Phishing-as-a-Service: Turn-key Phishing Kits
Cyren reports finding over 5,334 unique phishing kits just this year
Historically, phishing – like most cybercrimes – has had a technical barrier to entry. As in, you needed to have at least a moderate degree of sophistication in order to successfully mount a phishing campaign. Obviously not much. There’s no shortage of bad phish – I see two or three drop into my junk folder per day – but it still wasn’t something a layman could pull off.
That is no longer the case.
Enterprising cybercriminals have now brought phishing to the common man with turn-key phishing kits and Phishing-as-a-Service (PhaaS) products that come with subscriptions and varying levels of service. There is no longer a technical barrier – only a financial one.
So, today we’re going to talk about the rise of phishing-as-a-service and turn-key phishing kits, but we’re also going to look at the evolution of the cybercrime economy, which is beginning to embrace platform capitalism and other more traditional business practices.
Let’s hash it out.
Subscribe to Phishing-as-a-Service just like you would Netflix
Cyren is an IT security company that offers a Security-as-a-Service and threat intelligence solutions. I mention this because it’s a great jumping off point to quickly explain the whole ‘as-a-service’ concept to anyone that isn’t familiar.

Whereas traditional software came in the form of a download (or, back in the days of antiquity you could purchase it in a physical format at a brick-and-mortar store) that resided on the user’s device, software-as-a-service (and similarly infrastructure-as-a-service and platform-as-a-service) is hosted on the provider’s servers and made available via the internet. It’s a form of cloud computing.
There are several advantages to this business model:
- Financial – For users, rather than purchasing software, and potentially hardware, they simply pay for a monthly or yearly subscription. For providers, rather than a single, one-time payment you receive recurring payments for the life of the subscription.
- Scalability – Services can be accessed on demand, and the user can choose to access more – or fewer – features and services based on their specific needs.
- Updating – Rather than wait for users to download and install updates and patches, the provider can handle updates itself on its own servers and roll them out to users on its own timetable. This reduces IT burdens on the user side.
- Accessibility – Users can access the service anywhere they can access the internet, whereas traditional software needs to be installed on each individual device you connect from.
Now apply that to any “as-a-Service” product you come across and you should have a solid idea how it works – whether it’s a security product or a video game.
Phishing-as-a-Service and Turn-key phishing kits
In a July 1st blog post, Cyren reports finding 5,334 unique, turn-key phishing kits just from 2019. These are products offered by the aforementioned “Phishing-as-a-Service industry.” If the fact it’s big enough to refer to as an industry troubles you, that’s just the tip of the iceberg when it comes to the cybercrime economy – we’ll get to that in a minute though.
These PhaaS operations offer both one-off turn-key phishing attack kits for as little as $50; as well as full-service subscriptions that, on average, cost $50-80 per month. They even offer discounts. Here’s an example, courtesy of Cyren:
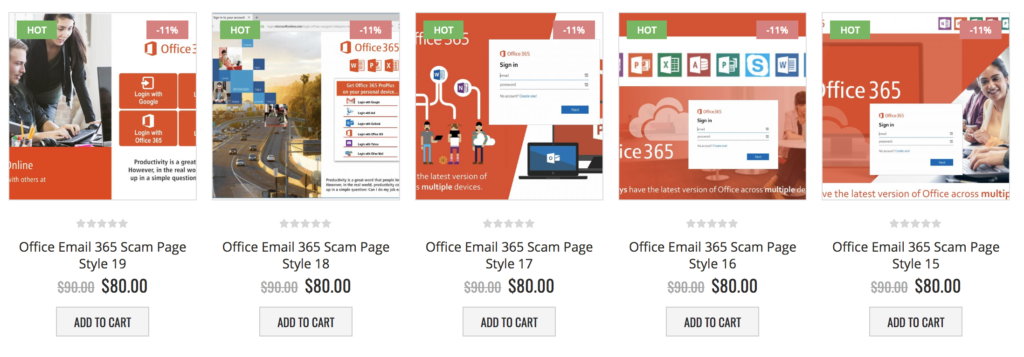
We’ll touch on this more in a moment, but just take a second and look at the presentation of these products. This doesn’t look like some fly-by-night criminal operation – this is a legitimate eCommerce website. Complete with shopping cart, product ratings and a professional-looking UI. They’re even using proven marketing tactics like the decoy effect and price priming. These criminal enterprises are leveraging traditional, legitimate business practices to push their products.
Better phish than you can catch in the wild
One of the additional benefits of the SaaS business model that we didn’t list earlier is that it provides a strong incentive for providers to continue refining and improving their products. After all, if it’s ineffective or goes stagnant then customers are going to start abandoning ship and money will be lost. Phishing-as-a-Service is no different. Only in PhaaS’s case, that benefit is pernicious. Because it means the phish are evolving, becoming better – sentient. Ok, not sentient, but smarter.
Per Cyren:
A straight line can be drawn between the availability of such kits and turn-key phishing platform services and the growth in evasive phishing—phishing attacks that use tactics to confound detection by email security systems. Today’s reality is that we are seeing more evasive phishing campaigns in the hands of more attackers at less effort and lower cost than in the past, as technically sophisticated phishing attack developers have adopted a SaaS business model to let even the most amateur criminal wanna-be [sic] spoof targeted web sites with a high degree of authenticity and embedded evasive tactics.
Obviously, none of that is good. Cyren reports that 87% of phishing kits include evasive techniques, and that’s really a matter of semantics. Cyren has six techniques that it defines as evasive and it looks for the presence of at least one of those before saying a kit uses evasive techniques.
- HTML Character Encoding – A form of Unicode Phishing
- Content Encryption – Sending encrypted email or attachments
- Inspection Blocking – Employing blocklists to prevent scanning and inspection
- URLs in Attachments – URL-based attacks
- Content Injection – Injecting phishing content directly into a website
- Legitimate Cloud Hosting – Hosting websites on AWS, Azure, etc.
Six different evasive techniques, all intended to fool mail clients into delivering the email. That’s their approach.
We tend to categorize phishing techniques a bit differently at Hashed Out. In fact, Casey wrote about this very thing on Friday, listing 10 different types of phishing attacks and scams.
10 Types of Phishing Attacks and Phishing Scams
There’s more than just one type of phish. Knowing what to look for can help your organization from getting swallowed. Here are 10 different types of phishing.
Every phishing email attempts to be evasive. Some more successfully than others. Historically, the evasiveness of a phish was indicative of the level of technical sophistication of its creator. That’s what makes Phishing-as-a-Service so worrisome – anyone with a little bit of cash can now send convincing phish.
The biggest barrier to entry has been removed.
This is indicative of a larger pattern with the cybercrime economy
The cybercrime economy generated – by conservative estimates – $1.5 trillion dollars in 2018.
| Crime | Annual Revenues |
| Illegal online markets | $860 Billion |
| Trade secret, IP theft | $500 Billion |
| Data Trading | $160 Billion |
| Crime-ware/CaaS | $1.6 Billion |
| Ransomware | $1 Billion |
| Total Cybercrime Revenues | $1.5 Trillion |
Crimeware-as-a-Service, a category that includes Phishing-as-a-Service, generated a modest $1.6 billion. That’s still more than the GDP of the Solomon Islands. That figure looks to increase in 2019.
Here are some other services you can purchase via the SaaS model:
| Cybercrime Product or Service | Price (in US Dollars) |
| SMS Spoofing | $20/month |
| Custom Spyware | $200 |
| Hacker-for-Hire | $200+ |
| Malware Exploit Kit | $200-$700 |
| Blackhole Exploit Kit | $700/month or $1,500/year |
| Zero-Day Adobe Exploit | $30,000 |
| Zero-Day iOS Exploit | $250,000 |
But the larger trend is that the lines between legitimate enterprise and criminal enterprise have begun to blur in ways we never expected. We mentioned earlier how professional the storefront that was selling turn-key phishing kits looked, but that trend didn’t start with PhaaS. The biggest generator of cybercrime profits are illegal markets. And a huge part of that is counterfeit goods.
In 2017, just counterfeit fashion goods – clothing, textiles, head wear, footwear, handbags, makeup, watches, etc. – amounted to $450-billion in illicit profits just by itself. But you can counterfeit just about anything, from children’s toys to medicine. And most people never have any idea they’re buying a fake.

That can be attributed to the same types of convincing eCommerce storefronts (and marketing tactics) we saw in the PhaaS example earlier. Oftentimes, the sales don’t even occur at the retail level, they occur at the wholesale level when unsuspecting buyers purchase fake goods in bulk and market them legitimately. Regardless, whether its retail or wholesale, more than just the product needs to be imitated. The supplier needs to appear legitimate; it needs to look like a real business. In fact, in most senses these criminal enterprises ARE legitimate businesses in every context but legality.
This trend has permeated across the entire cybercrime economy. And it shows no signs of abating. Some of these criminals have a real business sense. And now anybody with a few bucks can phish or hack with the best of them.
I think its fair to say this is the dark side of capitalism.
As always leave any comments or questions below…




















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown