Attacker Exploits FBI Website Vulnerability to Send a Hoax Email
When it comes to exploiting web and email vulnerabilities, no one — including the U.S. federal government — is impervious to cybercriminals’ attacks…
Earlier this month, the U.S. Federal Bureau of Investigation’s (FBI) legitimate IT infrastructure was fraudulently used to send hoax emails to tens of thousands of individuals and organizations. The phony email contained a message from the Department of Homeland Security (DHS), stating that the agency allegedly detected a sophisticated chain attack and identified a threat actor who was responsible for it.
While the FBI reports that no data is compromised, it still leaves us wanting answers to a few important questions: What the heck happened? How did this situation occur in the first place? And what can you learn from the FBI’s security incident that can help your organization avoid falling prey to similar attacks?
Let’s hash it out.
Breaking It All Down: An Overview of What Occurred
In a nutshell, on Nov. 12, an attacker capitalized on a basic vulnerability within the FBI’s IT infrastructure to send out phony emails to recipients that warned of fake cyber attacks. But what makes the situation particularly scary is that the messages were sent via an email address “eims@ic.fbi.gov” — this is a legitimate email domain that hails from servers controlled by the Bureau. This means that the attacker was able to use their IT infrastructure against them to send out emails from their legitimate domain.
The next day, the FBI released a brief official statement on the matter, saying that they were aware of the incident regarding the FBI email account and had taken the affected hardware offline. Of course, there’s a certain level of irony considering that in the same breath, they also warned people to “be cautious of unknown senders” and to report suspicious activity to either ic3.gov or cisa.gov. Since the emails were sent using an official email address by exploiting a webmail form vulnerability, that point is quasi moot in this case.
Two days after the initial faux emails went out, the FBI posted an update, stating that a threat actor gained temporary access to their law enforcement portal to send the hoax warning emails due to a “software misconfiguration.” (Brownie points if you remember this later.) The Law Enforcement Enterprise Portal, or LEEP, is part of the IT infrastructure that the Bureau uses to communicate with local and state law enforcement partner agencies. According to the Bureau:
“While the illegitimate email originated from an FBI operated server, that server was dedicated to pushing notifications for LEEP and was not part of the FBI’s corporate email service. No actor was able to access or compromise any data or PII on the FBI’s network. Once we learned of the incident, we quickly remediated the software vulnerability, warned partners to disregard the fake emails, and confirmed the integrity of our networks.”
The statement is a mix of bad and good news: Sure, the server in question was operated by the FBI. But it wasn’t used to house sensitive information. Rather, it was used to push messages to law enforcement partners.
The big takeaway in all of this is that the email messages were sent by a legitimate application on the FBI server. Since the FBI didn’t secure the API access, it allowed an unauthorized user to send out the hoax emails in their name.
What Did the Emails Say? Here’s a Look at the Hoax Messages
Okay, now that you have an idea of what this situation entails, it’s time to actually take a look at the message. The Spamhaus Project, an international threat intelligence organization, posted screenshots of one of these warning emails on its Twitter page:
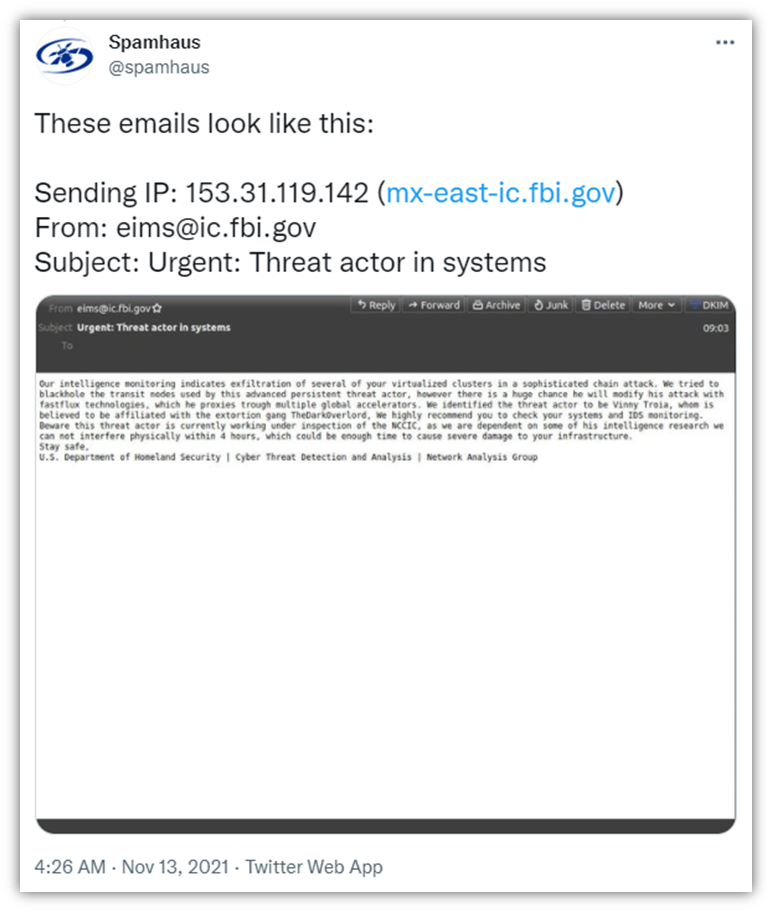
It says the following:
“Our intelligence monitoring indicates exfiltration of several of your virtualized clusters in a sophisticated chain attack. We tricked to blackhole the transit nodes used by this advanced persistent threat actor, however there is a huge chance he will modify his attack with fastflux technologies, which he proxies trough multiple global accelerators. We identified the threat actor to be Vinny Troia, whom is believed to be affiliated with the extortion gang TheDarkOverlord, We highly recommend you to check your systems and IDS monitoring.
Beware this threat actor is currently working under inspection of the NCCIC, as we are dependent on some of his intelligence research we can not interfere physically within 4 hours, which could be enough time to cause severe damage to your infrastructure.
Stay safe.
US Department of Homeland Security | Cyber Threat Detection and Analysis | Network Analysis Group”
… Uh huh. Okay. The spelling, grammar, and punctuation issues aside, this confused warning email seems to take an unusual left turn by ragging on cybersecurity researcher Vinny Troia. In an article in The Washington Post, Troia says he believes it was a smear campaign in response to research he’d published that exposed a young hacker and their involvement in several hacking groups.
The Spamhaus Project also tweeted another screenshot of the email’s sanitized header information as well for people to see:
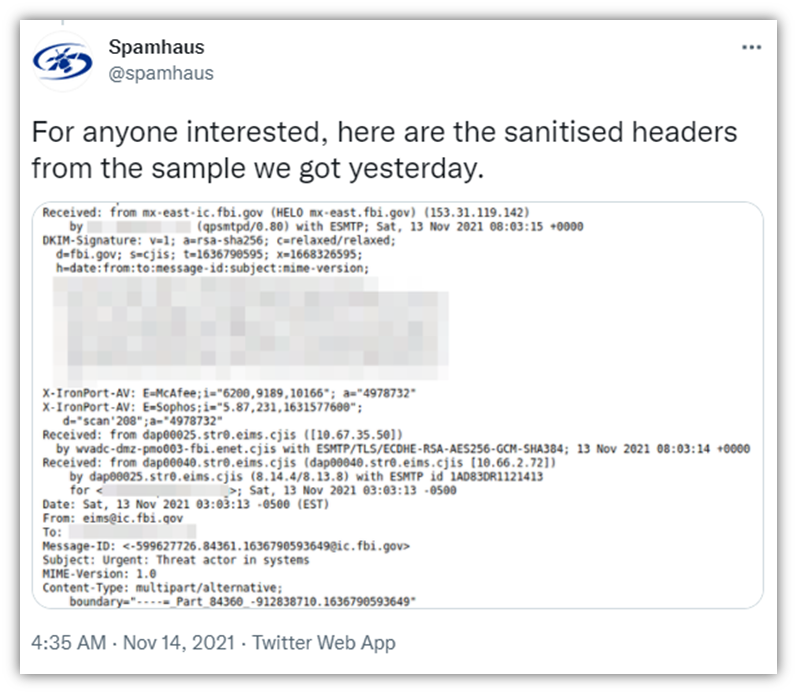
In the screenshot above, note the CJIS references in the “Received: from” fields — those stand for the Criminal Justice Information Services, which is a division of the FBI.
How the Form Mail Exploit Attack Occurred
In an article on his blog krebsonsecurity.com, Krebs said he interviewed the alleged attacker who goes by the username “pompompurin.” (Be sure to check out that article if you want a more in-depth look at how it occurred.) Pompompurin shared how he or she used the FBI’s own email system against them.
It all started with the LEEP web portal, which is intended to be used for government-authorized uses only by law enforcement and other related agencies.
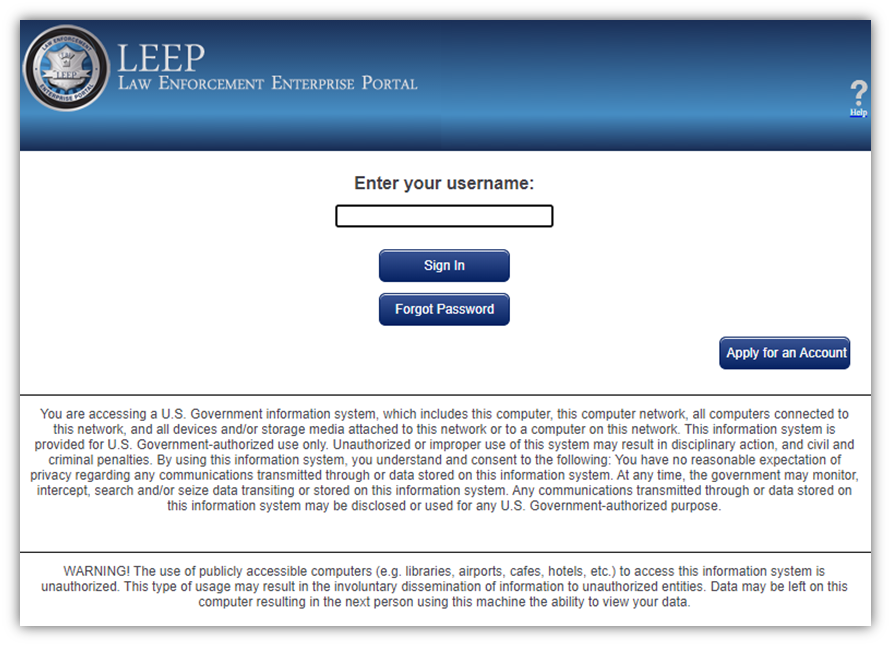
Until shortly after this incident, virtually anyone previously could set up an account on the law enforcement portal website. This process involved the FBI’s email system automatically sending a confirmation to a new user’s email account to confirm the new account.
Now when you hit the Apply for an Account button, it results in the following error message:
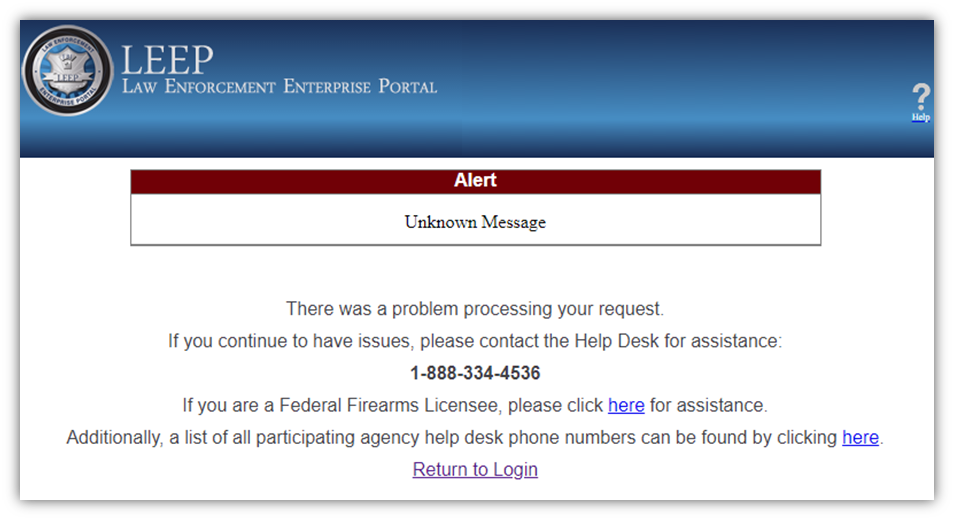
Oops.
Remember how the FBI’s statement pointed to a software misconfiguration as the cause of the security incident? Well, that not-so-little misconfiguration involved the system generating a client-side one-time code that it sent via an HTML POST request. (The POST request allows you to specify what information to include in an email and where to send it.) What this means is that the email gets generated in the browser where someone could — and apparently did — tamper with it and then the server would send the message.
- An attacker would receive confirmation code information that generated in their browser.
- They could change that information and put virtually whatever they wanted in the email’s key fields — subject line, body, and recipient info.
- They could use the FBI’s own webmail system to send the false message to whichever recipients they specified.
Using client-side code to send emails like this is really insecure and there’s no reason why any site should use it — especially not a federal government website! To say it’s insecure and dangerous is an understatement.
Why the Email Attack Occurred
There are plenty of reasons why the attack might have occurred — perhaps the attacker was just bored. Maybe they wanted to have a little fun at the expense of the FBI and Troia. Or, maybe, they’re a grey hat hacker who did something bad to do something that’s ultimately good…
According to Krebs, Pompompurin said the reason why they decided to hack the FBI’s email is that they wanted to call attention to a problem before someone else decided to exploit it for malicious reasons.
Why You Should Care
All of this goes to show that anyone — no matter whether you’re a small business, a large corporation, or even the federal government — can become the target or victim of a cybercriminal. Your technological weaknesses can be discovered and will be exploited if they fall into the wrong hands. Unfortunately for you and your business, if a bad guy finds one of those vulnerabilities to exploit, they may not have good intentions and will use it to cause significant harm to your business and customers.
Symantec reports that as of Q1 2020, one in every 4,200 emails were phishing messages. Now, imagine how much that number has likely skyrocketed considering all of the COVID-19-related scams, riots, and other ongoing world events that cybercriminals can use to their advantage.
At least, in this case, it doesn’t appear that the threat actor (Pompompurin) was trying to cause harm to the email recipients since they could have but didn’t. The emails weren’t sent out with any phishing links or attach malicious files. However, it’s no secret that email communications are a major target for cybercriminals. Email is the way that organizations stay in touch with their employees, customers, vendors, partners, and other key entities.
If someone can impersonate a legitimate organization or authority by hijacking their systems, who’s to say that they won’t use those systems to do significantly worse harm than sending an obviously fake email?
Final Takeaways: How to Make Email Communications More Secure
This particular cyber security situation for the FBI is one that was easily avoidable by following coding best practices and securing API access. But what other steps can you take to make your email communications more secure?
- Follow secure coding practices on your website, forms and web apps.
- Remove any client-side scripting capabilities that aren’t fully secure.
- Use email signing certificates to digitally sign all emails that are sent by your organization’s authorized users from their individual devices.
- Use BIMI and Verified Mark Certificates to add your logo to verified emails.
- Implement cyber awareness training for your employees that help them recognize phishing emails and other scams.


















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown