How to Prevent Cybercrime: 9 Helpful Tips
We’ll walk you through how to cyber police your data for cybercrime prevention and control
Many cyber security articles on cybercrime often start with a shocking statistic about how cyber attacks are on the rise. Danger! Beware!
But we’re not going to do that here. Instead, we’re going to present you with parodied lyrics to a song. The evolving modern cybercrime landscape is suitable for a parody of an 80s song by The Police:
Every account you create
Every transaction you make
Every security best practice you fake
Every email you communicate
Hackers are watching you.
It is true that cybercrime is increasing in occurrence each day and evolving to become more complex. But what is cybercrime? What constitutes such a significant (and growing) industry? In the broadest sense, cybercrime is any type of illegal activity involving the internet. Some of the most common types of cybercrime include identity theft and information misuse, data and intellectual property theft, human trafficking, child pornography, and terrorism. As you might guess from our variation of song lyrics, many of these crimes are committed using a variety of cyber security attack tactics such as phishing, CEO fraud, man-in-the-middle (MitM), hacking, SQL injections, DDoS, and malware attacks. Historically, these crimes were committed by lone wolves. Nowadays, however, cybercrime is a booming industry comprised of criminal enterprises, organized hacker syndicates, hacktivists, and nation-state actors.
The gargantuan task of knowing how to prevent cybercrime often comes down to nullifying cyber security threats and figuring out how to prevent cyber attacks. However, hackers’ continuously-changing tactics, a growing number of actors, and rapidly expanding technologies make it challenging for cyber security experts and businesses alike to stay a minimum of one step ahead of cybercriminals. Furthermore, there is no one singular method of 100% cyber crime prevention — understanding how to prevent cybercrime is about bringing together an effective combination of technologies, best practices, and procedures to craft the solution that is best for your business.
What are some of the best methods cybercrime prevention and control from a business perspective? Let’s hash it out.
How to prevent cybercrime — step #1: Follow industry best practices and guidelines
Cyber crime prevention is not a one-size-fits-all approach. Organizations of different sizes have different needs, threats, risk tolerances, vulnerabilities, and capabilities. Luckily, governments, regulators, and even industry organizations have provided some general frameworks and security recommended practices for organizations to follow to reduce their likelihood of falling victim to cyber security attacks. However, it is important to note that some are more particular than others in their recommendations or requirements. For example:
- GDPR, which stands for General Data Protection Regulation, is comprehensive legislation that rolled out in 2018 to protect the data and privacy of European Union citizens (even those living abroad and international companies that handle data of EU citizens). The regulation outlines much of what is or is not allowed, states what falls under data subjects’ (the citizens’) expectations of privacy, and details some of the stiff penalties that businesses and organizations alike could face for noncompliance.

- NIST, also known as the U.S. Commerce Department’s National Institute of Standards and Technology, is the go-to resource for cyber security professionals. Last year, NIST released version 1.1 of its popular Cybersecurity Framework document, which outlines ways to improve cyber security for critical infrastructure. The goal of the document is to provide “a prioritized, flexible, repeatable, performance-based, and cost-effective approach, including information security measures and controls that may be voluntarily adopted by owners and operators of critical infrastructure to help them identify, assess, and manage cyber risks.” Ideally, the framework should be used to complement your organization’s existing cyber security program and risk management processes, not replace them, and outlines five concurrent and continuous “functions”— Identify, Protect, Detect, Respond, and Recover — to address cyber security risks.
- HIPAA, the national Health Insurance Portability and Accountability Act in the United States, is not as particular nor stringent as the GDPR about how patient data and confidential personal health records are to be used, stored, or transferred. HIPAA’s Security Rule does not technically require encryption of patient health information (PHI). Instead, § 164.312’s standard for transmission security says that organizations must “Implement technical security measures to guard against unauthorized access to electronic protected health information that is being transmitted over an electronic communications network.” Even the rule’s technical safeguards concerning the topic of encryption are defined only as “addressable” requirements — handlers of PHI must “Implement a mechanism to encrypt electronic protected health information whenever deemed appropriate.” Isn’t that comforting? Granted, the language is left purposefully vague to account for evolution and changes in technologies. However, it also leaves businesses with potential opportunities to argue away their way out of responsibility and accountability.
- PCI SSC, the Payment Card Industry Security Standards Council, requires businesses that use account data to implement certain protections for that information. These data security requirements, known as the PCI Security Standards, require encrypted transmission of cardholder data across public and open networks, use of strong access control measures, implementation of a vulnerability management program, and more. Failure to comply with these standards can result in significant fines and penalties — not to mention possible suspension of your company’s card payment processing capabilities.
Sounds simple enough, right? These are highly-regarded resources for IT security professionals and businesses alike. The trouble is, though, not all businesses adhere to these recommendations (or, in some cases, required practices). An apropos analogy is when an adult tells a small child not to touch a hot stove because they will get hurt, yet the kids does it anyway: Some children (or businesses, in this case) choose to learn the hard way and wind up getting burned. For companies who instead choose to “listen to the adult” and adopt these required or recommended methods of cyber crime prevention, they will be in a better position to protect their data, employees, and customers from cyber security attacks and data breaches.
These other methods of cyber crime prevention can (and should) include the following:
How to prevent cybercrime — step #2: Implement digital & physical security methods
We have previously discussed the idea of using firewalls, antivirus, network and server monitoring, and other forms of physical and digital data center security measures to create barriers for cybercriminals. Aside from hacktivists and nation-state actors who are trying to achieve ideal or political goals, many modern cybercriminals are simply looking for a way to make money. This could be through wire transfer scams or by stealing account information, personal data, or even intellectual property and proprietary research.

However, the more challenging your defenses are to get through and the more responsive you are to their attacks, the more work a hacker will have to do to accomplish their goals. This makes your business less appealing as a target. After all, why would a thief want to go to the trouble and planning to rob a castle when they can just attack the king’s carriage instead? This same approach can be said for hackers when they are choosing a target for a cyber security attack. In part, cyber crime prevention includes hardening your defenses as much as possible so that your company appears to be more trouble and effort than the potential payoff is worth.
How to prevent cybercrime — step #3: Maintain asset lists, patches, and updates
While this should go without saying, cyber crime prevention involves keeping your company’s hardware, software, and digital assets up to date through proper IT security asset management. A very easy and common way for hackers to get through a company’s defenses is to simply take advantage of security gaps that exist due to outdated or unpatched IT infrastructure and software. While zero-day vulnerabilities — such as a Windows 10 cyber vulnerability for Microsoft Edge web browser users — could enable threat actors to take advantage of weaknesses that are unknown to manufacturers, the vulnerabilities they do know about are ones that companies will often issue updates or patches to fix.

An equally important responsibility is ensuring you maintain an up-to-date inventory list of all hardware, software, data, and security certificates so you know exactly what is on your networks, servers, and other IT systems. Keeping an up-to-date list not only helps you stay informed about your assets, but it also helps you keep vital information at your fingertips so you aren’t scrambling for information at the last minute should a cyber security event take place. This will play a vital role in implementing any incident response plans (IRPs), IT disaster recovery plans (DRPs) and business continuity plans (BCPs).
How to prevent cybercrime — step #4: Manage SSL/TLS certs and keys for your domain(s)
When discussing how to prevent cybercrime, we’d be remiss to not mention the importance of using a secure protocol for your website in lieu of a nonsecure one. HTTPS, the secure version of hypertext transfer protocols for websites, is essential for every website regardless of content — even Google says so. This secure protocol is made possible through the use of SSL/TLS certificates — secure sockets layer and transport layer security — which authenticates websites and businesses and enables secure, encrypted communication through a process known as a TLS handshake.
In a nutshell, SSL/TLS certificates have three purposes:
- To authenticate your website or business,
- To ensure data integrity, and
- To create a secure, encrypted connection for content and data to transmit back-and-forth between a user’s web browser and your web server(s).
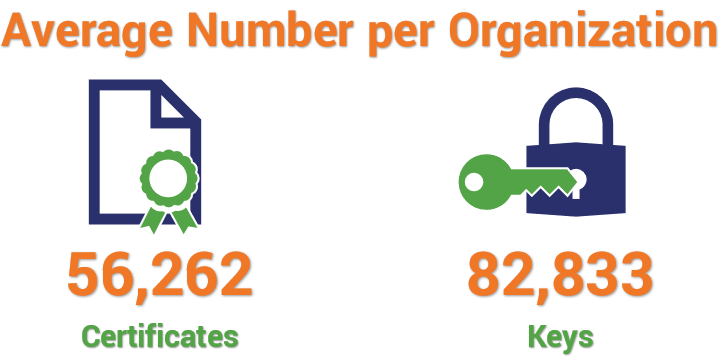
Once SSL/TLS digital security certificates are installed, the certificates and encryption keys must be managed to ensure that they remain up-to-date and don’t expire. While this may sound like a simple task, consider that the average number of certificates and keys per organization range in the tens of thousands, according to a survey of nearly 600 IT and IT security professionals by KeyFactor and the Ponemon Institute:
That’s a lot to track continuously. This is one of many reasons why public key infrastructure (PKI) and certificate management are such important task for every business, regardless of whether they hire a specialist to manage their PKI or use in-house personnel. This practice helps to avoid the issues and costs that can result from poor management, such as those reported in the KeyFactor/Ponemon Institute report:
| Scenario | Extrapolated Cost |
| Cost of unplanned outages due to certificate expiry | $11,122,100 |
| Cost of failed audits/compliance due to undocumented or poor key management | $14,411,500 |
| Cost of server certificate and key misuse | $13,423,250 |
| Cost of Code Signing certificate and key misuse | $15,025,150 |
| Cost of CA compromise or rogue CA for MITM and/or phishing attacks | $13,219,850 |
| Total Cost | $67,201,850 |
HTTPS is considered the leading protocol and now represents 50.6% of site elements as of April 25, 2019, according to W3Techs. Although we’d like for this number to be higher, it’s important to consider that this statistic is up from the previous year’s standing (30.8%) as of April 1, 2018. The HTTP/2 protocol, which can’t be used without encryption, also represents 36.3% of site elements, up from 24.6% in the previously mentioned timeframes. Google even recommends HTTPS websites supporting HTTP Strict Transport Security (HSTS), which tells users’ browsers to request HTTPS pages automatically (regardless of whether they type HTTP into their omnibox) to minimize the risk of delivering unsecured content.
How to prevent cybercrime — step #5: Train employees to identify and react to threats
Do you know what the biggest vulnerability in cyber security is for most businesses? If you guessed “employees” or “employee negligence,” then you are correct. Employees (in house and remote) represent the most significant security risk to businesses and employee negligence is the leading cause of data breaches, according to research from Shred It. While I may not have a prize to offer, I can at least share some relevant insight on how to protect yourself from the numerous cyber threats that exist and seek to exploit your cyber vulnerabilities.

Cyber awareness training provides a basic understanding of cyber security best practices. Great training teaches employees — everyone from C-level executives to the janitorial staff — how to:
- Identify and respond to phishing and other email scams (hint: don’t engage with them).
- Practice safe internet habits (such as creating secure passwords and not using them across multiple accounts).
- Familiarize themselves with your organization’s cyber security-related policies and abide by them.
- Recognize social networking threats.
- Safely collect, store, manage, and send client and company data.
- Comply with government and industry regulations.
Your employees are your company’s first line of defense. While automated cyber security protections such as firewalls, antivirus and antimalware solutions can help, they don’t block every threat. This means that your employees need to be able to recognize and act quickly (and safely) to threats that make it through your network and other systems’ defenses. They also need to know how to not create risks by handling sensitive data and information appropriately.
Effective cyber security training for cyber crime prevention is educational for both your employees and your IT security staff. Though we already know the way that it is educational for the former, the way that it is also educational for the latter is that it should involve regular testing as well. This training helps info sec professionals assess what is or is not working from the training so they can identify areas they need to drill down on more in-depth to increase employee understanding. One example of such testing, phishing simulations, will be discussed in the next section.
How to prevent cybercrime — step #6: Implement email security solutions and phishing simulations
Considering the rise in business email compromise, phishing, and other email-related concerns, the modern virtual mailbox represents a significant area of cyber security vulnerability. Unlike physical messages sent by a physical mail carrier, emails can contain a variety of threats from attachments containing malware (often Microsoft Office files such as Excel spreadsheets and Word documents) to embedded links that direct users to malicious websites.
Many businesses tend to rely on the anti-spam filters that come with bundled with their email platform or antivirus programs to protect their business’s communications. However, there are additional third-party email solutions that you can use such as anti phishing platforms and email signing certificates.
Anti phishing platforms can automatically identify and even quarantine potentially dangerous emails so users can’t engage with them. Some anti phishing solutions even provide an educational component to help users understand why emails are being quarantined (such as a sender’s name not matching their email address or signature, embedded links directing users to dangerous websites, etc.). Email signing certificates allow users to digitally sign and encrypt emails containing sensitive or confidential information to avoid man-in-the-middle (MitM) attacks and eavesdropping. By signing your emails, it allows your recipients to authenticate that you are you and mitigates email tampering.

While putting these protections in place is exceedingly important, you still need to take it a step further and conduct periodic phishing simulations. This will allow you to test the cyber security awareness of your employees to assess how well they can apply the lessons from your training in real-life scenarios. Seeing whether employees are approaching email more judiciously or are opening every messages with wild abandon will help you recognize which employees are your biggest risks as well as identify new areas to address with cyber security and phishing awareness training.
How to prevent cybercrime — step #7: Monitor traffic and access to increase visibility
If you want to keep an eye out for danger, it’s best to keep the lights on, pay attention to everyone coming and going, and make regular patrols. What many businesses do instead is turn off the lights, turn on the TV, and ignore everything else. By always keeping their attention focused on something else and not paying attention to the traffic and things going on around them, they will miss important cues and won’t be able to observe or learn from situations that occur.

In a nutshell, this concept summarized the importance of IT threat monitoring. This function involves continuous monitoring of the traffic, access, and denial logs on your network and other IT infrastructure components such as servers and workstations. It can involve the use of security information and event management (SIEM) tools and intrusion detection/intrusion prevention systems (IDS/IPS) but also can include the services of a cyber security operations center (CSOC). A CSOC team can provide 24/7/365 monitoring of systems and logs to ensure that threats are identified and addressed to mitigate damage. This can be particularly helpful in monitoring traffic to identify distributed denial of service (DDoS) attacks, which can result in a slow network, iffy connectivity, or even website downtime.
How to prevent cybercrime — step #8: Regularly assess and test your systems
Vulnerability assessments, risk assessments, and penetration tests are simultaneously the best friends and annoying acquaintances of IT security experts everywhere. Although these terms are often incorrectly used interchangeably, these three methods of IT security they are related but separate functions:
- A vulnerability assessment helps to identify, assess, and prioritize any vulnerability in cyber security that may exist in your existing system.
- A risk assessment, on the other hand, is useful for evaluating potential risks for specific tasks or events (if you did “A,” then X could happen as a result).
- Lastly, penetration tests are your IT security team’s way of testing to see how your defenses can be breached or compromised.
The goal with these tools is to help you understand the strengths and weaknesses of your cyber security posture. This knowledge is just as valuable as knowing the strengths and weaknesses of your enemy — in this case, hackers or insider threats. This approach supports the ancient wisdom of Chinese military strategist Sun Tzu in (a translation of) his military treatise “The Art of War”:

“If you know the enemy and know yourself, you need not fear the result of a hundred battles. If you know yourself but not the enemy, for every victory gained you will also suffer a defeat. If you know neither the enemy nor yourself, you will succumb in every battle.”
These tools are invaluable in terms of identifying network vulnerabilities, out-of-date software that need patching or updates, gaps in your existing cyber security defenses, and other cyber security vulnerability concerns.
How to prevent cybercrime — step #9: Develop, implement, and enforce security policies
While analyzing, poking, and prodding your network and other IT systems is great, you still need to take it a step further and implement other protective measures in the form of cyber security policies. In the world of IT security, there are many types of security-related policies to choose from such as computer use policies, password policies, remote access policies, email/communication policies — the list goes on and on. Each of these policies has its own benefits and merits that should be considered.

Access management and an access control policy are also extremely important. Regularly review who has access to what systems, information, or data to ensure that you’re not leaving your business open to attack or insider threats. Limit employee access through a policy of least privilege (POLP) to ensure that each employee only has access to the tools and information their job necessitates. This will help to limit your potential risk by reducing the number of people who have access to your most valuable data. NIST offers a valuable resource that links to several of their access control policy and implementation guides that you can review for additional information.
Just remember, however, that a policy is only as good as its enforcement. If you put policies into effect but never follow up or enforce them, then they are essentially useless documents that serve no purpose. Be sure to enforce each of your security policies to ensure that your business is getting the most protection possible.
Final thoughts
Because many (though not all) cybercrimes involve cyber security attacks and exploiting known and zero-day vulnerabilities, implementing this combination of tactics, policies, and processes will help to significantly strengthen your cyber security posture — and your level of cyber resilience along with it.
Hopefully, it also means that the song lyrics we shared with you at the beginning of this article will change and be aimed at prospective hackers and threat actors:

Every malware you make
Every piece of data you take
Every email you fake
Every website you scrape
I won’t fall for you…
(Or your cyber attack tactics).
What additional recommendations or best practices do you have on the topic of how to prevent cybercrime?



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown