Smile! Thanks to Verkada Breach, You Could Be on Candid Camera
Verkada Hack Leaves Hundreds of Thousands of Cameras Exposed – Here’s How the Attack Could Have Been Avoided With PKI + Access Control Best Practices
Ever get the feeling that someone is watching you? It’s not a nice thing, and you’re even more likely to experience it if there are security cameras in your vicinity. They are becoming more and more common these days, both in our workplaces and homes, and roughly five billion cameras are expected to be in use by 2027 according to Reportlinker.com. That’s nearly one camera for every person on earth.
Modern video camera systems have exploded in popularity thanks to their cheap price and ease of use, but with this convenience factor comes potential security risks that can leave us unsuspectingly exposed. Enter Verkada, a Silicon Valley company that offers cloud-based security cameras. Similar to the recent SolarWinds hack, everything was fine until hackers were able to breach Verkada’s systems. Hundreds of thousands of cameras were compromised, as was the company’s video storage library. Suddenly factory workers, medical personnel, and even children playing at home were all exposed, violating their privacy and potentially allowing attackers to access other systems on the camera’s network.
So, how were the hackers able to pull off the Verkada breach? How did the company respond? And how can organizations prevent similar breaches in the future?
Let’s hash it out.
Who is Verkada?
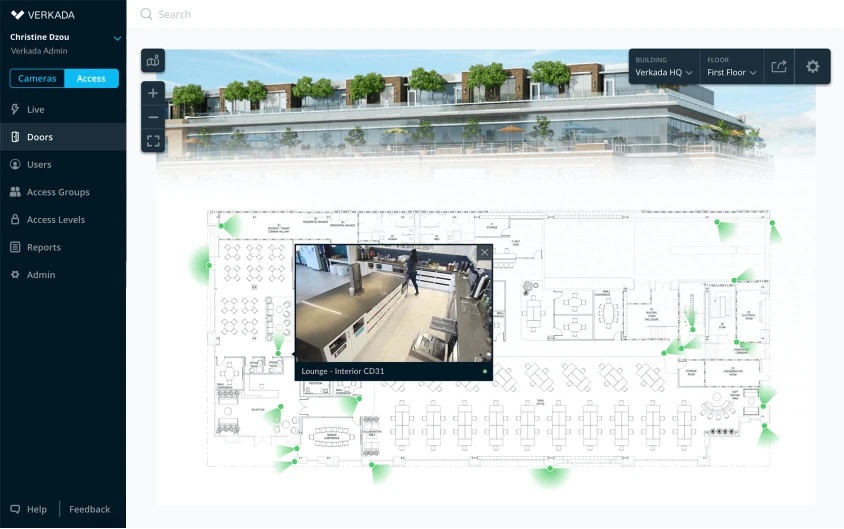
First, let’s take a look at the company itself. Verkada was founded in 2016 and sells cameras to a wide variety of industries and markets. Everything from offices to jails to schools to gyms to police stations. Notable clients of theirs include Cloudflare, Tesla, Equinox, and Nissan. Verkada offers the equipment required to monitor any desired areas, plus building automation gear that keeps track of temperature, motion, noise, and door access.
Their hardware requires an internet connection so it can access their cloud service. This gives customers the ability to watch and store real-time video from any location. Verkada also boasts artificial intelligence features that can track individuals as they move around. Called “People Analytics,” this software searches for specific people based on their face, clothes, any accessories they’re carrying, and their gender, and allows them to be tracked as they move around.
The selling point of their AI features is that it improves public safety and security by detecting unusual occurrences that possibly pose a danger. Basically, the goal is to stop crimes before they occur. Yes, we’re getting into Minority Report territory here. These kind of “video analytics” systems are becoming more and more popular as a greater number of companies and public organizations turn to them in an attempt to prevent everything from petty theft to mass shootings.
What Happened in the Verkada Breach?
About 150,000 of the company’s cameras were accessed by a Swiss “hactivist” group known as Persistent Threat 69420 (quite the serious name, indeed). The collective has less than ten members, including Tillie Kottman, who describes their mission:
We generally do not do targeted work. We all have ADHD and not a lot of patience. We do scans for very broad vectors looking for vulnerabilities.
The goal of this particular attack was relatively straightforward – to demonstrate how easily Verkada’s cameras could be hacked and to raise awareness of their vulnerabilities. Access was gained when the group located credentials for a “super admin” account on a public-facing server. Specifically, it was on an unencrypted subdomain intended to be used as an internal development system. As Kottman explains:
This one was easy. We simply used their web app the way any user would, except we had the ability to switch to any user account we desired. We did not access any server. We simply logged into their web UI with a highly privileged user account.
After finding the credentials, they were able to move freely within Verkada’s internal network and had root access to individual cameras. This allowed them to use the cameras to execute whatever code they wanted, giving them the ability to potentially perform further, escalated attacks. The hackers were also able to subsequently infiltrate some customer networks by using the camera’s connection as a starting point.
Besides accessing the live feeds of individual cameras, the hacker group was also able to infiltrate the complete video archive that contains files saved by Verkada’s users to the cloud. The centralized nature of the company’s software enabled the attackers to browse a massive amount of data with just a few clicks.
Who Were the Victims of the Verkada Breach?
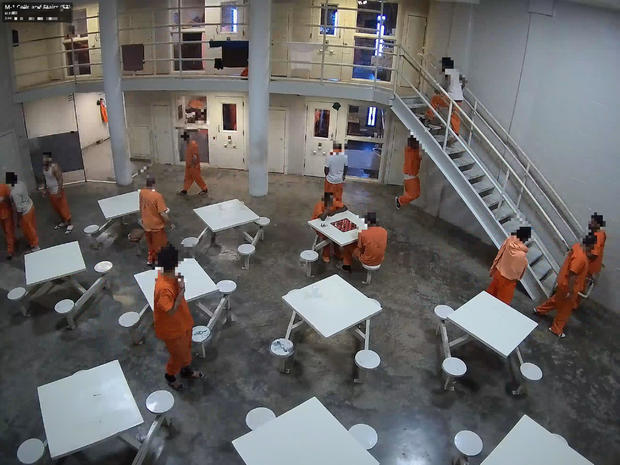
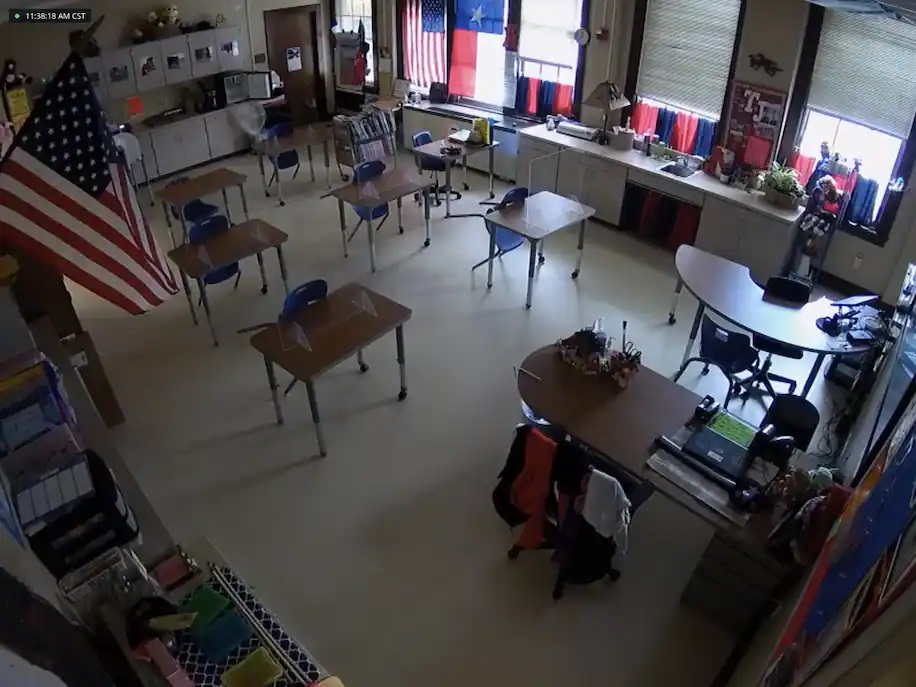
Anyone who used Verkada cameras was at risk, and the list of those affected is both long and diverse. The attackers were able to take a live glimpse into the factories of Tesla and Nissan, county jails around the country, and the offices of companies like Cloudflare and Equinox. Organizations weren’t the only target – average people like you and I were impacted as well. The hackers did not discriminate.
Some of the released videos are quite eerie to watch because of how “real” they are and the fact that the subjects of the videos have no idea they’re being spied on. One video shows a father and his children working a puzzle in a playroom, and another shows a nurse checking on someone in a hospital bed. There’s videos of empty corridors and conference rooms, and even ones of convicts milling around a jail.

The hackers didn’t stop there once they had access to Verkada’s network. They stole the company’s entire client list, containing over 24,000 entries along with potentially sensitive information on each.
How Did Verkada Respond?
The company acknowledged the hack and issued an apology for the exposure of “video and image data from a limited number of cameras.” However, they are not getting rid of the ability to view the live stream of individual devices.
Moving forward, Verkada says they intend to come up with a more effective approach to managing login data, hire more security experts, and use third-party consultants to perform a security audit. CEO Filip Kaliszan said:
While we already have robust logging and audit capabilities, we will ensure that customers receive proactive notifications whenever their data is accessed by Verkada, including by our technical staff
The company has also disabled their internal administrator accounts and notified law enforcement so they can pursue the perpetrators.

Verkada has been in the news a few times previously in the past few years, and not for good reasons. Their security measures have been publicly questioned by security analysts, with Charles Rollet, part of the security research group IPVM, saying
Verkada had sold their system as particularly advanced in terms of privacy and security, which is ironic when you look at what happened. People don’t realize what happens on the back-end, and they assume that there are always these super-formal processes when it comes to accessing footage, and that the company will always need to give explicit consent. But clearly that’s not always the case.
Three employees were also terminated last year for using company cameras to spy on fellow employees, as well as making sexually explicit jokes about them. They aren’t the only security company to face this kind of issue, as the doorbell company Ring has also recently fired employees for similar infractions.
Verkada could face even more legal trouble down the line, as the Department of Health and Human Services (HHS) may investigate them for possible HIPAA/HITECH violations. Security camera footage from medical facilities can sometimes be considered as sensitive health information. There are also possible GDPR violations and the potential for class-action lawsuits, so time will tell what additional penalties Verkada may be hit with.
How Could the Verkada Breach Have Been Prevented?
The Verkada breach raises numerous questions concerning device security. First off, why did this “super admin” account exist in the first place? Verkada said that admin access was given to engineers and support staff so that technical issues could be fixed, but surely there are better approaches that would still allow for effective problem solving and troubleshooting. Admin access should only be given out on a user-by-user basis, and only to those that absolutely require it to carry out their duties. Jeff Costlow, CISO at cloud security firm ExtraHop, agrees:
I’m OK with vendors having the ability to auto-update the device. That means they have control over the source code. But that doesn’t mean that they have control over the device any time they want.
Companies, and in particular start-ups like Verkada, must implement best practices for privileged access to systems in order to prevent privacy breaches like these. While manufactures do indeed have legitimate reasons to log into your devices, comprehensive controls, restrictions, and auditing should be enacted to maintain the right balance between safety and access.
There was clearly a lack of effective access control in place, and even if these kind of “super” accounts exist, the credentials should never be stored anywhere that could potentially be public-facing. This is a textbook example of how certificate-based authentication can prevent unauthorized access. Copying and pasting a username and password into an email or webpage is an easier and more likely scenario than someone taking an archive of the certificate/key and posting the contents. Plus, you can link certificates to individual users so you’ll have a trail of who is accessing what, and when they’re doing it.
Vendors could even go a step further and have each customer act as its own “mini” private certificate authority. That way, no one can access the device unless the owner issues a certificate to them. In the case of Verkada, if a customer had a technical issue then they could issue a certificate to the support team so they could fix it. Otherwise, the doors to the device would always be locked.
End-users should also have more control over how vendors are able to interact with their devices. While users can create admin accounts on their own Verkada cameras, for example, they couldn’t do anything to prevent the company’s “super admin” account from accessing their video feed. Ideally, users would have to opt-in to allowing a feature like that, in order to preserve privacy by default. Users should have full control of the devices they own – period.
This incident also serves as a reminder that upon purchasing any new device, one should always go through the default settings. You never know what is enabled/disabled by default, and what possible vulnerabilities may be created as a result. No matter what, the default login credentials should always be changed.
There’s some irony in the Verkada breach – it demonstrates the dangers of self-surveillance. We have such a strong desire for a sense of security, but if it’s not properly implemented then it can end up creating even more security threats as a result. In this particular case, we aren’t even talking about a sophisticated attack or previously unknown vulnerabilities – the bad guys simply used valid credentials. It’s critical that companies be proactive with access controls and security in general so that they won’t have to learn things the hard way, which ends up punishing average consumers like you and I, as well.
Protect Your Site With CodeGuard Backup

It’s like an undo button to reverse damage done by a mistake, cyber attack, a bad update, or other issues.





































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)













5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown