What Is API Security & How Do You Achieve It? 10 Essential Methods to Know
Salt’s research shows that 17% of organizations have experienced a breach resulting from an API security gap. Don’t become one of them.
Data from Salt underscores why API security (i.e., application programming interface security) is so important. The firm’s State of API Security Report Q1 2023 observes a 400% increase in unique attacks on its customers compared to the previous six months, with 31% experiencing sensitive data exposure. One result of this is that API security is no longer seen as simply an engineering concern: It is now increasingly on C-level executives’ radar.
Twitter’s 2022 API security breach serves as just one example of the dangers relating to API vulnerabilities. A security vulnerability first disclosed in December 2021 resulted in hackers stealing data belonging to over 5.4 million Twitter users. They released the data on the dark web in July 2022, causing the company plenty of embarrassment and reputational damage.
If your organization doesn’t want to follow in Twitter’s footsteps, it’s time to focus on API security. This article provides an overview of 10 important API security methods to know and implement within your organization.
Let’s hash it out.
Defining API Security and Its Importance
API security refers to the holistic approach you take to keep your APIs safe against malicious attacks. It encompasses a wide range of security practices, tools, documentation, and procedures — all designed to ensure that businesses can prevent API attacks and mitigate any damage when such attacks do take place.
The use of APIs in public and private sectors has exploded in the past few years. These interfaces now underpin vital IT infrastructure around the globe and can be found in the digital environments of everything from financial and government organizations to healthcare services. Given their popularity and widespread usage, it’s time to put application programming interface security under the microscope.
Given that APIs expose data and application logic, API security has become hugely important to businesses. From a technical perspective, web API security largely involves (although it’s not limited to):
- Implementing authorization and authentication processes. You can do this through methods such as using static strings, tokens (either dynamic or user-delegated), etc. This approach ensures that you are in full control of who accesses your API and how they do so.
- Creating and rolling out policy-based access controls. This approach enables you to implement security via policies, rather than doing so for each individual product. This is ideal for those exposing multiple APIs.
- Instituting role-based access controls. This enables a granular approach to access levels, with differing access linked to different roles within your organization.
- Implementing rate limiting. This will help you to ensure that your API is protected from excessive system traffic that can bring everything to a standstill, thus protecting against distributed denial of service (DDoS) attacks.
Examples of the Most Worrisome API Security Vulnerabilities
When it comes to security vulnerabilities, OWASP is a highly regarded authority for software and web application security environments, including APIs. Its “top 10” lists consider vulnerabilities, attack scenarios, and prevention methods. OWASP recently shared its Top 10 API Security Risks — 2023, the order of which was as follows:
- “Broken object level authorization” — This is where hackers exploit this by manipulating object IDs to access sensitive data.
- “Broken authentication” — This entails a lack of protection mechanisms and identity validation mis-implementation that set the scene for hackers to take control of accounts.
- “Broken object property level authorization” — This occurs when hackers can read and change object values that they shouldn’t be able to access, enabling unauthorized data disclosure.
- “Unrestricted resource consumption” — This is where APIs lacking consumption limits are vulnerable to DDoS attacks by overwhelming your available resources.
- “Broken function level authorization” — This is where hackers attempt to access administrative functions by sending API calls to endpoints or other resources that they shouldn’t be able to access.
- “Unrestricted access to sensitive business flows” — This occurs when an attacker takes advantage of a legitimate, sensitive business flow function (e.g., making a purchase) via automation to cause harm.
- “Server-side request forgery” — This occurs when hackers access a Uniform Resource Identifier (URI) and use it to bypass an endpoint’s API security mechanisms.
- “Security misconfiguration” — This is where hackers use automated tools to detect unpatched flaws, unprotected directories or files, and other vulnerabilities that enable access to sensitive data and/or system details.
- “Improper inventory management” — This when attackers capitalize on orphan and shadow APIs (i.e., forgotten or unknown assets), providing hackers with unmitigated access.
- “Unsafe consumption of APIs” — This is where third-party APIs create the potential for hackers to exploit security flaws, meaning developers need to be careful about trusting such interactions.
Given the breadth of these vulnerabilities, it is perhaps unsurprising that 80% of organizations report that ensuring API security is a challenge – with 36% reporting API security as a significant issue.
How Do You Achieve API Security? 10 Examples of API Security Measures
When it comes to defending themselves against the above vulnerabilities, businesses exposing their APIs are not without a decent armory of resources. Let’s take a look at some handy tools and techniques you can include in your arsenal.
1. Use Well-Established Standards for Access Control & Access Management
Using well-established standards for authorization and authentication flows is an important way to try to avoid security issues while ensuring it is still easy for authorized users to consume your API. Some important aspects of identity and access management practices include:
- Creating strong, PKI-based digital identities
- Implementing and enforcing strong access controls
- Adhering to industry standards and best practices
Implementing OAuth and OpenID Connect may help meet your needs in this respect.
2. Always Use TLS Encryption (HTTPS)
TLS encryption secures your data in transit using encryption (this enables a secure HTTPS connection, otherwise known as HTTP over TLS). Using TLS means that the messages flowing through your API to your server will be securely encrypted and, thus, secure from the prying eyes of malicious actors.
(This way, if they do intercept your data, all they’ll see is a bunch of gibberish. They won’t be able to decrypt the data without having access to the secret key.)
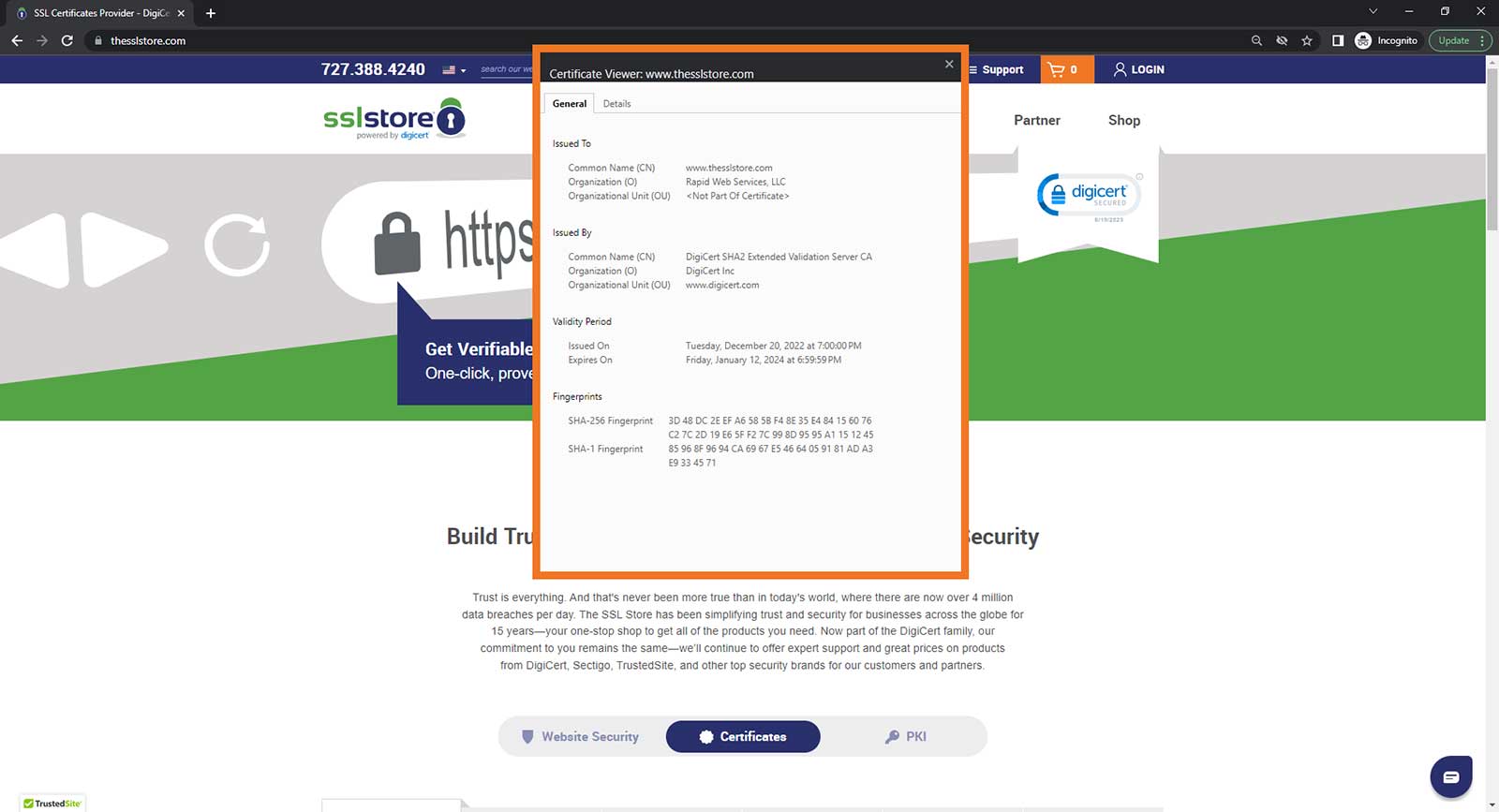
You can enable HTTPS encryption by installing an SSL/TLS certificate that’s issued by a publicly trusted certificate authority (CA) onto your web server. These certificates come in three validation levels (domain validation, organization validation, and extended validation) and provide assurance that the website’s digital identity is authentic.
3. Enable Mutual Authentication
Using mutual authentication is another important way to address API security. You can use public key infrastructure (PKI)-based client authentication certificates and mutual TLS authentication using policy expressions to ensure that both the server and client certificates’ properties match pre-defined values.
4. Validate and Sanitize Inputs
For interaction with third-party APIs, the emphasis should be on input validation and sanitization:
- Validation checks to see that the input meets your pre-defined criteria.
- Sanitization modifies any non-compliant input to enable it to be validated.
When implemented correctly, validation and sanitization can help avoid SQL injection attacks (these are where a cybercriminal injects malicious SQL commands into API requests that can steal, manipulate, or delete data).
Check out OWASP’s Input Validation Cheat Sheet to learn more about how to perform input validation.
5. Implement Rate Limiting
Rate limiting, along with quotas and throttling, can help to reduce your organization’s vulnerability to DDoS attacks. Rate limiting controls the amount of traffic that can access your API at any given time, meaning that bad actors can’t overwhelm it and knock your service offline. Think of it as something akin to a funnel channeling water; a lot of traffic comes in on one end but gets funneled down to a smaller amount on the other. This prevents too many calls from coming in simultaneously and overwhelming your system.
You can set API rate limits in several ways based on the number of requests you want to receive in a set period, and whether they’re authenticated or unauthenticated calls. For example, you can set it to limit client calls to your API to one per second, or maybe 100 per minute.
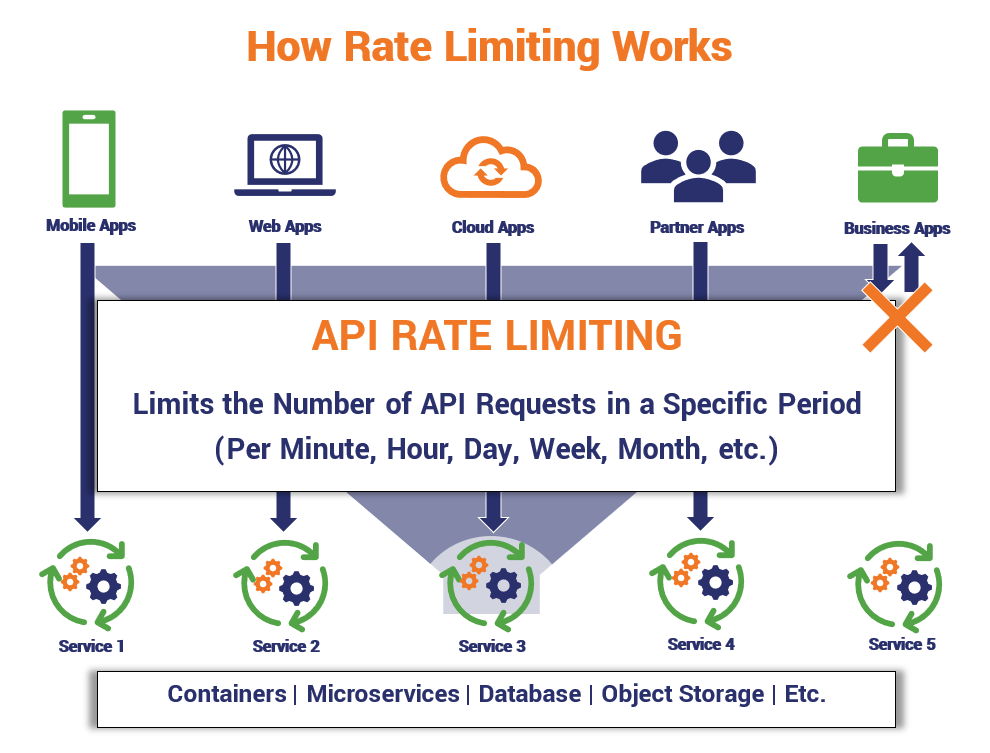
Any decent API management solution should offer rate limiting so that you can easily defend against such attacks.
6. Focus on Regulatory Security Requirements
API security requires a multi-layered approach that accounts for varying requirements, including differing regulatory obligations. A business focused on anti-money laundering (AML) compliance, for example, will have a different focus than a company aiming to meet its security obligations under the Health Insurance Portability and Accountability Act (HIPAA) or Payment Card Industry Data Security Standards (PCI DSS).
Yet, whether it’s the implementation of an AML compliance program, the protection of patient data, or anything else related, there are certain API security best practices that apply.
Key to this is ensuring that API security is addressed as part of an overarching cybersecurity strategy that adheres to industry standard best practices (relating to PKI certificate management, key management, and so on). For example, always ensure that you’re storing your API keys (and other cryptographic keys) securely outside of your application (i.e., don’t embed it in its code or source tree).
Many organizations opt to use a key vault, physical hardware storage module (HSM), or a trust management solution.
7. Take a SecDevOps Approach
Another way that you can boost the security of your APIs is to “shift left” that security — i.e., move it to an earlier stage of the development timeline within the development lifecycle. Instead of designing and building an API and then implementing security testing using the traditional DevOps or DevSecOps approach, shifting security left as part of a “SecDevOps” philosophy supports the implementation of security testing as a fundamental part of the build process.
This way, API security is an integral part of the process throughout and isn’t regarded as an afterthought.
8. Use a Secure API Gateway
Taking advantage of evolving API management tools can also help improve your API security. For example, using API gateways means that organizations can implement robust security at the gateway level, rather than leaving it to individual teams to determine and implement security mechanisms. Think of it as the gatekeeper that restricts or permits access to your applications and data.
Implementing full lifecycle API management via a product such as Tyk API Gateway, for example, supports standardization across a company’s APIs.
9. Get into the “Zero Trust” Mindset
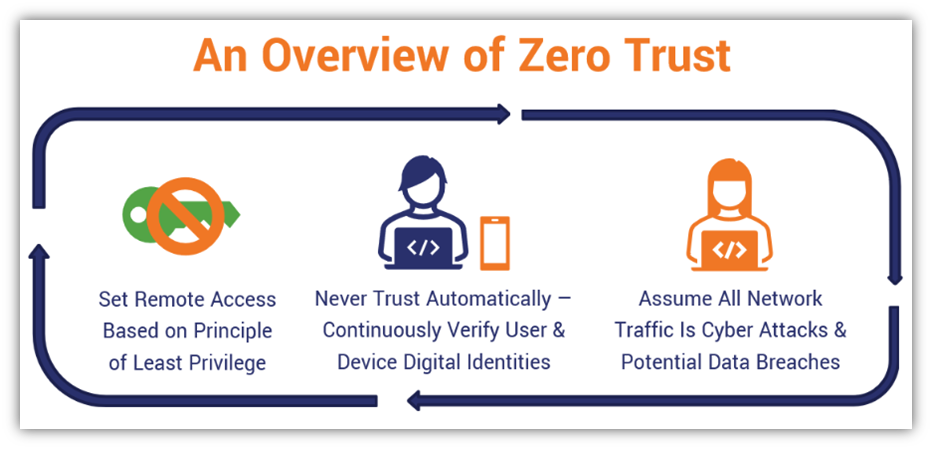
A zero trust security mindset and model is another way to enhance your API security. It’s all about verifying everything automatically and trusting nothing within your network and other systems. This requires continuous authentication throughout a connection.
Adoption of zero trust security is growing rapidly, with the zero trust security market expected to achieve a compound annual growth rate (CAGR) of 17% between 2023 and 2028. Zero trust is a boon for security because no users or devices are trusted by default; rather, they have to be verified every time, even if they were previously trusted.
10. Take a Robust Approach to Testing
Finally, it’s essential that organizations re-check their API security after patches and bug fixes are implemented. (Applying patches can fix some issues but also create others.) You can use automated testing to do so on your site, but manual oversight is a must as well. Implementing regular penetration testing is also important.
Don’t have the internal resources to handle such tasks? You could hire a third-party firm to perform this important function to discover any security vulnerabilities that your API may have. This way, you can discover what vulnerabilities you have rather than leaving them exposed and at risk of exploitation by a hacker.
Final Thoughts: Prepare for the Future With API Security
Cybersecurity is top of mind for many businesses. 2022 was a difficult year for businesses and consumers alike when it came to security, emphasizing the importance of preparing for a future of better API security.
Thankfully, as API security threats grow, so, too, does our understanding of how to combat them. Between zero trust methodologies, shifting security left in the API design process, and baking security into API management processes and architectures, organizations can have the knowledge and tools they need to prepare for a more secure future for application programming interfaces.







































![A Look at 30 Key Cyber Crime Statistics [2023 Data Update]](https://www.thesslstore.com/blog/wp-content/uploads/2022/02/cyber-crime-statistics-feature2-75x94.jpg)











5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownPayPal Phishing Certificates Far More Prevalent Than Previously Thought
in Industry Lowdown