New Study Finds 75% of CIOs Are Concerned About TLS Certificate-Related Security Risks
A recent survey from Venafi found that 93% of surveyed CIOs say they have over 10,000 certificates, and 74% said they’d recently experienced a certificate-related outage
Although it sounds like something out of a futuristic sci-fi movie, machine identities are real and they’re here. In fact, if you’re like most organizations that have SSL/TLS certificates on their website, that means your organization also has a machine identity (or maybe many of them).
According to a study from our friends at Venafi, a cybersecurity company that specializes in machine identity protection, Chief Information Officers globally are increasingly concerned about the security risks that relate to those machine identities. But what exactly is a machine identity? How does it relate to SSL/TLS certificates? And what can you do to protect your organization against these risks?
We’ll answer these questions and also share the top takeaways from their survey.
Let’s hash it out.
Key Findings from Venafi’s Global CIO Study
Venafi sponsored a market research study by Coleman Parkes to gain a better understanding of how CIOs regard the risks that are associated with machine identities. In a nutshell, machine identities are what identify your business in the digital world. Businesses, organizations, and governments alike use these machine identities to authenticate and communicate securely across a variety of platforms. The most common types of machine identities in use are SSL/TLS certificates and their corresponding keys.
Considering that machine identities and SSL/TLS certificates and keys go hand in hand, it’s easy to see why this survey caught our attention.
Here are the top five findings to note from participants’ survey responses:
1. 75% of CIOs Worry About Risks Associated with TLS Machine Identities
Venafi’s research indicates that the majority of CIOs are concerned about the security risks that stem from or are somehow linked to machine identities. When asked about whether they’re concerned about the security risks that stem from the widespread use of SSL/TLS certificates and keys, three in four survey respondents say yes. Another 1% indicate that they aren’t sure whether they should be concerned.
The chief concern voiced by nearly two-thirds (65%) of respondents relates to the increased risks that result from the use of expired or compromised certificates. Part of this concern stems from the fact that the use of TLS certificates and keys has skyrocketed in recent years.
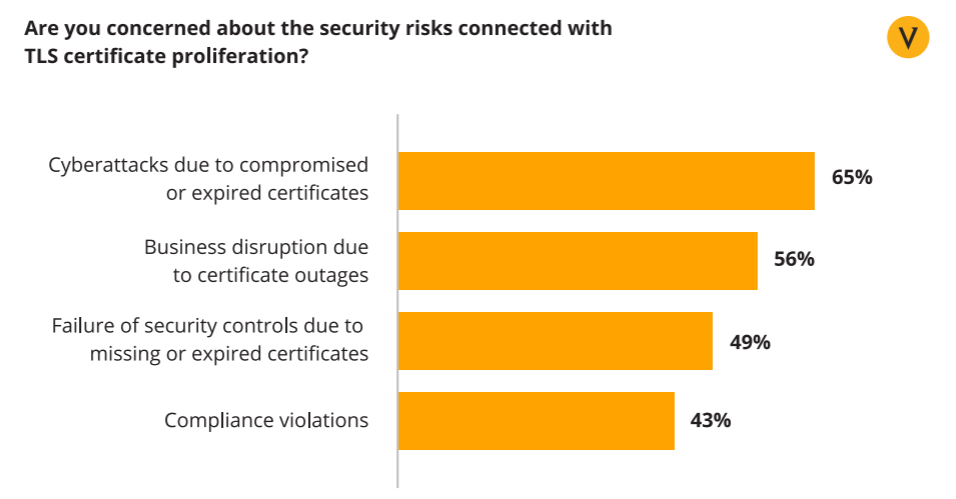
A bar chart breaks down the top security concerns Venafi survey participants voiced relating to the widespread (and growing) use of TLS certificates.
The good news, though, is that it means that the heads of IT and cybersecurity teams are becoming increasingly aware of the need to secure these machine identities.
2. 91% of CIOs Say They Have Complete Visibility of TLS Certificates Within Their IT Infrastructure
It’s great that you have visibility, but how often are you actually looking? It’s not practical to physically look into every nook and cranny of your network and IT infrastructure. But this is where certificate management tools that automatically monitor your TLS certificates are so important.
Certificate outages are a clear sign that organizations lack awareness of the certificates and keys that exist within their IT infrastructure. Considering how common certificate outages are for governments and businesses alike, our concern would be that some of these CIOs are not as aware as they think they are. (Or, at least, they don’t have as much visibility as they believe they do.)
3. 79% of CIOs Know How Many Active TLS Certificates and Keys They Have
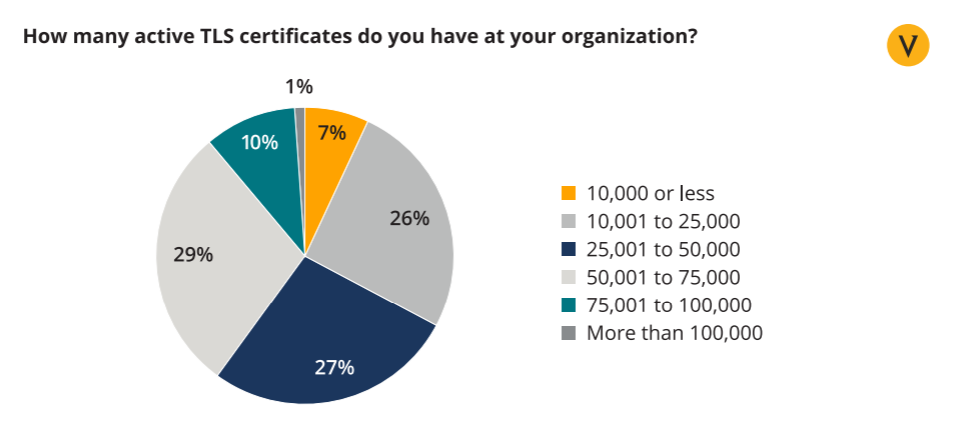
The study reports that more than three-quarters of respondents know how many active certificates and keys exist within their IT infrastructure. In fact, 93% — or nine in ten — of the survey respondents estimate that they have a minimum of 10,000 active TLS certificates that are active, and 40% of them believe that they have more than 50,000 in use.
Again, considering how common certificate outages are, I’d be genuinely surprised if 79% of CIOs really know about every certificate in their organization — it just seems unusually high. A few months ago, we shared research from KeyFactor and the Ponemon Institute that indicated that 74% of organizations have no idea how many digital certificates they have in use.
Now, this isn’t to say that I think the CIOs are being intentionally deceptive. Perhaps, Coleman Parkes surveyed a group of super knowledgeable and cyber-aware CIOs. But I think the most likely situation is that the survey respondents are overestimating their certificate usage awareness (or underestimating their true number of machine identities).
Which number do you think is more accurate?
4. 74% of CIOs Indicate That Their Businesses Had Certificate-Related Outages in Last 2 Years
The CIOs in this study don’t appear to hold any punches when it comes to admitting the certificate outages their organizations have experienced in recent years. Nearly three-quarters of them said they’ve had outages within the past two years. 60% indicate that an outage hit their business within the last year, and 34% indicate it’s happened within the last six months.
As we’ve mentioned, certificate outages typically result from certificate mismanagement. It could be something as simple as allowing a TLS certificate to expire, or a less likely scenario is that it could result from a certificate being revoked by a publicly trusted certificate authority (CA). There is a third possible cause — a CA becoming compromised and distrusted by browsers — but even though it’s happened in the past, thankfully, that’s it’s an even more rare occurrence.
No matter what the cause, the bottom line is that certificate-related outages are bad for businesses.
Outages can result in everything from displaying error messages (the unsightly “Not Secure” warning) to a termination of service. But what makes this worse is that these outages can ultimately result in lost revenue and trust in your organization in the eyes of your customers.
5. Despite Their Concerns, CIOs Recognize That Machine Identities Are Here to Stay
Machine identities are integral to many aspects of digital communications and technologies. TLS certificates and keys can be found everywhere from websites and APIs to mobile and IoT devices. And it’s a trend that’s not only expected to continue but to grow as well. In fact, the overwhelming majority of the survey respondents — a whopping 97% — estimate that the number of TLS certificates their organizations will grow upwards of 20% within the next year!
Many businesses appear to be overconfident in their current abilities to manage their machine identities. So, since machine identities are here to stay for the foreseeable future, and as the number of certificates and keys that they will be using grows, it means that they really need to put aside their pride and look at their current capabilities through an objective lens.
Big Takeaway: The Study Shines a Spotlight on the Importance of Automation
The biggest takeaway from this survey is that it underscores why automating the certificate lifecycle is so important. While smaller businesses and organizations may be able to get away with manual certificate management, it’s damned near impossible for larger organizations and enterprises to do the same. Why? Because small businesses are more likely to have a more manageable number of active certificates in their infrastructure.
Enterprises, on the other hand, could have thousands (or tens of thousands) of active certificates living within their network and other IT infrastructure at any given time. To make manual certificate management work in this scenario, you’d basically have to have multiple full-time employees whose only responsibilities would be managing TLS certificates and keys on a daily basis.
Just the inordinate amount of time, labor, and monetary resources that would have to be dedicated to manual management of that many certificates would be ridiculous. I’m sure you’d agree that there are way more valuable (and productive) ways that your employees could be spending their time. This is why automating the certificate lifecycle can help you protect your machine identities and the security of your organization as a whole.
How Automation Helps Your Business
No one can argue the importance of properly managing certificates — but it doesn’t mean that the tasks associated with it aren’t menial and repetitive. Again, there are better ways for your employees to spend their time than, say, reissuing and rotating certificates. And that’s why a certificate automation tool is critical.
Heck, even NIST agrees. In their special report on securing web transactions, NIST SP-1800-16, the National Institute of Standards and Technology offers guidance for the proper management and securing of TLS certs and keys. And what’s at the core of their framework for securing machine identities? Automation.
A certificate manager automates those boring (yet necessary) tasks, which frees up your tech team to focus on higher-level tasks that require critical thinking. This way, your employees can work on projects that can improve your business or services instead of sloshing through inventory tasks and making sure that expiring certs are swapped out before they cause any security events.
To learn more about certificate management best practices, download our free cert management cheat sheet:
About the Study
The Venafi whitepaper shared the responses of 550 chief information officers (CIOs) from five of the world’s most technologically advanced countries in their whitepaper:
- Australia,
- France,
- Germany,
- United Kingdom and
- United States.
To learn more about the study and the automation best practices it shares, be sure to download Venafi’s whitepaper.






































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)












5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown