Compromised Credentials: 7 Ways to Fight Credential Attacks
92% of cyber security & app development professionals reported to Axiad that they’re worried about compromised credentials stemming from phishing social engineering attacks. Here’s what you can do to strengthen your organization and its secrets against credential attacks.
Credential attacks are a growing issue. Earlier this year, Microsoft Tweeted in a series of five messages that Russian hackers used “a variety of password spray, brute-force, and token theft techniques” and “session replay attacks to gain initial access to cloud resources leveraging stolen sessions likely acquired via illicit sale.” These attacks use residential proxy services to hide where the attacks are coming from.
This is just one example of some of the credential attacks we’re seeing against organizations. There are many others occurring virtually every day, as cybercriminals increasingly try to get their hands on as many compromised credentials as possible. In fact, Verizon reports in its 2023 Data Breach Investigations Report (DBIR) that 86% of web application attacks involve the use of compromised credentials.
Microsoft released a patch in March to address the security issue described above, but recently (June 21) posted that there’s been an increase in these types of credential attack activities targeting “governments, IT service providers, NGOs, defense industry, and critical manufacturing.”
So, what can businesses do to fight back against attackers who want compromised credentials and harden their security against credential attacks?
Let’s hash it out.
How Your Organization Winds Up With Compromised Credentials in the First Place
News about compromised credentials has become a regular part of our personal and professional lives (unfortunately). When we talk about “compromised credentials,” we’re referring to when someone other than you has access to your username and password — namely, a cybercriminal who doesn’t have your best interests at heart. This can happen as easily as someone taking a sticky note or journal from your desk if you’re someone who writes down your passwords.
In a digital world, it’s easy to see what makes usernames and passwords attractive targets for bad guys. Your username and password are the virtual keys to your kingdom — they provide access to everything from your devices and online banking accounts to your email and other communication platforms. And if those secrets fall into the wrong hands, your professional and/or personal lives would be the worst kind of nightmare.
Poor credential management is one factor that can contribute to broken authentication. Unfortunately, there are plenty of ways that attackers can compromise your employees’ or customers’ credentials. Let’s explore several of them:
Bad Guys Use Phishing Attack Tactics to Reel In Victims
This is a really broad category. Phishing is both a category of cyber attacks as well as a specific type of attack method.
Common types of phishing attacks include:
- General phishing — This is when cybercriminals send general phishing emails to massive lists to see if they get any responses. Using a fishing analogy, they cast their nets into the water to see what they can drag in. These tactics are largely untargeted and have lower rates of success, but they still equal a payday for attackers.
- Spear phishing — This attack is highly targeted and involves an attacker writing emails that include specific information. Rather than fishing with a wide net, this type of attacker is like a surfcaster — someone who fishes on the beach using multiple rods. They set their lines with bait and then sit back and wait to see what bites.
- CEO fraud — This type of attack involves someone pretending to be a manager or other high-ranking official within your organization. They use this perceived position of authority to trick, threaten, or manipulate employees into handing over login credentials or performing a wire transfer.
But if these things weren’t bad enough, some cybercriminals will use human nature itself as a tool to take their attacks to the next level.
Cybercriminals Use Social Engineering Tactics to Manipulate or Trick Their Targets
Social engineering is a category of tactics bad guys use in cyber attacks. Social engineering is the practice of using human emotions against people to get them to do something they normally wouldn’t (and shouldn’t) or to gain access to something.
Compromised credentials are the target in 76% of attacks involving social engineering. Data from Verizon’s previously mentioned 2023 DBIR shows that your username and password are among their favorite things to steal.
Now, put yourself into your employees’ shoes when facing these threats. Cybercriminals will do their homework to learn about you from publicly available sources (social media accounts, digital newsletters, public directories, aggregate data-sharing sites, etc.). This enables them to guess your accounts’ passwords or security prompt responses.
However, some bad guys prefer a more direct approach. Many social engineers would rather use what they’ve learned about you to trick or manipulate you into giving them your login information or a security authentication code — perhaps, for example, by pretending to be an employee at your bank who wants to “help” you resolve a security alert.
Regardless of which tactic they take, their goal is typically to get their hands on your login info.
Bad Guys Infect Devices With Malware to Carry Out Surveillance or Steal Data
It’s no secret that bad guys love malware. There are literally millions of malware programs out there with new ones being created every day, and many of them are used by attackers to get your compromised credentials.
One such example is called a keylogger. A keylogger is a malicious software application that records your keystrokes and sends that data to the attacker who deployed it. It can be an independent program, or a keylogger can be embedded in another program to help it evade detection.
Bad Guys Steal Login Information via Man in the Middle (MitM) Attacks
This method of attack involves compromising the connections that people use to access the internet or specific websites. In these attacks, MitM attackers place themselves between users’ browsers and the services or websites they’re connecting to. By doing this, they’re able to intercept the data in transit — including sensitive login credentials — so they can use it however they want.
3 Common Credential Attack Methods to Look Out For
Now that we know how bad guys get their hands on compromised credentials, it’s time to see what they do with them. There are three common types of credential attacks that cybercriminals love to use:
- Brute force attacks — In these types of attacks, cybercriminals repeatedly try to guess username/password combinations by running through lists of common passwords. Although this particular method doesn’t require them to have compromised credentials available, it’s still a form of credential attack because they’re trying to guess yours. (Check out this article on brute force prevention techniques to learn more about how to prevent these attacks.)
- Credential stuffing attacks — These attacks are similar to brute force attacks, but they involve an attacker using a leaked or stolen list of username/password combinations to see if they work on specific websites. This is where having databases of compromised credentials comes in handy for bad guys.
- Dictionary attacks — In these attacks, bad guys use lists of words from the dictionary in combination with common usernames (Admin, manager, user, IT.admin, etc.) to see if any provide access to accounts on different websites.

What Damage Attackers Can Cause While Using Compromised Credentials
Using any of these credential attack methods may give an attacker access to your network, email server(s), website, or other digital assets. A few examples of how they can use their newfound access include:
- Exfiltrating sensitive customer data, intellectual property, and other information from your systems.
- Sending phishing or malicious emails from your legitimate account using business email compromise (BEC) attacks to target your customers, partners, vendors, or other associated organizations.
- Upload malicious code and files to your website.
7 Steps You Can Take to Prevent or Fight Credential Attacks
Now that you know what compromised credentials consist of and how bad guys continually seek to get their hands on them, it’s time to look at some of the ways you can fight back against credential attacks that use them. This section encompasses both preventative and reactive methods.
1. Evaluate Your Identity and Access Management Systems to Identify Areas of Improvement
Dedicate the time to review and analyze your company’s network, website, servers, APIs, and other resources. In addition to taking stock of what you have, you can determine how these resources are accessed and what security measures you have in place to secure access to them.
Be sure to create useful documentation that specifies what you want admins to do and how you want them to carry out those tasks. Not only does this information serve as a useful resource for admins, but it also aids compliance audits and helps to ensure that T’s are crossed and I’s are dotted properly.
2. Set Up Robust Access Controls to Ensure Only Users Who Need Access Have It
An important component of access control is creating lists of privileged users based on their roles or permissions. These lists give users the authorization to access specific systems and data. Think of an access control list (ACL) like a VIP list at a nightclub or a membership at a country club: if you don’t have access, you won’t get in. The assigned level of access you have is what determines what you can access within each protected asset.
A few examples of some common ACLs include:
- Content management system access control lists
- Filesystem ACLs
- Active Directory (AD) ACLs
- Network ACLs
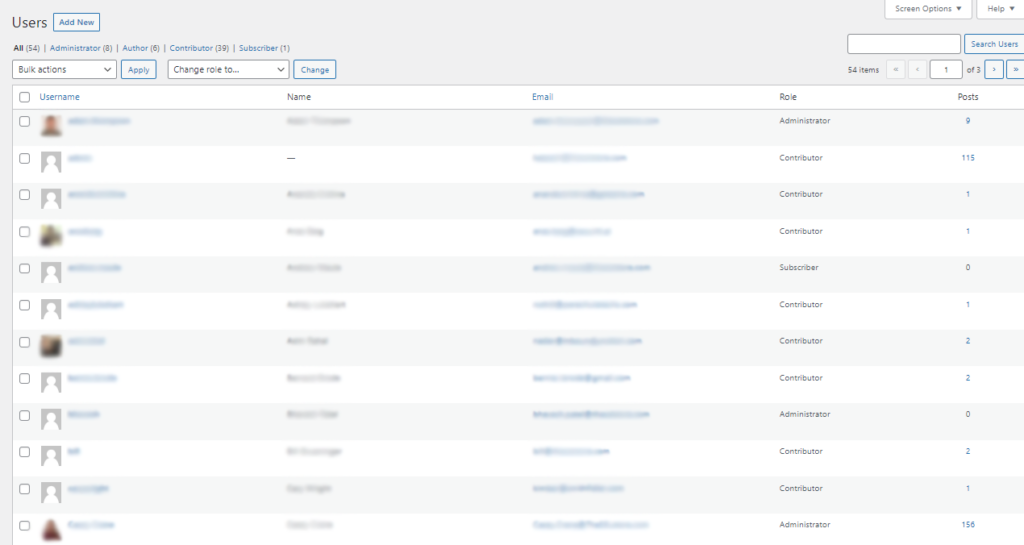
If someone isn’t on these lists, then they won’t have access to those resources. The fewer people who have access, the better it is for your organization’s security. By reducing the number of privileged users, the more you reduce your organization’s attack surface.
3. Implement and Enforce Strong Password Security Requirements
Passwords are the traditional means of securing access to an account or digital asset. And passwords in and of themselves aren’t bad; they serve useful purposes. It’s how people use, secure, and store those passwords that are often at the heart of password security issues.
Recorded Future and Insikt Group observed a 600% increase in the volume of compromised credentials sold in 2022. This number reflects credentials that were stolen specifically using info-stealing malware.
Do yourself a favor and set minimum password character lengths for your login portals and systems. Then encourage your employees, customers, and other users to do the following:
- Use unique passwords (or, ideally, passphrases) on all accounts instead of reusing the same password across multiple accounts.
- Avoid the use of personal information as passwords (i.e., names of family members or pets, personal dates such as anniversaries or birthdates, etc.).
- Avoid using celebrities’ names or references to pop culture (i.e., movie characters’ names, song titles, TV show titles, etc.).
- Turn on multi-factor authentication (if it’s something you have available as an option) to add another layer of security.
You’ll also want to ensure that you’re using strong password storage security practices. Before adding passwords to your database, you first should instead add a password salt and pepper (i.e., strings of random characters) to those passwords and hash them. This way, you’re storing salted/pepper password hashes instead of sensitive plaintext passwords.
In a perfect world, everyone would abide by these rules and there wouldn’t be issues of bad guys using compromised credentials to attack additional targets. But we don’t live in a perfect world; we live in a world where bad guys buy, sell, and trade compromised credentials like cheap flea market items. And since your organization’s and customers’ account secrets should be regarded as virtually priceless, then you need to treat them as such.
4. Implement Strong Passwordless Authentication
As the name implies, passwordless authentication is a concept that focuses on using other secrets to authenticate (i.e., prove your digital identity) so you can access secure systems and data. This provides a more secure alternative to traditional username + password login credentials.
Examples of authentication methods that are often considered passwordless include:
- Public key infrastructure (PKI) certificate-based authentication. This popular approach uses digitally signed X.509 digital certificates (e.g., client authentication certificates) to ensure only legitimate users can authenticate and access your sensitive resources. The certificates serve as your employees’ digital identities, which are like their digital passports, taking the guesswork out of the authentication process by proving each employee is who they say they are.
- Biometric-, app- or token-based multi-factor authentication (MFA) systems. MFA is about using at least two identifying factors (biometrics, apps, or physical tokens) to authenticate users. One example is a mobile app that uses push notifications instead of sending an SMS-based one-time PIN (OTP). (NOTE: Many 2FA methods require a username + password in addition to a push app notification. So, they’re not truly “passwordless” for that reason.)
- Magic links. These tools are one-time use links that are sent via SMS or emails during authentication processes. They have their uses in terms of convenience (i.e., users can click on links instead of entering their passwords) but also their deficits as far as security is concerned because there’s no way to verify that the users are who they say they are (in the event that users’ phone numbers or emails have been compromised).
Authentication-related data can be stored digitally using various methods (cookies, ephemeral storage, etc.). But cookies and tokens themselves aren’t actually standalone passwordless authentication measures.
The way that passwordless authentication helps to prevent credential compromise is pretty straightforward: bad guys can’t compromise your credentials if there aren’t any passwords to compromise. 93% of the professionals surveyed by Axiad (from the study we cited earlier) indicate that passwordless authentication “had (or will have) a positive impact on the workforce.”
An additional benefit of using this approach is that it moves you a step closer to achieving zero trust (and who doesn’t want that?)
5. Follow Industry Identity, Secrets, and Key Management Best Practices
Identity management is about ensuring that authorized, authenticated users can access predetermined resources, systems, and data. As such, an important part of this is ensuring that those digital identities are secure and aren’t vulnerable to compromise. To do this, it requires securing the cryptographic properties that form the foundation of each digital identity’s security.
PKI key management helps you protect the cryptographic tools you use to achieve that security. If a certificate’s private key isn’t protected, then anything it’s used to secure or authenticate is vulnerable. This is why implementing key management best practices is essential to the security of your business’s cryptographic secrets. They span everything from the policies and standards of key management to the technologies and tools and processes you use to secure the keys throughout their lifecycles.
An example of a way to securely store your keys and other secrets is using a secure, centralized solution such as a hardware security module (HSM) or key vault.
If you don’t carefully manage and secure your digital identities, cryptographic keys, and other secrets, then kiss data confidentiality and identity authentication goodbye, as the systems they secure will be vulnerable to compromise.
6. Incorporate Additional Access Security Measures Into Your Systems and Processes
In addition to integrating passwordless authentication into your IAM processes, there are some additional steps you can take to help harden access to your systems against credential compromise attacks. The approach here is to identify and prevent bot-based attacks that attempt to use compromised credentials:
- Set user and server rate limits. Setting user rate limits helps to prevent automated attacks by limiting the number of times an account can attempt to log in to a website, web application, network, API, or other digital asset within a specified period. Similarly, restricting the amount of traffic attempting to access one of your server resources within a set amount of time helps to thwart attackers who try to overwhelm your login pages with
- brute force attacks,
- credential stuffing attempts, and
- distributed denial of service (DDoS) attacks.
- Use CAPTCHAs to thwart bot-based brute force attacks. You can use CAPTCHAs on your websites and web applications to prevent bots from logging into accounts using guessed or compromised credentials.
- Implement automated event log monitoring. Event logs are simultaneously a wealth of information and also a burden to slog through. When used properly, they help you learn from successful and unsuccessful attacks to update your approach to prevent future attacks. However, they’re retroactive tools; they generate a lot of noise — so much so that it’s virtually impossible to manage manually in-the-moment when things are happening.
- Adopt IDS/IPS systems to secure your network. Intrusion detection systems (IDS) and intrusion protection systems (IPS) help to detect and identify threats in real time. These systems are ideal for larger organizations that have greater capacities and resources to implement and manage them. Smaller organizations may want to contract out services to a third-party managed security service provider that can use these resources.
7. Provide Cyber Awareness Training to Employees and Other Authorized Users
SpyCloud reports that they observed 721 million exposed credentials and 8.6 billion instances of personally identifiable information (PII) in 2022. In that same year, nearly three-quarters of users whose credentials were compromised in 2022’s data breaches were reusing previously exposed passwords.
… Fool me once, shame on you; fool me twice…
Data from ThriveDX’s 2022 Global Cybersecurity Awareness Training Study shows that “91% of successful attacks start with a lack of employee understanding.” Providing cyber awareness training that hardens your “human firewall” helps make employees and contractors less likely to fall for phishing and social engineering tactics. These attacks can otherwise lead to compromised credentials and the devastating data breaches that follow.
Just look at what happened to Twitter on July 2020. Several Twitter employees were targeted and their credentials were exposed. But the attackers didn’t stop there:
“Not all of the employees that were initially targeted had permissions to use account management tools, but the attackers used their credentials to access our internal systems and gain information about our processes. This knowledge then enabled them to target additional employees who did have access to our account support tools. Using the credentials of employees with access to these tools, the attackers targeted 130 Twitter accounts, ultimately Tweeting from 45, accessing the DM inbox of 36, and downloading the Twitter Data of 7.”
So, who were some of the targeted verified accounts? Former President Barack Obama, Elon Musk, Bill Gates, Apple, and around 100 additional high-profile users. Yikes. And to think, this kind of situation could have been prevented by employees being more aware of social engineering threats and tactics.
Did they eventually catch the people responsible for the social engineering attacks? Absolutely. But not before the damage was done and more than $100,000 worth of Bitcoin was scammed from Twitter users.
One of our previous articles covered many disturbing cyber awareness statistics that show what happens when ignorance and cluelessness among employees take the wheel. It’s virtually a guarantee that your organization will fall prey to cyber attacks and suffer the damages of data breaches.
TL;DR: Compromised Credentials and How to Stop Them from Being Used
Alright, it’s time to wrap things up. Compromised credentials are the bane of organizations, businesses, and customers worldwide. Attackers are continually seeking out new ways to swindle you and your employees out of their account secrets through:
- Phishing attacks and social engineering tactics,
- Infecting devices with malware, and
- Infiltrating connections via man-in-the-middle attacks.
Once they have their hands on your compromised credentials, they can use them in various credential attacks. To combat these attacks (or prevent them from happening in the first place), you must harden your IT and human defenses. Some ways to do this include:
- Setting up robust access controls and identity management systems
- Implementing strong authentication systems
- Adhering to industry best practices for digital identity and secrets management
- Training your employees and other authorized users
The bad news is that bad guys aren’t going anywhere; they were here yesterday, they’re here today, and they’re certainly still going to be here tomorrow. The good news, though, is that you have a better understanding now of what you can do to protect your organization and customers against credential attacks. We encourage you to take action now and make protecting your organization’s secrets and overall security a top priority.


















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown