Growing Demand for Custom PKI Solutions Creates New Opportunities for IT Providers
Public key infrastructure (PKI) adoption is booming. New data from MarketsandMarkets forecasts that the global PKI market (which includes SSL/TLS certificates) will reach $9.8 billion by 2026 — let’s explore how you can get your piece of the pie as an IT provider
With the growing demand for data encryption, digital identity management, and more secure authentication, the need for custom/private PKI solutions has exploded. PKI, in one form or another, is a compliance requirement of many data security and privacy regulations. Consumers, businesses, and governments want greater security, and the use of public key infrastructure tools is one way to achieve that.
This new demand has created a unique opportunity for IT providers of all types — managed service providers, consultants, data centers, software developers, and more. Why? Because there are growing needs for public key infrastructure solutions across virtually every industry.
What are the growth trends driving this growth, and how can you, as an IT provider, help your customers?
Let’s hash it out.
PKI & Digital Certificate Usage Is Growing — Thanks to Several Industry Trends
The number of SSL certificates on the internet has exploded over the past decade. Just a few years ago in 2015, BuiltWith reports that fewer than 3% of websites used HTTPS by default, but now in 2021, 75% of all websites use HTTPS. That equates to hundreds of millions of additional certificates… and SSL certificates are just a small piece of the PKI pie.
Keyfactor reports that the average organization now has 88,750 digital certificates and keys in use. These certificates are used for securing everything from applications and websites to authentication processes and IT environments. In general, PKI certificates have three main uses:
- Encryption. Encrypting data for websites, databases, emails to keep communications private.
- Identity/Authentication. Asserting digital identity to authenticate users, devices, and/or organizations.
- Integrity. Ensuring data integrity of documents and software so users know they haven’t been altered.
The Trends Driving PKI Growth
Because PKI certificates are used for so many different things, there’s not just one trend driving the adoption of PKI—it’s multiple trends. Here are a few notable trends that are driving companies to adopt PKI:
- Zero trust security model,
- Increased HTTPS adoption,
- Passwordless authentication,
- VPN access to support remote working,
- Privacy legislation mandating encryption (e.g., GDPR), and
- Explosion of IoT devices.
Digging into each one of these trends is beyond the scope of this blog post, but let’s take a brief look at two of them…
PKI > Passwords
When it comes to securing your organization against unauthorized access, traditional passwords are no longer enough. All you have to do is look at the most recent cyber attack headlines involving phishing and credential theft to see proof.
Cybersecurity expert Brian Krebs equates passwords as “the fossil fuels powering most IT modernization”:
“They’re ubiquitous because they are cheap and easy to use, but that means they also come with significant trade-offs — such as polluting the Internet with weaponized data when they’re leaked or stolen en masse.”
Sure, one option is to require your employees to use unique passphrases instead of traditional passwords. These are long phrases that consist of multiple random, unrelated words like RubberWallpaperGumball. But if even just one user breaks the rules by re-using their password on another site that gets breached, all bets are off. Without additional security measures in place, you won’t know whether it’s truly your employee who’s logging in or an imposter.
PKI certificates (and their associated private keys) can’t be stolen via phishing attacks or database breaches. This makes PKI a more secure method for logging in to VPNs and other internal systems that contain sensitive data or controls.
PKI and Zero-Trust Go Together
Using PKI-based authentication helps strengthen your organization’s data and IT security capabilities by preventing unauthorized access. This concept is at the heart of zero-trust security. Zero trust is centered around the idea that users must have:
- Approved authorization (permissions or privileges) to access something,
- Ability to authenticate (i.e., prove they’re the legitimate user) prior to gaining access to a secure resource, and
- Must continually prove their identity to maintain that access.
Unlike passwords, PKI-based authentication credentials cannot be spoofed or stolen via methods such as phishing. This makes PKI the ideal foundation for implementing a zero-trust model.
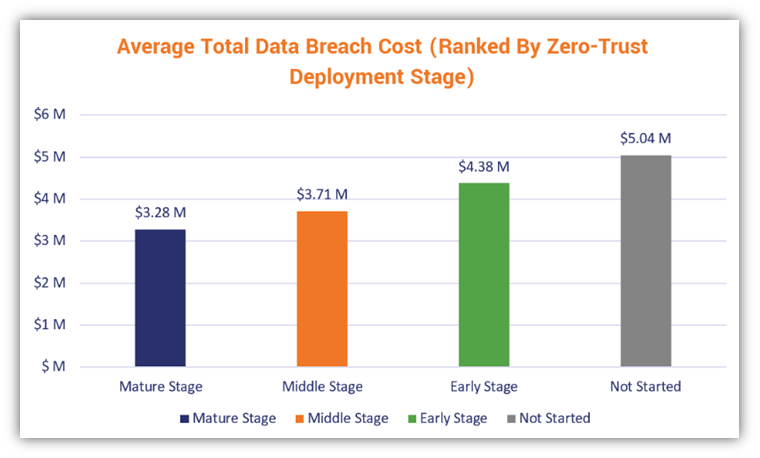
IBM’s 2021 Cost of a Data Breach Report shows that data breaches involving companies with mature zero-trust models in place averaged $1.76 million less in costs than those that lacked zero trust.
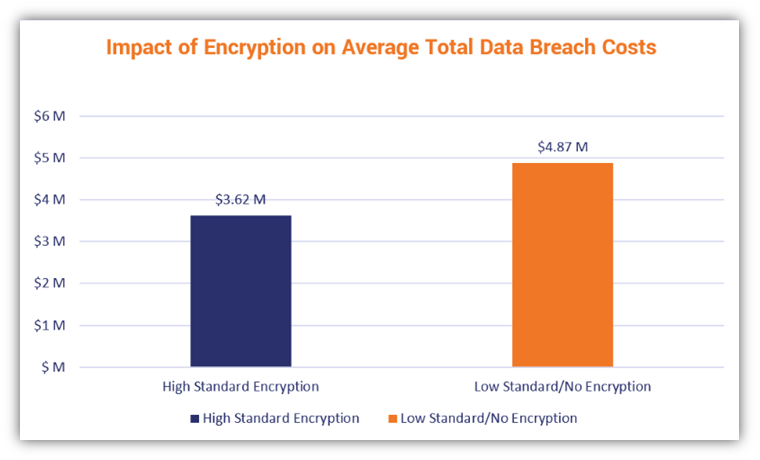
Their research also identified encryption as the leading factor in cost mitigation:
Why Companies Need Custom PKI Solutions (i.e., Private PKI)
Now that we’ve covered the overarching trends that are driving PKI adoption rates, let’s look more specifically at why companies need private PKI solutions.
Publicly trusted digital certificates (such as SSL certificates) are highly effective security tools for securing public-facing websites, servers, emails, etc. These digital certificates are easy to get from a trusted certificate authority (CA), but there is one important caveat: they often don’t work well for internal networks, servers, and devices.
For example, it’s not possible to issue a publicly trusted SSL certificate for a private IP address or internal domain. Certificate authority compliance rules simply don’t allow it. This is why many companies look to alternative solutions that will meet their needs — namely, using a private CA instead. A private certificate authority is what you use to issue certificates that only your internal network knows and trusts.
When used to secure internal resources, private PKI offers several key advantages over public PKI:
- Ability to issue certificates to devices lacking public hostnames or IP addresses (for example, most IoT devices),
- Full control over all certificate processes and policies (not limited by CA/B Forum rules), and
- Nearly unlimited ability to customize and integrate with your systems and projects.
Where Companies Are Using Private PKI
Every PKI project is unique, but some of the most common use cases for private PKI are:
- Secure authentication and communication for IoT devices/networks,
- PKI-based authentication for smart cards,
- Device certificates for VPN or network authentication (far more secure than passwords!),
- Private SSL certificates for securing connections between servers, and
- Private code signing for securing DevOps containers and packages.
DIY vs. Managed PKI
While some companies implement and manage their own private PKI using Active Directory Certificate Services (aka Microsoft CA), the downsides of the DIY approach make it expensive and impractical for many companies:
- Extensive time investment to properly manage the certificate authority,
- Hard costs for a hardware security module (HSM) and other infrastructure, and
- Limited certificate management capabilities, especially on non-Windows devices.
For most companies, using a managed PKI provider is much simpler and actually saves a lot of money once you do a full cost analysis. (We recently talked about some of these costs in an article on how to become a certificate authority and the differences between public and private CAs.)
Companies needing a PKI solution often start with their existing vendors. For IT vendors, this is an opportunity for you to grow revenue — you can meet your customer’s needs by partnering with a PKI provider. Increasingly, PKI providers are recognizing this opportunity and working alongside IT providers to create and implement solutions for companies.
Strong Security Requires Even Stronger Key Management
Of course, your PKI is only as good as the policies and security measures you have in place to protect your private keys. If a key becomes compromised, it’s no longer a secret because anyone with access to it can decrypt your data. Most managed PKI solutions include key management features and secure key storage (using an HSM) to protect your organization’s private keys.
New PKI Partner Programs Help IT Providers Meet Demand
DigiCert’s recent announcement is a great example of the growing demand for custom PKI solutions. On Aug. 31, DigiCert officially announced their Trust Services Group Partner program, which enables IT providers to provide DigiCert’s private PKI solutions to their clients. As you might guess, The SSL Store was an early participant and founding partner in DigiCert’s TSG Partner program (more on that below).
DigiCert offers a range of PKI solutions on their new DigiCert ONE platform, which allows companies to manage all of their PKI-related projects in a single pane of glass. DigiCert ONE solutions include:
- DigiCert® Trust Lifecycle Manager — end-to-end certificate management for private CAs
- DigiCert® IoT Trust Manager — securely manage IoT devices and certificates
- DigiCert® Software Trust Manager — fully secure, auditable code signing platform
- DigiCert® Document Trust Manager — manage document signing workflows and digital signatures
“Current trends such as zero trust, privacy laws, and passwordless authentication are driving more and more organizations to upgrade their security with custom PKI solutions. We’re excited to be working with The SSL Store to help their customers and partners implement PKI solutions that keep their organizations secure.”
— James Dalton, Global Vice President (VP) of the Trust Solutions Group
The SSL Store Partner Program Is Your One-Stop Shop for PKI Solutions
Over the course of 2021 (so far), we’ve expanded The SSL Store’s partner program to meet the growing demand for custom PKI solutions. We now offer custom PKI solutions from many of the industry’s top providers, including:
- DigiCert,
- Sectigo,
- AppViewX,
- Keyfactor,
- Venafi, and
- ManageEngine’s Key Manager Plus.
As an IT provider, you’ll likely need access to multiple vendors to meet the needs of different client projects. Our job is to make the process easy and simple for you — to provide streamline, unbiased support to help you find the right vendor and solution for each project.
Need a PKI solution for your project or a client’s? Contact us and we’ll help you find the best solution for your needs… and, of course, make sure you get the best pricing!
Where’s the PKI Industry Headed?
So, where’s all this heading? What are the trends we’ll see over the next few years? Predicting the future is far from certain, but I expect to see these trends over the next few years:
- Adoption of zero-trust security will continue to grow.
- Demand for custom PKI solutions will continue to grow alongside it.
- Vendors will continue to develop their platforms with the goal of making private PKI simpler to set up and manage.
- Integrations will continue to be a key point — finding a vendor with pre-built integrations for the system you use will be critical. Here’s a few popular integrations ready for use today:
- Servers — IIS, Apache, Nginx, ACME
- Load Balancers — F5, Netscaler, A10, AWS
- DevOps — Ansible, Jetstack, Pupper, Terraform, Docker, Kubernetes
- Users —Active Directory, LDAP, Intune, Sophos
- Some PKI solutions will become easier for small businesses to purchase, implement, and manage.
- Companies will gradually shift towards PKI-based authentication as they realize passwords are no longer enough.
- More IT professionals will use managed PKI services to avoid scripting everything from scratch (this is especially useful when securing complex hybrid environments).






































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)












5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown