TLS Pinning in Mobile Apps
How key pinning could help with mobile app security…
Ask about TLS pinning amongst people who talk about these kinds of things and you’re likely to get divergent opinions.
It’s certainly true there are some risks involved, but there are also some potential benefits. One of the factors to consider is exactly how you plan on making use of key pinning and what you intend to accomplish.
Before making up your mind one way or the other, it pays to learn more about TLS pinning, how it can be used, and what sort of advantages and drawbacks you may experience.
What Exactly is TLS Pinning?
Transport Layer Security (TLS) certificate pinning is a process that makes it possible to increase the security of a site or some sort of service offered through a site. Basically, it’s a way to authenticate that the server certificate associated with the site or application is issued by an authority that can be trusted.
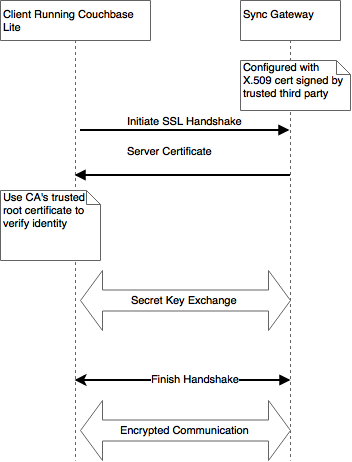
Think of it this way. With pinning, you have an additional layer of security during the handshake that takes place when you initiate a connection to a site or to an app that’s maintained on a server.
Before the handshake is completed, the pinning checks to make sure the certificate is valid, issued by a recognized authority, and can be trusted. If something is out of line, the connection may be denied. At the very least, you get a warning so you can decide for yourself whether or not to proceed.
Keeping TLS certificates active matters. The potential threats associated with expired certificates can create quite a few headaches for just about any type of government, public, or private entity.
How Does This Play Out With Mobile Apps?
People tend to trust apps that they get from whatever store is associated with the operating system used on their smartphones. Much of the time, those apps are perfectly secure. However, there have been events in which apps were infected. When that happens, the store’s typical security defenses may or may not identify the threat.
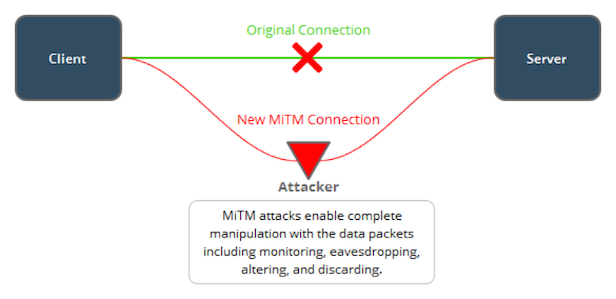
This results in what we call a man in the middle attack (MITM). The compromised app makes it possible for data that’s being transmitted between the point of origin and the destination to be intercepted and copied, and can then be used in any way the hacker desires. Consider the negative possibilities if you are using an app to check the balance in you bank accounts.
Apps are also available outside the device store. Those third-party apps may come with some sort of security or they may not. It depends on who designed the app and what type of security measures they included in the code.
What you will find is that some developers use TLS pinning as a way to enhance security. This is important since the typical safety provisions associated with downloading an app from an approved device store don’t exist.
Make It Harder for Hackers to Compromise Your App
An upside to TLS pinning is that it creates one more layer that hackers must overcome in order to compromise your app. They’ll have a harder time finding vulnerabilities to exploit and using them as a backdoor into the app function.
Since they have to exert more effort and resources into breaking through the encryptions, and still keeping the breach from being detected, they may decide the returns are not worth the time or money.
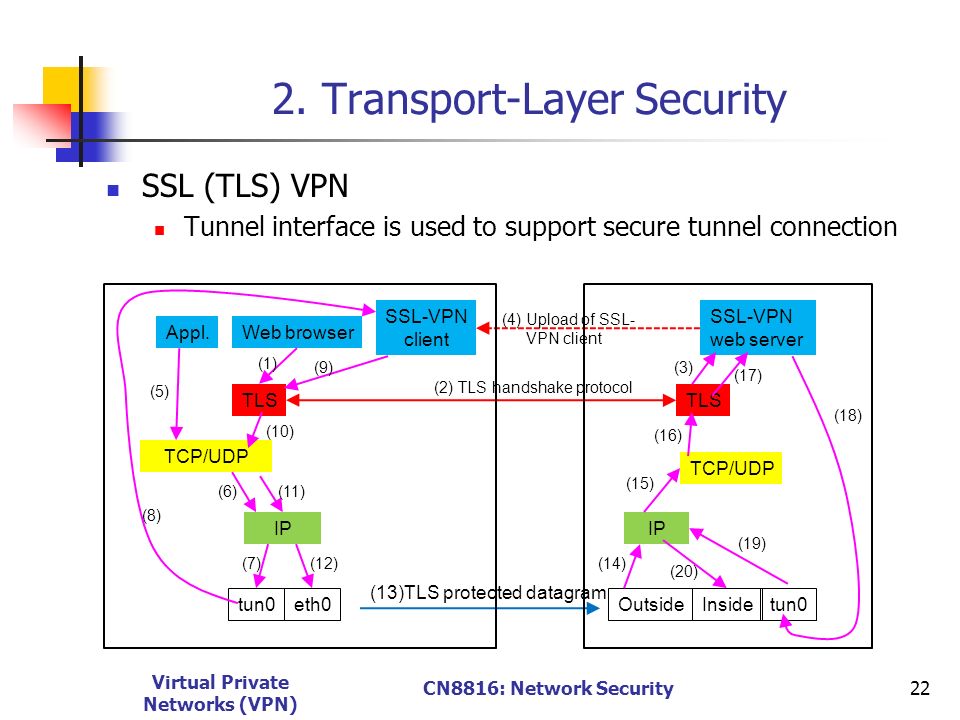
TLS Pinning and VPN Integrity
Virtual private network (VPN) technology use by the general public has increased rapidly in recent years as a means to protect personal data in the face of a rising hacker onslaught.
It works by creating a private encrypted “tunnel” between a user’s device and the internet, which makes it less likely a bad actor will be able to eavesdrop on data in transit during your session.
Now considered part of cybersecurity best practices, disparate organizations like the Small Business Administration, the SANS Institute, and The OWASP Foundation have all added their voices to the call for individuals and businesses of all sizes to use a VPN any time they access the internet.
Coincidentally, a recent study conducted by security expert Bruce Schneier found underlying security vulnerabilities in TLS pinning, one which affected mobile apps for TunnelBear – a popular VPN service – and several banks. Wait a moment now – if TunnelBear – a leading VPN provider – and some of the world’s largest banks are susceptible to MITM attacks as a result of TLS pinning, how secure are other mobile applications? If security sensitive mobile applications like VPNs could expose our personal information via a MITM intermediary, should we be concerned?
Well, one answer is ‘yes,’ and the other is ‘no,’ and both are valid. On one hand, a VPN provider could actually make user data vulnerable. The way this would happen would be if it inspected SSL traffic, similar to what IT teams in companies do to their own employees.This could certainly happen without your knowledge.
If you install a VPN, the software could be silently told to trust a computer from the VPN provider for SSL interception purposes. This would mean – unbeknownst to users – that the VPN provider can watch and even modify encrypted traffic from your internet activities. This could happen without your knowledge because installing the VPN software gives the VPN provider the option to change parts of your system – like the browser – in order to hide any inspection from you.
However, this isn’t necessarily cause for alarm. This type of logging is not restricted to VPN software; any mobile app you install could keep logs of user activity. When you give a software permission to change anything on your computer this is the reality.
This is a perfect example of why you shouldn’t download software willy-nilly. This is the reason why certain software can build up a reputation as being safe and reliable. To its credit, TunnelBear has a history of quickly addressing app vulnerabilities as soon as they’re discovered. Choosing a well-reviewed, widely-used and reputable VPN is the difference between opening yourself up to this specific vulnerability and protecting yourself from it. Third party testing and evaluation of VPN services, like study conducted by Schneier et. al, is essential to patching vulnerabilities in mobile apps, whether they originate from TLS pinning or otherwise.
So yes, MITM vulnerabilities are possible in VPNs and other security-sensitive mobile applications. However, the rate of incidence is low. When deployed properly, a VPN used in conjunction with TLS pinning have the potential to create a strong protective synergy around your data and to secure solid online privacy.
In today’s hack-a-minute world, the more protection you have, the better
Sounds Good So Far: What’s the Drawback?
Smartphones and tablets both utilize apps designed to provide encrypted connections. When you open the app, it attempts to establish a link with a server. The server responds to the attempt by providing a digital certificate. Assuming the certificate is recognized, the connection completes and data can be shared back and forth between the point of origin (your device) and the point of termination (the server.)
Here’s the thing to remember: each of these connections via the app requires something that you could call a chain of trust. That chain includes your device and the app, the server, the list of recognized Certificate Authorities, and the Certificate Authority associated with this particular connection. If there is any hiccup among that chain, there will be a problem connecting.
In the last several years, attacks launched against Certificate Authorities have taken on several forms. One was infiltrating and creating fake certificates in names of organizations that were well known. For example, these breaches made it possible to create fake certificates for Google, Facebook, Twitter, and even email clients.
When hackers have repeatedly breached an Authority and generated a sizable number of fake certificates, trusting the legitimate ones associated with that Authority may not occur. In other words, your app may not trust the real digital certificate and you can’t use it to connect to that server.
And if the preceding wasn’t enough of a reason to think hard before engaging in mobile TLS pinning, you should realize that the process can get so complicated as to spiral out of the grasp of a great many website owners.
If you feel the urge to explore the intricacies of how to accidentally misconfigure and otherwise screw up while pinning, The SSL Store’s own, Vincent Lynch, wrote an excellent article on the topic
And Finally… Keep Your TLS Versions Up to Date
Just like web browsers and other Internet-connecting tools, new versions of TLS are released from time to time. Older versions are supported for a time, but that support eventually ends. If you are a networking guru or someone who creates apps, it pays to know what is currently still supported and for how long.



















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown