rest of the world has with the likes of social media, Google, Amazon, etc.
Platforms connect people. It’s easy to get hung up on the terminology, “platform,” but really all we’re talking about are sites and companies that facilitate connections between suppliers and the consumers in need of their products and services. It makes more sense when you look at a real-world example. AirBnB is a very popular company that offers apps and a website where homeowners looking to rent their properties can connect with people that are looking to rent in their area. Similarly, Facebook connects us to our friends, Google connects advertisers with websites that will get the most out of their ads, Uber connects us a with a ride home. You get the idea.

The platforms themselves produce nothing in this process, whilst the users provide the platforms with the most precious of all commodities within an information economy – their data.
Cybercriminals and the cybercrime economy seem to be embracing this model, too. While there isn’t a ton of definitive research into these areas as of yet, we can get a pretty good top-level idea from Dr. McGuire’s work. Currently there seem to be two ways in which platform economics seem to be playing out in the cybercrime economy.
- Exploiting existing legitimate platforms
- Developing new crime-specific platforms
Exploiting existing legitimate platforms for cybercrime
Once again, there isn’t a ton of in-depth research on the topic yet as it’s a fairly recent development and cybercriminals aren’t exactly forthcoming with their business practices. Imagine that. Still there are some methods that have been observed, many of which are already in the news quite a bit.
Using existing platforms as a source for data theft and hacks
You see this in the news all the time, it seems like we cover at least one of these a week, but data breaches are a cybercriminal’s bread and butter. As we’ve already established, you can sell personal information in its raw form or use it to create bank and credit card accounts which can be sold for a small fortune. It’s also useful for various other criminal activities beyond outright theft. Small wonder major platforms are major targets—they collect boatloads of data. Recently Facebook has been in the news for a high-profile data leak. Yahoo’s breach, which may be the largest in recorded history, compromised up to 3 billion user profiles. Cybercriminals want data and they know where to look.
FACT: 4 BILLION data records of various kinds were stolen in 2016.
Using existing platforms to distribute malware
Whether it’s deceptive apps that end up Cryptojacking your device or malware that adds your system to a botnet, there always seems to be story in the news about malware being found on popular platforms. Recently we’ve seen Google crackdown on thousands of apps in its mobile app store. Facebook has had its own problem with apps. And that’s just the most direct attack vector.
Related: Google shuts down hundreds of apps in its Play Store
Cybercriminals have also learned to leverage social media to aid in their spearphishing campaigns, particularly on LinkedIn and Facebook.
With [the stolen data] in hand, phishing campaigns can be launched to download malware onto targeted corporate systems. Even better, the details of CEOs or executives can be illicitly acquired. Malware of this kind allowed the Carbanak cybercrime group to steal over $1 billion from more than 100 financial institutions (Reuters, 2015).
FACT: In 2018 Google discovered that cybercriminals had been abusing its DoubleClick network for a cryptojacking attacking.
Using existing platforms for illicit supplies and sales
Who needs the black market or the dark web? You can find illegal items like weapons, drugs and a whole range of counterfeit items on perfectly legitimate platforms already. Despite efforts to crack down on this by the platforms themselves, the activities persist. Criminals find workarounds, use code words that avoid detection and use encrypted messaging services to cover their tracks.
Recently the website Craigslist.org had to shut down parts of its online marketplace after a US law was passed that would have made the company liable for any sex trafficking activities conducted on its site. That this law, which many argue is written poorly despite it’s noble intentions, was even needed is evidence as to what a problem this has become.
Using existing platforms for money laundering
Cybercriminals can’t just show up at the bank and deposit thousands of dollars in ill-gotten gains, people ask questions. And that’s probably understating it. Try doing anything with more than $10,000 in the US and it’s going to involve some paperwork and likely some taxes and fees. That’s not going to work for you if you’re a criminal, so you’re going to need to find a way to make the money look like it was earned legitimately. Cleanly. Ergo, money laundering.

A lot of people think this is done using digital currency, and that’s true to an extent. But it tends to vary by crime, for instance ransomware profits are almost always cashed or laundered using cryptocurrency. But many other criminals launder the money through legitimate platforms like PayPal or AirBnB. For instance, a popular method is listing a property on AirBnB and then booking it with hacked user profiles that will never actually stay there. Former presidential advisor Paul Manofort is accused of a similar grift on AirBnB.
“Digital payment systems appear to be most effectively used for overt laundering activities when combined with online transactions, or as one part of a suite of other laundering methods and resources. A very common technique here is to use sites like eBay to make purchases that can facilitate the laundering. These transactions are then able to pass through the PayPal system with less suspicion and the money received will conveniently disappear.”
FACT: The United Nations estimates that between 2-5% of total global GDP is now circulating in illicit or money-laundered forms. That’s up to $2 trillion.
Using existing platforms to enable crime in general
This has less to do with cybercrime and more to do with traditional crime, but social media helps to facilitate more than its fair share of crime. While conclusive research is lacking on this subject, anecdotal evidence is high. News stories about terrorists being radicalized on YouTube or the recent Toronto tragedy where a young man that had been indoctrinated by an “incel” community drove a van into a crowd and killed ten people.
Then there are crimes like burglaries, which can be aided by social media sites – allowing criminals to case houses and figure out when their occupants won’t be present – and identity theft, cyber-stalking (which is usually linked with real stalking), etc. Given the likely volume of crimes partly or more substantially enabled in this way, the volume is probably significant. However, without more research, the true level of criminal enablement provided by contemporary platforms is likely to remain an unknown factor.
Developing cybercrime-specific platforms
As with the previous iteration of platform cybercrime, there is not yet detailed research about cybercrime specific platforms, but three variations have been observed.
Data Trading Platforms
Every cybersecurity company with a TV budget has a line in their commercials about “monitoring the dark web for your personal information.” Which is a great thought, albeit probably one that’s too late. Once it’s there, it’s there. And there are plenty of sites on both the open web and the dark web that traffic in stolen data. For cybercriminals it’s all about understanding the value of that stolen data and learning to maximize its worth using the right platforms and networks. For instance, it can be absurdly inexpensive to track down random bits of personal identifying information like addresses, birthdates and even social security numbers.
However, if you can gather enough personal information to construct an identity, complete with banking information, you can make a fortune.
FACT: In 2015, the recorded losses from card fraud totaled $22 billion.
Cybercrime-as-a-Service Platforms
Last week Dutch police shut down the world’s largest DDoS-for-hire service, “webstressor.org” and arrested six people behind it. The site had over 136,000 registered users and allowed customers with little or no technical knowledge to launch a Distributed Denial of Service attack for about £10. The service was responsible for attacking seven of the UK’s biggest banks in November of 2017, in addition to various government institutions and gaming services.
This is just the tip of the iceberg, platforms also exist where you can rent botnets, purchase known exploits and even commission specific hack jobs.
| Cybercrime Product or Service | Price (in US Dollars) |
| SMS Spoofing | $20/month |
| Custom Spyware | $200 |
| Hacker-for-Hire | $200+ |
| Malware Exploit Kit | $200-$700 |
| Blackhole Exploit Kit | $700/month or $1,500/year |
| Zero-Day Adobe Exploit | $30,000 |
| Zero-Day iOS Exploit | $250,000 |
“Buying malware is currently not a problem: it’s easy to find them on various hacker forums, and they are relatively cheap, making them attractive. A cybercriminal following this illegal path doesn’t even need any skills – for a fixed price they can get an off-the-peg package to launch their attacks at will.” says Alexander Gostev, Chief Security Expert at Kaspersky Lab.
BitTorrent and Download Sites

Pirating entertainment is nothing new, this has been going on since Napster. Perhaps the largest, most well known BitTorrent platform is Pirate Bay, which has eluded numerous attempts by law enforcement and the entertainment industry to shut it down. Some estimates hold that music piracy alone is worth upwards of $12.5-billion per year. Pirate Bay doesn’t make it’s money of the piracy itself though, it earns upwards of $6 million in annual revenues just by selling ads. That’s actually how most of these platforms make money. Sites that profit exclusively from ad sales make an average of $4.4 million per year. Even a small operation can earn around $100,000 per year selling advertising.
What is clear, is just how much more lucrative these sites are for those who manage or run them, than for many of the individuals who contribute the data, or who do the grafting to obtain it.
The problem for cybercriminals is getting the money out
Making money via cybercrime is relatively easy in theory. Where it gets difficult is getting the money out. Think about it, how do you spend the stolen money? None of this happens in a vacuum, eventually the victim is going to realize something has been stolen and they will likely come looking. How do you move money around so that you can transact with it without getting caught?
This presents a major problem for cybercriminals, and while people are quick to point out digital currency as a method for laundering money, that’s not quite as effective as many believe – owing to the fact it’s tracked and not nearly as anonymous as many hope.
Instead, cybercriminals are left trying to figure out how to use their illicit gains. Here’s how the money is stored.
FACT: 30% of the criminals interviewed in The Web of Profit study reported they had physically transferred cyber revenues or sent money via couriers, a.k.a. money mules, on airlines to deposit in foreign banks.
As you can see the vast majority of the money ends up being tied up in property. In fact, 1-2% of all the property transactions in the UK are directly funded by criminal activity. That’s about $3.7-$7.4 billion dollars per year in crime funded property deals.
Another method for laundering money and making ill-gotten gains appear legitimate is through the use of shell corporations. Cambridge Analytica was associated with a shell corporation while it was harvesting data from Facebook and the 2016 leak of the Panama Papers – a massive data leak by a Panamanian law firm, Mossack Fonseca – exposed the activities of over 200,000 such corporations, many of which were directly associated with crime. Shell corporations represent a great way to hide and launder money.
Here’s another fun fact, up to 10% of all the laundered money in circulation is a product of cybercrime. That’s about $200 billion dollars worth of crime revenues.
FACT: 95% of money mule activity has links to cybercrime.
What do cybercriminals spend their money on?
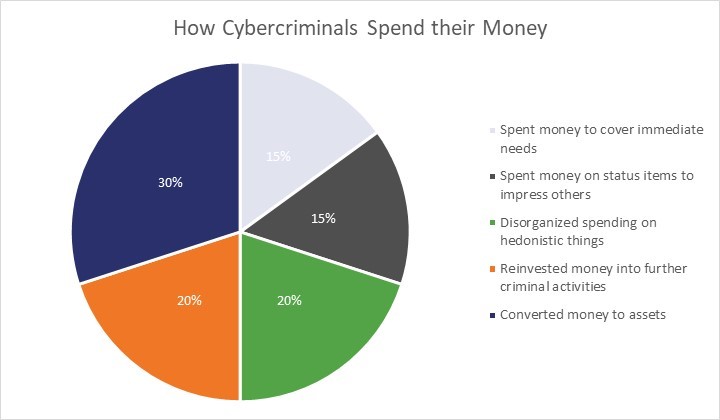
We’ve covered where cybercriminals store their money and the difficulty in laundering it, but what do they actually spend it on? Are any of these guys living lives of luxury about yachts in the Mediterranean? Some are, but many more are not. About 20% of the money went toward “disorganized or hedonistic spending.” An additional 15% went towards status items – purchases meant to impress girlfriends, other criminals, etc. I’m not sure what the difference between those two categories is, but they’re tabulated as separate expenses so let’s just roll with it.
Then there is the 15% of cybercrime revenue that goes towards covering immediate needs like food and diapers—spending that shines a light on the economic situations that facilitate cybercrime. Then we have the savers. 30% of cybercrime revenue gets converted into other assets like property. And then the last 20% are some real bad hombres, they’re the ones reinvesting their illicit gains into other areas of crime like terrorism or human trafficking.
Cybercrime and Cryptocurrency
One of the most common criticisms of almost any cryptocurrency is that criminals use it. This is somewhat correct, as we’ve discussed certain types of cybercrime almost lend themselves to cryptocurrency, but as with any blanket statement that gets a lot wrong, too.
The UK National Crime Agency and Interpol both agree that traditional cash still remains core to money laundering. Bitcoin is usually the first cryptocurrency that comes to mind, but given concerns over the ability to track transactions (thus undoing any anonymity) many criminals are beginning to use other currencies. And while 25% of Bitcoin transactions are sent through mixers to try to strengthen the anonymization, even those are beginning to be pulled down by regulatory pressure. Combine that with bans on cryptocurrencies in some jurisdictions like China and South Korea, and the volatility of the market, cryptocurrency still hasn’t proven itself as the future of money laundering.
Laundering through cryptocurrencies remains relatively small compared to the volumes of cash laundered through traditional methods. For example, a Europol estimate has suggested that money laundered via cryptocurrencies was only up to 4% of the total laundered in Europe at present (Silva 2018).
On the other hand, as we discussed earlier, ransomware works frequently with cryptocurrency, despite some of the issues that have been had with ransomware transactions being tracked in Bitcoin. In 2017, Alexander Vinnick was arrested in Greece. He was the proprietor of the cryptocurrency exchange BTC-e and is accused of laundering over $4 billion dollars in Bitcoin for cybercriminals. He denies this, obviously. But the fact remains an estimated 95% of ransomware profits up to that point had been cashed via BTC-e.
FACT: Researchers at Princeton suggest that, despite the use of tumblers and mixers, a unique linkage to individuals is still possible up to 60% of the time.
Final Thoughts
Obviously, this is a lot to unpack, but over the coming weeks and months we’ll be drilling down on each of these topics individually to explore the ways that cybercriminals are operating and the things that you can do as a business to stay secure.
The old idea that cybercrime is like a business needs to be replaced with a new metaphor that better captures its internal complexities; that is, that cybercrime now has its own economy – a literal “web of profit” that not only mirrors its legitimate counterpart, but that both feeds off it and feeds into it.
Re-hashed is a regular feature where we update an older post that we think some of our new readers would enjoy. This post originally ran on May 7.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown