What to Take Away from Iran’s Global Malware Campaign
The FBI recently disclosed that Iran’s intelligence agency has been using nation-state actors & a front company to carry out a years-long global malware campaign — here’s what was involved and what we took away from the situation…
On Sept. 17, the FBI released a cybersecurity advisory about eight previously undisclosed sets of malware that are tied to Iran’s Ministry of Intelligence and Security (MOIS). The intelligence agency used them to monitor Iranian citizens, journalists, former government employees and dissidents (among others), as well as international companies in the academic, telecommunications, hospitality and travel sectors. This includes travel companies in the U.S. that have records of millions of travelers.
The attacks, which the FBI estimates has cost “millions of dollars” to U.S. and international companies, have been ongoing for years. (The FBI’s Boston office media representative told me that they couldn’t disclose specifically for how long the malware campaign was running or how much the damages totaled more specifically when I reached out for comment.) As part of their effort to thwart MOIS’s campaign capabilities, the FBI’s Internet Crime Complaint Center (IC3) also released an alert that showcases some screenshots of the codes that were used.
So, what exactly was involved with these malware-based attacks? And what are the key takeaways from this incident that we can learn from?
Let’s hash it out.
What Occurred and Who Was Affected by the Malware Campaign
According to the FBI, MOIS has been targeting Iranian citizens, journalists, businesses and others both domestic and abroad. The used a front company called the Rana Intelligence Computing Company (Rana), as well as nation-state actors known publicly as Advanced Persistent Threat 39 (APT 39), which also were known by a few other names including Cadelspy, Chafer, ITG07, and Remexi.
There were also 45 other individuals that the U.S. Department of Treasury’s Office of Foreign Assets Control (OFAC) imposed sanctions against for being linked to Iran’s MOIS on Sept. 17.
Their goal? In a nutshell, they used their vast resources to target, monitor, harass, repress and exploit anyone that they identified as a threat to the establishment. This includes:
- Iranian citizens, journalists and dissidents,
- University students and faculty,
- Foreign government networks in nearby countries,
- “Hundreds of individuals and entities from more than 30 different countries across Asia, Africa, Europe, and North America,” and
- International and domestic entities in the academic, telecommunications, hospitality and travel sectors (including 15 or more U.S.-based travel organizations).
Basically, this malware campaign has affected a lot of people that the FBI knows of at this point. When MOIS operative caught up with some of the individuals they were monitoring, those targets were often arrested or subject to physical and psychological intimidation.
How to Know Whether Your Business Is Compromised
The FBI stated in their advisory that affected businesses and individuals have been notified. However, the FBI’s Internet Crime Complaint Center (IC3) also released their own alert (alert number ME-000134-MW) that shares the “Indicators of Compromise” that are associated with the Rana Intelligence Computing and its other aliases. The IC3’s goal is to help cybersec pros and sys admins to protect themselves against these types of malicious activities.
According to the FBI’s cybersecurity advisory:
“Until now, most of these technical indicators have never been publicly discussed, nor attributed to the MOIS by the U.S. government. It is anticipated that by making this malicious code public, it will deal a significant blow to the MOIS and mitigate the ongoing victimization of thousands of individuals and organizations around the world, while also imposing risk and consequences on our cyber adversaries.”
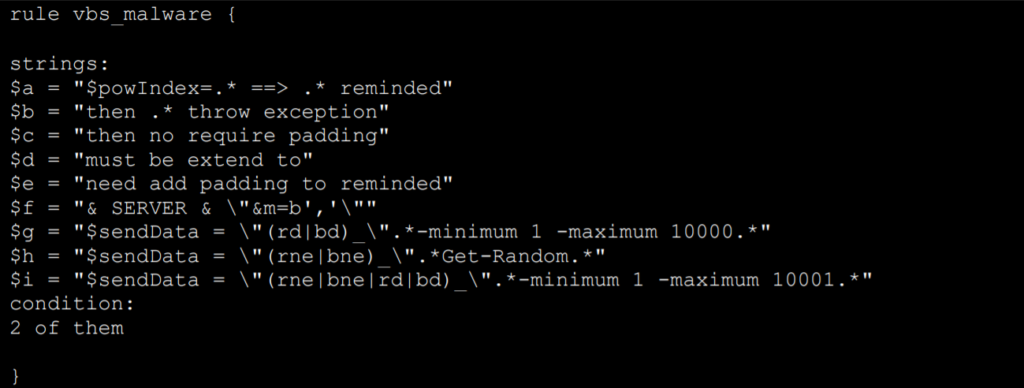
The 26-page resource includes a wealth of information relating to the malicious intrusion tools that the attackers used to carry out their mission. It contains information relating to the eight sets of malware that the FBI was able to identify, as well as YARA rules you can employ to detect these malicious files:
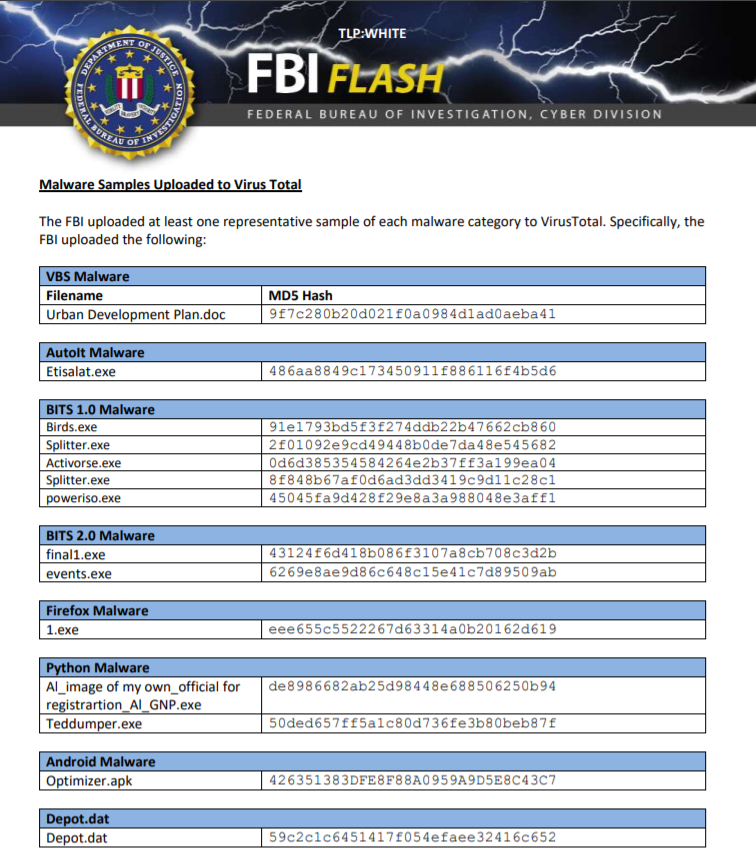
Let’s take a few moments to explore each of these types of malware a little more in depth.
1. Visual Basic Script (VBS) Malware
The IC3’s alert says that the malware, which was embedded in seemingly innocuous Office files, launched scripts that would create files and run commands that would result in the victims’ files being uploaded to attacker-controlled IP addresses.
But how was this malware employed? According to the IC3’s alert:
“The VBS malware was embedded in Microsoft Office documents and sent to victims via spear phishing or other social engineering techniques.”
To identify files that indicate the presence of this malware, the FBI published a list of indicators of compromise (IOC) signatures and also created YARA rules that you can implement. For example, here’s the YARA rule that they created for the VBS malware:
2. AutoIT Malware Scripts
This type of malware causes a script to execute that results in the creation of two new directories and PowerShell commands to run specific files. The PowerShell commands involved also are thought to allow the attackers to upload or download commands and files.
The FBI determined that AutoIT malware and VBS malware are technically very similar in terms of functionality. And also like the aforementioned VBS malware, the AudtoIT malware was also spread via phishing and social engineering tactics.
The FBI published IOCs and created multiple YARA rules for the AutoIT malware set as well as the rest of the malware variants that follow. To view the full list of YARA rule screenshots, check out the IC3 alert resource.
3. BITS 1.0
According to the IC3 alert, this type of malware is thought to work in conjunction with the previous two sets of malware. It would use those malware variants to download the BITS 1.0 malware from attacker-controlled IT systems, which would then be used to collect data from the victims through key logging, screen captures, and other methods. The stolen data would be encrypted and password protected before being sent via the Microsoft BITS protocol back to the attackers systems.
The malware involves the use of multiple executable files, including (but not limited to) Birds.exe and Splitter.exe.
You can view the full list of IOCs and YARA rule screenshots for this malware in the FBI’s IC3 alert.
4. BITS 2.0 Malware
Basically, BITS 2.0 is a separate variant of the BITS 1.0 malware — even using similar communication channels and techniques. However, there are “significant changes in technical details” that differentiates this from its sister malware that the report points out.
For one, BITS 2.0 is self-extracting and contains “an image, an icon, a VBS script, and an executable.” There was also an observed instance of the malware that contained two additional files. The events.exe file basically has the combined capabilities of the Events.exe and Splitter.exe executables of the BITS 1.0 malware. For example, it could:
- Allow the attackers to search for, upload and download files on the targets’ devices.
- Execute command line operations of the victims’ machines.
- Collect and capture a variety of data using keylogging, screenshots, and clipboard data.
- Turn off legitimate BITSADMIN processes.
- Bundle and transmit encrypted data for exfiltration to the attacker-controlled command-and-control (C2) server.
To view the full list of IOCs and the YARA rule screenshots for the BITS 2.0 malware, check out the IC3 alert.
5. Mozilla Firefox-Mimicking Malware
This type of malware that the federal investigators identified is a wolf in sheep’s clothing. Basically, this variant, simply labeled “1.exe,” would disguise itself as a legitimate Mozilla Firefox files, including:
- Multiple .dll files
- Multiple executables including MozillaFirefox.exe, CrachReport.exe, SafeBrowser.exe, and MozillaUpdate.exe.
- Two VBS files, which would create shell commands to run binary for two of the executables.
The IC3 report didn’t disclose how the malware was delivered or wound up being downloaded by the targets. However, there are many ways that the malware could have been delivered — too many to go through here individually. A few of the possibilities we think could include using remote access tools, having direct access to install the malware, or by emailing a link to a fraudulent website where legitimate users could download the files.
You can view the full list of FBI’s IOCs and YARA rule for this malware in the IC3 alert.
6. Python-based Malware
According to the IC3 release, this malware variant was typically contained within a .rar file along with a script named ma.py. Furthermore:
“When run, the file conducted a HTTP GET request to a command and control server conforming to [Actor IP]/service.html. This GET request then downloaded additional malicious files to the victim machine. The file directed additional files from the command and control server to be written out as:
C:\\Windows\\Temp\\ImageVeiwer.exe. The file also directed ImageVeiwer.exe to be run at system reboot.”
To view the full list of YARA rule screenshots that the FBI created, please refer to the IC3 alert.
7. Android Malware
As a type of malware specifically designed to target android devices using an android package kit (APK). Although we don’t know for sure when the malware was deployed, there may be a bit of a clue in the malware metadata certificate information. The certificate was listed as being valid from Dec. 23, 2018 to Sept. 25, 2019.
The malware gave Iranian intelligence remote access and data-stealing capabilities without the users’ knowledge so that they could:
- Retrieve HTTP GET requests from the C2 server for the domain saveingone.com. This domain previously resolved to an Iran-based IP address. This type of server issues updates or commands for affected devices.
- Steal data from the compromised devices. If you’re wondering just how bad that can be, just remember how many people use their mobile devices for just about everything now.
- Compress and AES-encrypt the collected data.
- Forward data via HTTP POST requests to the attacker-controlled C2 server.
- Record audio and video via the targets’ devices.The APK gave the attackers permissions to use the microphone and camera for surveillance on compromised devices to record audio and take photos.
You can view the full list of YARA rule screenshots that the FBI created in the IC3 alert.
8. Depot.dat Malware and Dropper
This type of malware, which comprised an encrypted MS CAB file (depot.dat) and a dropper, enabled the MOIS attackers to do the following and send the resulting data back to RANA-controlled IT infrastructure:
- Capture keylogger information,
- Collect screenshots of the victims’ devices, and
- Collect a variety of other data.
The dropper, which decrypts the encrypted depot.dat file, “establishes persistence” for the malware. The CAB file contains four separate files that enabled the malware to carry out the malware’s data collection, packaging, and exfiltration functions.
You can view the full list of the FBI’s IOCs and YARA rule screenshots in the IC3 alert.
A Few Takeaways From This Situation…
This threat is one that has affected individuals, businesses, governments and other organizations on a global scale. But if you think that Iran is the only government in the world that spies on its citizens, neighbors and other entities of interest, then I’ve got a bridge (or two) to sell you.
No, the FBI’s recent announcement about Iran’s MOIS isn’t the first time a government or group of nation-state actors has been caught spying on others — nor is it likely to be the last. We’ve seen plenty of examples of government spying programs in recent years:
- The U.S.’s National Security Agency (NSA) spied on U.S. citizens in illegal mass surveillance program.
- The U.K.’s Government Communication Headquarters (GCHQ) surveillance programs such as Tempora and The Three Smurfs.
- U.S. and German intelligence used a Swiss encryption company as a cover for surveillance via their products that were used around the world.
- Many nation-state actors used the COVID-19 pandemic to cover for various espionage activities.
Although there are some key pieces of information that we don’t know about the Iran malware situation, let’s consider what we do know. There are a few critical takeaways that extend beyond this situation and speak to the importance of securing data for businesses and other organizations in general.
Telecommunications Companies Are Among Chief Targets for Cybercriminals
In the case of the MOIS malware campaign, the FBI shared that telecommunication companies were among the targeted organizations. This isn’t very surprising considering that telecoms companies make excellent targets for government surveillance and nation-state actors alike. After all, they provide critical communications infrastructure and are trusted with transmitting and storing tons of sensitive data.
Telecommunications companies typically includes internet service providers (ISPs). And if an ISP, for example, becomes compromised, it gives attackers access to all of the data that flow through them. This leaves them with big targets painted on their backs.
Internet service providers aren’t infallible and can become compromised through different means. A few examples include bad guys:
- Teaming up with malicious insiders (rogue employees),
- Targeting and blackmailing employees via social engineering or phishing attacks, or by
- Exploiting unpatched or zero-day vulnerabilities.
Nation-State Actors Can Use These ISPs to Monitor or Steal Your Data
Now, nation-state actors — Iranian or otherwise — could infiltrate those companies to gain access to their networks and data. They can then use their access to monitor and steal valuable data that flows through their systems. And this is why it’s so important that all organizations and other entities take the necessary steps to secure their data and communication channels.
After all, when data travels across the internet, it traverses through potentially dozens of different touch points — modems, routers, networks, servers, etc. That’s a lot of potentially insecure places where bad guys could try to intercept it. We’ll cover more about how this data transmission process works next week (be sure to check back for that one). In the meantime, what does this all mean?
So, as your data travels from one system to the next to the next, it’s going through a lot of different (and potentially vulnerable) touchpoints. And if that information is transmitted using the insecure HTTP protocol, then that information is sent in plaintext. This means that if your ISP is compromised by government or nation-state attackers (or any other threat actors), any of your data that transmits through that ISP is also compromised. So, to protect your data as it zips around the world at outrageous speeds, you need to use encrypted communication channels.
Use Encryption to Protect Your Data (Even From Compromised ISPs)
We’d love to say that if the businesses that were affected by MOIS’s campaign used public key infrastructure and TLS, that they could have prevented their data from being compromised. But the reality is that there’s no way to tell whether the directly targeted companies could have protected themselves through PKI/SSL usage. (I even tried asking the FBI contact whether any of the known victims were using any type of data encryption, but she said that they couldn’t disclose that.)
But we do know one thing for sure—PKI can definitely help protect you if your data is being transmitted by a compromised ISP.
There are two PKI-related implementations that can be useful in helping to protect your organization’s data. Using the secure HTTPS protocol and S/MIME certificates for end-to-end encryption can help you to ensure that even if your ISP gets compromised, your data won’t be.
SSL/TLS Certificates
A TLS certificate (sometimes also still referred to as an SSL certificate) enabled HTTPS for your website. HTTPS (among other benefits) protects you against spying via a compromised ISP…
Since HTTP data exchanges over the internet take place using plain text, basically anyone can read it because the data isn’t encrypted. Without a secure connection to protect the communications, the data transmission could be intercepted by man-in-the-middle (MitM) and altered to include malicious content (such as malware files).
TLS certificates enable your website connections to occur via the secure HTTPS protocol instead of the insecure HTTP protocol. This encrypted communication channel prevents eavesdropping and MitM attack from access your plaintext information. Basically, it’ll just look like a bunch of gibberish since they won’t be able to decrypt the information without use of the requisite private key.
S/MIME Certificates (Email Signing Certificates)
Email signing certificates make it possible to digitally sign and encrypt your email communications. This makes end-to-end encryption possible. (Note: While you can send digitally signed documents to anyone, the recipient would also need to have an email signing certificate installed to exchange encrypted email messages.)
When you use end-to-end encryption to protect your emails, even if any attackers are able to gain access to and download your data, they’d need to have access to the companies’ individual private keys to decrypt and read the data. In other words, without the decryption keys, all the attackers would achieve is capturing a huge amount of data that they can’t use. Those blocks of data are the virtual equivalent of a paperweight. Not exactly useful or profitable for them…
Follow Cybersecurity Best Practices to Harden Your Device and Network Security Defenses
Furthermore, as a general rule of thumb, all organizations and businesses should be following cybersecurity best practices for network and device security. There are plenty of valuable web security tools and processes that you can use to monitor and identify malware-related threats. Examples of these processes and solutions include:
- Implementing access controls to ensure that only those who need access to sensitive data or IT systems have it.
- Using signature- and behavior-based antivirus and anti-malware solutions.
- Performing regular updates and patching to software, devices and IT systems.
- Conducting vulnerability assessments and scans to identify vulnerabilities.
- Implementing penetration testing to identify exploits.
- Implementing web application firewalls (WAFs).
- Employing email filtering to cull suspicious (and potentially malicious) messages
- Implement SPF, DKIM and DMARC to prevent people from spoofing your domain in phishing and other malicious email communications.
- Conduct server network analysis.
- Perform regular cybersecurity awareness training for all of your employees and users who have access to your network and other systems.
- Implementing computer use policies to ensure that users only use organization devices for official purposes and not, say, surfing the internet.





































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)













5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown