Official: Google Chrome’s Plan to Distrust Symantec SSL Certificates
The announcement being circulated simply finalizes an agreement from July
A couple days ago, on September 11, 2017, a group of Google employees made a post on the Google Security Blog outlining the final plan between Google and Symantec to distrust the latter’s root certificates.
This is not really news.
Despite the swell of media attention that the blog post has received, the post simply lays out an agreement that was formed back in July and updates it now that Symantec has sold its CA to DigiCert. In fact, it even says as much in the first sentence:
This post is a broader announcement of plans already finalized on the blink-dev mailing list.
Still, now that everything is final. It is worth hashing out what it all means.
But first, a quick disclaimer. Though Hashed Out operates with a considerable degree of autonomy from its corporate owner, The SSL Store™, we would be remiss not to admit that we have a long-standing partnership with Symantec (dating back to before the CA was Symantec at all).
While we support our partner, we do feel it’s worth pointing out that in this case Symantec is the victim of its own mistakes and Google was not acting unduly here. While a case can be made that the punishment is harsh, an example needed to be made and the entire CA ecosystem will be stronger for it moving forward.
What Happened with Google and Symantec?
Let’s start with one of the first misnomers about this story: that this is just between Google and Symantec. It’s not. Google, as the de facto leader of the browser community has taken the reigns on this issue, but the dispute is really between Symantec and the browsers.
At issue is a series of mis-issuances by Symantec over the past couple of years. This issue first appeared on the radar after Symantec effectively had its wrist slapped by Google back in 2015. A year later, the issue ramped up even more when security researchers discovered a batch of mis-issued test certificates.
At this point, Google and many others around the web ecosystem felt that the Symantec mis-issuances now constituted a pattern that was indicative of a much larger problem with Symantec’s validation procedures. After some investigation, it was discovered that several of Symantec’s regional partners – companies that handled validation in specific regions of the world – had not been in compliance with industry standards.
Now, the two parties couldn’t be farther apart in terms of how they present this entire situation. Symantec is quick to point out that the certificates in question were test certificates that were never meant to be used publicly—that this is a false flag. And Symantec is, at least on some level, correct in that no actual, real-world harm was done.
However, Google – and by extension Mozilla and many others involved in this debate – doesn’t care if the mis-issuances were test certificates or not. This is still serious. Regardless of the circumstances, Google and company view the mis-issuances as completely unacceptable and argue that this makes it harder to trust Symantec’s PKI.
Trusted Roots and PKI
When you’re discussing a trusted CA you are basically discussing two different entities. In terms of PKI and SSL encryption, what’s really important is the trusted root certificate. A trusted root is beyond valuable. It allows for the issuance of trusted digital certificates. Trusted roots already come pre-installed and trusted by web browsers. You can’t just create a trusted root from thin air. It takes a lot of work and once a company has one, it needs to be safeguarded.
When a company acquires a CA, what it’s really interested in is that root. Symantec acquired its root from Verisign. When we refer to the Symantec CA, what we’re really referring to are the original Verisign roots being run by the company Symantec. And that’s the other entity that comes into play when we discuss CAs. You have the trusted root, and then you have the organization that’s managing it.
So how does that factor into the Google/Symantec conversation? Google views Symantec’s mis-issuance issues as undermining its entire PKI. Or in layman’s terms, all of its roots are no longer trustworthy in Google’s eyes. And that’s where Google’s negotiation with Symantec began.
When you strip away all the extra pieces, the conversation really came down to this: Google didn’t feel it could, in good conscience, continue to trust Symantec’s PKI unless changes were made. The entire negotiation consisted of both sides working to reach an agreement wherein Symantec could make the necessary changes to its PKI (its roots) while making sure its customers’ certificates would continue to be trusted.
That agreement was finalized at the end of July.
What Is the Google/Symantec Agreement?
Google has agreed to continue recognizing and trusting Symantec SSL certificate provided that Symantec takes requisite steps to address issues with its PKI. This will be done by shifting Symantec’s issuance needs to a managed third-party Certificate Authority while it rebuilds its own PKI infrastructure.
Here’s how that’s going to play out:
- Symantec’s old Verisign roots will officially be distrusted in Chrome 66 (April 17, 2018). RIP.
- Symantec has sold its CA business to DigiCert, which will now issue for Symantec.
- DigiCert will begin issuing for Symantec in December 2017, affected Symantec SSL Certificates will need to be replaced at some point in 2018.
So, briefly, in layman’s terms: Symantec has agreed to transfer its CA operations to DigiCert for nearly 1-billion dollars and a 30% share in the company. DigiCert will now begin to issue digital certificates on Symantec’s behalf using its own trusted roots. This will allow Google to continue trusting Symantec certificates while Symantec addresses its PKI issues.
In the meantime, this is a sad end for VeriSign’s roots, which are effectively dead as of the end of the year.
What is the Timetable for the Distrust?
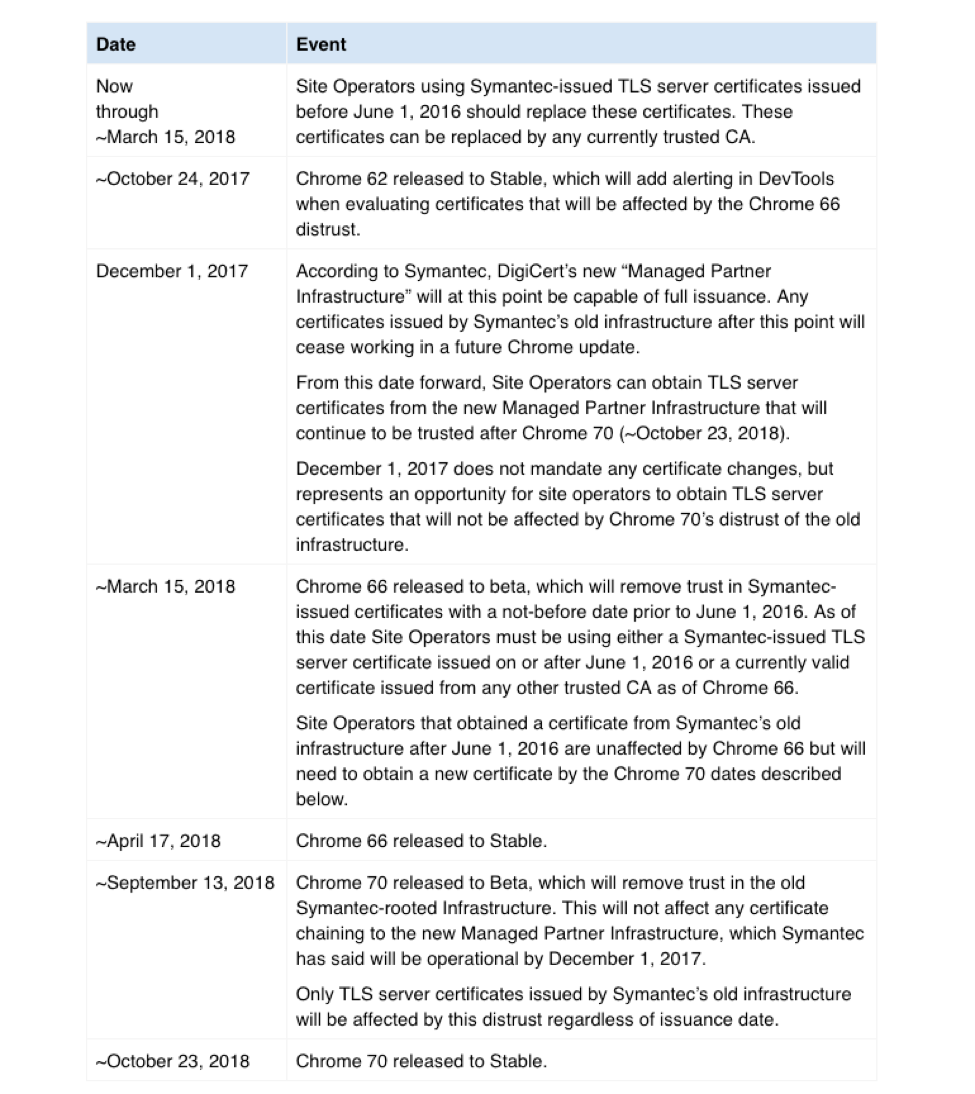
Per Google’s Security blog, here is the final timeline for the Google Chrome’s distrust of the Symantec roots:
What We Hashed Out (For Skimmers)
Here’s what we covered in today’s discussion:
- Google’s plan to distrust Symantec’s roots is not new, the plan has just been updated to reflect DigiCert’s acquisition of Symantec’s CA.
- DigiCert will begin issuing digital certificates on Symantec’s behalf in December of 2017.
- Current Symantec customers will not need to take action until April 2018, when they will need to replace their Symantec certificate with a new one (free).






































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)












5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown