What Is Malware? 10 Types of Malware & How They Work
Malicious code is the thing that nightmares are made of for web users and cybersecurity experts alike — here’s everything to know about what malware is and how hackers use it
If you answer a question like “what is malware?” with the definition alone, that’s going to make for one short (and really boring) article. There’s a lot more to know about what malware is and what it does than just that.
There are many different types of malware that are making life difficult for IT security experts and users alike. Although incidents involving malware seemed to be decreasing at the beginning of 2020, it looks like those numbers are coming back up, Emsisoft reports. That’s why it’s still important to know what the different types of malware are, how they’re delivered, and what you can do to protect yourself and your organization.
So, just what is malware in computer terms? We’ll break all of that down, along with covering the 10 most common types of malware and what they do.
Let’s hash it out.
What we’re hashing out…
- Malicious code is the thing that nightmares are made of for web users and cybersecurity experts alike — here’s everything to know about what malware is and how hackers use it
- Malware Definition: What Is Malware (Malicious Software)?
- Why Attackers Create and Use Malware
- 10 of the Most Common Types of Malware That You Should Know
- Not All Malware Are Created Equally….
- Consumers vs Businesses: Is One More Appealing Than the Other to Attackers?
- Common Malware Delivery Methods
- What You Can Do to Protect Yourself Against Malware-Based Threats
- Final Thoughts on the Malware Threats Facing Organizations Today
Malware Definition: What Is Malware (Malicious Software)?
The term “malware” is a portmanteau of the words “malicious” and “software.” Basically, we’d define it as a catch-all term or an overarching category that encompasses any type of malicious software or code. So, what is malware in the simplest terms?
Malware = any software or code that’s created to do something bad.
Malware can hide inside legitimate software applications or files, or its author can disguise it as a seemingly harmless app that users download unknowingly. But what does malware do? Cybercriminals often use malware to:
- Disrupt individuals’ lives and organizations’ services and operations.
- Extort or steal money or cryptocurrency.
- Take control of IT systems or devices.
Basically, I’d say that a “malware” roughly translates in IT admin speak to mean that you’re going to have a really bad day. Malware can result in everything from stolen funds to significant reputational damage. That is unless, of course, you have the right tools in place to prevent them from successfully infecting your IT systems and end user devices. But we’ll talk more about that later…
The reality is that malware isn’t anything new to the digital world. Malicious computer code has been around for decades. AVG reports that the concept of computer viruses dates back to 1966 with the first worm-type malware (then classified as a virus) coming to fruition in 1971! But even still, it’s a threat that cybersecurity experts worldwide are facing and fighting each day.
How Others Define Malware
Of course, different people and organizations define malware differently. For example, Microsoft tends to be a bit generic in their definition of malware: “Malware is the overarching name for applications and other code, i.e. software, that Microsoft classifies more granularly as malicious software or unwanted software.”
The National Institute of Standards and Technology (NIST), on the other hand, cites multiple definitions for the term, describing it as “hardware, firmware, or software that is intentionally included or inserted in a system for a harmful purpose.”
Here’s one of NIST’s more specific malware definitions:
A program that is inserted into a system, usually covertly, with the intent of compromising the confidentiality, integrity, or availability of the victim’s data, applications, or operating system or of otherwise annoying or disrupting the victim.”
A lot of the time, hackers and other cybercriminals use malware as a way to turn a profit. However, that’s not the only reason why hackers use malware.
Why Attackers Create and Use Malware
Now that we’ve defined malware and know what it is, let’s talk about why the bad guys use malware over other attack methods. Malware serves a variety of purposes. For example, some cybercriminals use malware:
- To profit financially (either directly or through the sale of their products or services). For example, they may use malware to infect targets’ devices to steal account information or cryptocurrency. They may sell their malware to other cybercriminals to use as they see fit or may sell it as a service offering. (Yes, DDoS-as-a-service and ransomware-as-a-service really are things that exist.)
- As a means of revenge or to carry out a personal agenda. For example, Brian Krebs of Krebs on Security faced an issue a few years ago when a DDoS attacker decided he didn’t like Krebs talking about him.
- To carry out a political or social agenda. Some perfect examples of this would be nation-state actors (like state-run hacker groups in China and North Korea) and hacker groups like Anonymous.
- As a way to entertain themselves. I guess some people just aren’t content binge-watching Netflix or Disney+. Instead, some cybercriminals are kind of like joyriders — they choose to drive away boredom by victimizing others.
Now that we have a pretty good idea of why cybercriminals use malware, let’s talk about the most common types of malware that pose threats to organizations and consumers.
10 of the Most Common Types of Malware That You Should Know
Now that you know what malware is in a general sense, let’s get specific about the different types of malicious software that exist. After all, there are a lot of things that fall under the umbrella of “malware.” And something you’re bound to notice as you read through the list is that there’s frequently overlap between the various categories of malware.
Just to make things a little easier, we’re going to go over some of the biggest offenders in alphabetical order:
1. Adware

Everyone hates those dreaded little pop ups. They lie, telling you that there’s something wrong with your computer or that there’s a piece of software that you’ve never even heard of that needs an update.
Adware is the software that displays these types of unwanted ads on your screen. These ads may just be harmless (but annoying) pop-ups, or they can be harmful ads that redirect users’ search requests to malicious sites. Although not all adware is malicious, it’s still something you don’t want on your devices.
Adware may generate one carefully crafted pop-up, or it might be a whole slew of them that seemingly overtake your entire monitor. Either way, adware is usually bad news. In addition to annoying you, adware also enables bad guys to steal data from your device and target ads in the future.
Adware dominated the consumer threat detection category in 2019. Malwarebytes reports in its 2020 State of Malware Report that there were 54 million adware detections on Windows (24 million) and Apple devices (30 million). Adware also captured the top business malware detection as well, increasing a whopping 463% from its 2018 detections.
Defining Adware vs Malvertising
Although some may lump these two together, adware and malicious advertisements are actually two separate threats. Adware = malware that displays ads. Malvertising = ads that spread malware. They usually take advantage of exploitable vulnerabilities within the users’ browsers.
Of course, there are some malvertisements that auto-install malware on users’ devices via drive-by downloads. This results in malware being installed on the users’ individual devices that can redirect users’ legitimate web searches to lookalike phishing websites. There, hackers can then steal your login credentials or other personal data.
2. Botnet Malware
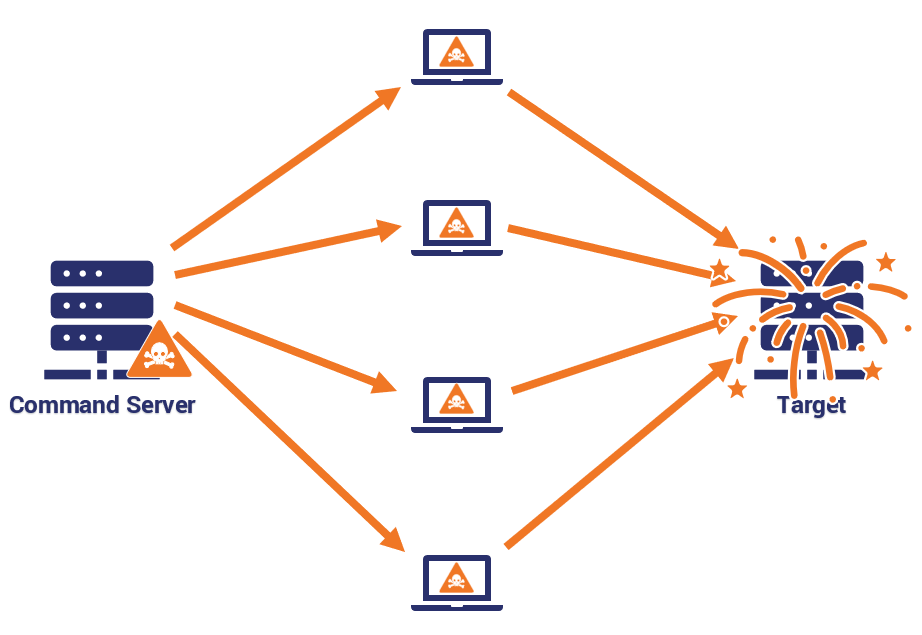
A botnet is a network of compromised computers, servers, and IoT devices (infected devices that are also sometimes called bots or zombies). The devices are infected with a malware and form a massive weapon that cybercriminals can use to launch massive distributed denial of service (DDoS) attacks against individuals, governments, and organizations. These attacks inundate the target with traffic requests or packets to disrupt the server or network, or to take it offline completely.
Of course, there are other ways that botnets can be useful to cybercriminals:
- Brute force & credential stuffing attacks — Bots can be used to carry out different types of brute force attacks on websites. They’ll use a pre-configured list of usernames and passwords combinations on website login pages. The hope is that with enough tries, they’ll get lucky and find a winning combination.
- Data and content scraping — This is a pretty crappy way to doing business, but some individuals and organizations love to resort to underhanded tactics. Scraping uses botnets to comb through websites and databases to cull useful information they can use to undercut their competition. This could be site content, pricing sheets, or other useful information.
- Botnet-as-a-service opportunities — Cybercriminals sometimes rent their botnets to all types of malicious users — including those who are less tech savvy. This service is also sometimes called malware-as-a-service, according to the International Botnet and IoT Security Guide 2020 by the Council to Secure the Digital Economy (CSDE). These bot armies essentially serve as mercenaries-for-hire to take down a target’s servers and networks.
One of the biggest (and “baddest”) botnets in existence is called Mirai. This massive botnet of compromised IoT devices — infected with the Mirai malware — is responsible for some of the biggest DDoS attacks in recent years. (It was most famously known for taking down huge numbers of websites in 2016.)
But where do the majority of these “bad bots” originate? None other than the good ol’ USA! Imperva reports in their 2020 Bad Bot Report that 45.9% of all bad bot traffic comes from compromised devices in the United States.
Of course, different malware threats can change over time as their authors determine new ways to use them to their advantage. For example, Malwarebytes reports in their 2020 State of Malware Report that Emotet and Trickbot — two former banking trojans — have evolved into “first-stage infection vendors and botnets.”
Now, there are also some newer botnets that borrow from tried-and-true models like Mirai. One such new IoT botnet that uses some Mirai code is called dark_nexus. It’s named such by its the Bitdefender researchers who discovered it because the term “dark_nexus” appears in its banner. According to Bitdefender’s report:
While it might share some features with previously known IoT botnets, the way some of its modules have been developed makes it significantly more potent and robust. For example, payloads are compiled for 12 different CPU architectures and dynamically delivered based on the victim’s configuration.”
A TechRepublic article on the company’s study quotes Bogdan Botezatu, director of threat research and reporting for Bitdefender. In the article, Botezatu shares the prices that the botnet’s creator is renting the botnet out for:
The dark_nexus botnet is being promoted for sale on YouTube, with advertised prices as low as about $18.50 per month for 2,500 seconds of boot time […] For about $99 a month, attackers can buy unlimited access, making the botnet accessible to anyone with $20 and fairly basic computer skills to launch their own disruptions.”
So, basically, for less than what you’d pay for a monthly subscription to some popular TV streaming services, you could rent a botnet to launch attacks. I guess we’ll just have to keep an eye on this one to see what happens with it in the future. Considering that since it was first discovered in 2019, it’s already undergone several updates by its creator (over 30 versions in three months), I’m sure it’ll be a bumpy ride.
3. Cryptomining Malware
Cryptomining currency malware, also known as a cryptominer or cryptomining malware, is a type of malware that cybercriminals use to mine cryptocurrency. According to the Cybersecurity & Infrastructure Security Agency’s (CISA) Security Tip (ST18-002), it does this by running complex mathematical calculations to “mine” new coins — which the cybercriminals then keep for themselves.
Cryptocurrency miners often use server farms as part of their mining efforts. As you can imagine, all of this takes a lot of computers and electricity — some researchers estimate that Bitcoin mining uses more electricity than the whole country of Switzerland. So, some cybercriminals take an unethical shortcut: they write malware to run on other people’s computers — IoT devices, mobile devices, computers, servers, networks, etc. — to use their resources and force their machines to do the mining for them. Most cryptomining apps are categorized as PUAs — potentially unwanted apps — or, in rarer cases, as trojans. However, there’s a more modern method of cryptomining — cryptojacking — that also works in your browser.
“Cryptojacking occurs when malicious cyber actors effectively hijack the processing power of the victim devices and systems by exploiting vulnerabilities—in webpages, software, and operating systems—to illicitly install cryptomining software on victim devices and systems. With the cryptomining software installed, the malicious cyber actors to earn cryptocurrency. Additionally, malicious cyber actors may infect a website with cryptomining JavaScript code, which leverages a visitor’s processing power via their browser to mine cryptocurrency.”
But what type of cryptocurrency do cybercriminals most commonly target? According to ESET, most cryptominers focus on Monero instead of other types of cryptocurrencies like Bitcoin for two key reasons:
This cryptocurrency has many advantages over the better-known bitcoin: it offers anonymous transactions and can be mined with regular CPUs and GPUs instead of expensive, specialized hardware.”
4. Fileless Malware

Okay, now this is where things might get a bit strange considering that everything we’ve discussed so far involves some sort of downloadable or executable. However, there’s a type of malware that breaks the traditional malware mold — it’s known as fileless malware.
Basically, fileless malware is a threat that uses code that already exists within your computer or device to carry out an attacker’s agenda. IBM describes it as a type of attack that involves attackers “living off the land” because they’re simply taking advantage of legitimate tools and software (known as “LOLBins”) that exist within your computer. These fileless attacks often rely on executables, tools, and scripts include everything from Windows PowerShell to Office documents.
What makes this threat particularly dangerous is that it’s very hard to detect. Because it doesn’t require any downloads or executables like traditional malware, it’s able to navigate many traditional anti-malware tools. Remember the drive-by cyber attacks that we mentioned earlier? Those frequently involve the use of fileless malware.
The Ponemon Institute’s 2020 State of Endpoint Security survey report, sponsored by Morphisec, states that survey respondents indicate that they think 41% of cyber attacks will involve fileless malware next year (compared to their estimates of 59% of file-based cyber attacks). But just how much of a risk is fileless malware? Let’s put it this way: The survey respondents shared that fileless attacks and existing/known threats were equally likely (68%) to compromise their organizations.
5. Ransomware
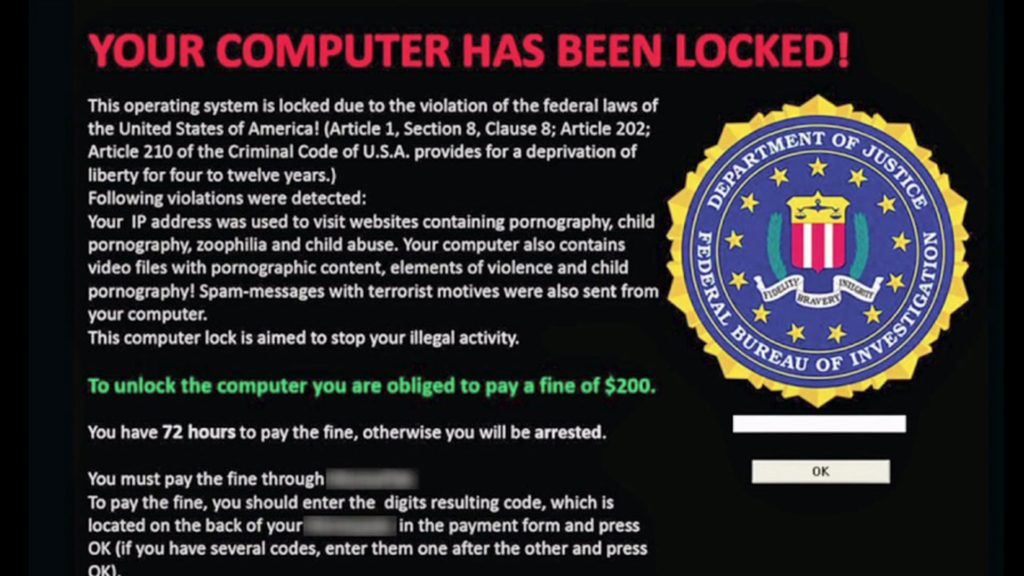
Yeah, you’ve definitely seen headlines about this type of malware in 2020. Verizon’s 2020 Data Breach Investigations Report shares that 27% of all malware-related incidents they tracked in 2019 involved ransomware. Ransomware is a type of malware that encrypts a target’s data until some demand is satisfied — typically, the payment of a ransom. (Hence the clever malware name.)
So, how does ransomware work? Tim Femister, vice president of digital infrastructure at ConvergeOne, shared with Forbes the “Five Uneasy E’s” of ransomware:
- “Exfiltrate: Capture and send data to a remote attacker server for later leverage.
- Eliminate: Identify and delete enterprise backups to improve odds of payment.
- Encrypt: Use leading encryption protocols to fully encrypt data.
- Expose: Provide proof of data and threaten public exposure and a data auction if payment is not made.
- Extort: Demand an exorbitant payment paid via cryptocurrency.”
The Rise of Ransomware
This year, we’ve seen a variety of new ransomware popping up — and it’s an issue that’s increasingly targeting organizations over individuals. And while it may look like ransomware numbers are dropping and becoming less of a threat, Malwarebytes is quick to caution in their 2020 State of Malware Report that the numbers are misleading:
Ransomware operations in 2019 haven’t so much slowed down as their targeting has become more precise. Instead of spraying a wide cross-section of potential victims, ransomware authors sniped the most vulnerable rich targets they could find.”
For example, researchers discovered a new CryCryptor ransomware masquerading as COVID Alert, the official COVID-19 contact-tracing app for Canada. Thankfully, ESET researchers were able to create a decryption tool to help those whose files were encrypted by the ransomware.
In August 2020, Carnival Corporation reported to the SEC that the cruise line was hit by ransomware that resulted in access to guests’ and employees’ personal data. And earlier this year, we shared with you about how the entertainment law firm Grubman, Shire, Meiselas & Sacks found itself facing a $42 million ransomware payment demand. Last year, we also shared about a ransomware attack that targeted the city of Johannesburg and how ransomware attacks also cause life-threatening issues for hospitals and other healthcare providers.
In addition to traditional ransomware threats, businesses are increasingly facing threats from ransomware-as-a-service models (such as Sodinokibi) as well. For a list of additional ransomware-related statistics, check out our article “20 Ransomware Statistics You’re Powerless to Resist Reading.”
6. Rootkits
A rootkit is a remote access tool (RAT) or application that provides remote admin access to devices. This isn’t bad in and of itself. But, as you can imagine, this means that they can cause a lot of damage if they’re put to work by someone with devious intentions.
But why do rootkits pose such big security risks?
- Modern rootkits are typically associated with malware such as worms, viruses, and trojans.
- 2. They’re damned near impossible to find and require specialized scanner tools. That’s because the whole purpose of a rootkit is to enable access while evading detection. Rootkits can modify core files and mask other malware that may be hiding within your system. As a result, many traditional antivirus tools struggle to detect them.
- They provide unfettered access to a person’s device without them ever knowing it.
Heimdal Security sums up nicely what it is that rootkits do:
Once a rootkit installs itself on your computer, it will boot up at the same time as your PC. On top of that, by having administrator access, it can track everything you do on the device, scan your traffic, install programs without your consent, hijack your computer’s resources or enslave it in a botnet.”
Types of Rootkits
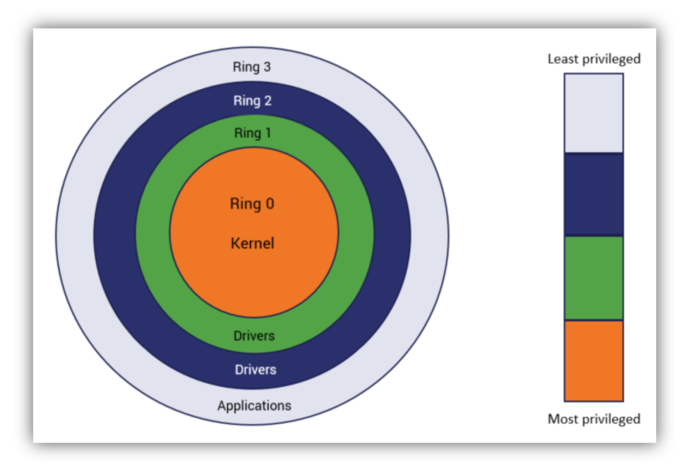
Traditionally, rootkits can install themselves in ring zero (kernel level), although some sources say that they can install themselves all the way up to ring three (user level). This means that they can get as much (or as little) access as necessary. This is good news for cybercriminals and really bad news for you.
There are different types of rootkits, which are typically categorized by the reach of the systems they affect:
- User-level/application level rootkits (although the SANS Institute refers to these as non-rootkit trojans)
- Kernel-level rootkits
- Hardware rootkits
- Bootkit rootkits
- Virtualization rootkits
If you’re looking for more specific information about particular rootkit variants, check out this comprehensive list from BleepingComputer.
7. Spyware
Much like the name would suggest, spyware is a type of monitoring software that allows someone to observe your activities without your knowledge or authorization. This type of malware provides bad guys with access to your sensitive personal information and data. This could include everything you ever type into your computer — everything from your personal and financial account information to health-related data.
But just how big of a threat is spyware? Malwarebytes’ data shows in their 2020 State of Malware Report that consumer-focused spyware was detected 465,284 times in 2019 (an increase of 4% from 2018’s reported 448,026 detections). This puts it at No. 7 on their list of global consumer threat categories. This differs from business-focused threats, which dropped from 246,156 to 110,805 — a decrease of 55% — from 2018 to 2019. This puts it at No. 6 on their list of global business categories rankings.
So, while it’s not the biggest threat you or your organization may face, it’s still something to be cognizant of and to regularly scan for on your devices.
Keyloggers
A specific type of spyware is known as a keylogger (or a “keystroke logger” for you more specific readers). A keylogger is a type of hardware or software that records everything you type without needing access to what’s on your monitor. That’s because it records all of your keyboard activities — basically, every keystroke you type on your keyboard. The benefit of this to hackers is that it allows them to monitor your activities and capture sensitive information such as your account credentials and passwords.
Basically, all keyloggers are types of spyware, but not all spyware is keylogging malware. And, as weird as it may sound, not all keyloggers are bad. In fact, as Sophos reports, some businesses use keylogging legitimately within their IT departments to troubleshoot tech issues. The difference is whether 1) the keylogger is installed with the owner’s knowledge, and 2) whether it’s installed with malicious or legitimate intentions.
Keyloggers come in hardware or software formats, which means that the installer doesn’t necessarily require physical access to your device to use one.
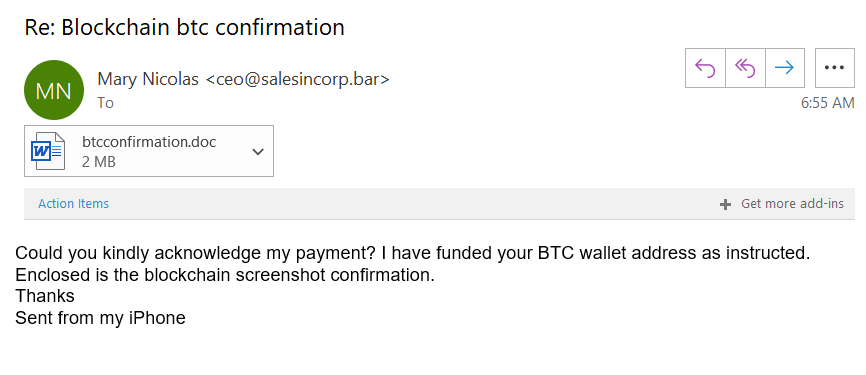
8. Trojans

Ah, trojans. Now, here’s a truly insidious threat (much like rootkits). A trojan, which is short for “trojan horse,” is a type of malware or malicious code that hackers use to infiltrate devices. The name hearkens back to the mythological giant wooden horse that Homer describes in The Iliad of the siege on the city of Troy during the Trojan War.
We won’t get into all of the details of the story. But, basically, the point here is that the trojan horse (as the wooden horse came to be known) is all about subterfuge and disguising something dangerous as something harmless. In the case of computer malware trojans, they’re malicious software or code that masquerade as legitimate files, including:
- Office documents (such as Word files and Excel spreadsheets)
- PDFs
- Software executables
Trojans, as we often call them in computer terms, are a big threat for consumers and organizations alike. Malwarebytes reports in their 2020 State of Malware Report that in 2019:
- Trojans slipped from first to second place from the previous year with 6,637,893 detections (down 7% from 7,161,012) for consumers, and
- Trojan detections for businesses decreased 25% from 3,745,473 to 2,809,198 in that same period.
Some of the most notable trojan strains include:
- Emotet
- Trickbot
- Ryuk
- Sodinokibi
- Mirai
- SamSam
9. Viruses
Let’s quickly clear one thing up since there’s sometimes confusion about viruses and malware. Viruses are a type of malware, but not all malware are viruses. It’s kind of like how all ice creams are desserts, but not all desserts are ice cream. Cool? Cool.
Much like how viruses spread from person to person, computer viruses are a category of malware that self-replicates. Its goal is to spread its malicious code to as many other programs and devices as possible. However, one thing it needs to activate and spread is some type of action from the user.
According to Kaspersky:
Viruses are often attached or concealed in shared or downloaded files, both executable files—a program that runs script—and non-executable files such as a Word document or an image file. When the host file is accepted or loaded by a target system, the virus remains dormant until the infected host file is activated. Only after the host file is activated, can the virus run, executing malicious code and replicating to infect other files on your system.”
Viruses can exploit vulnerabilities in software applications and operating systems. However, they also can infect users’ devices through:
- Infected email attachments
- Malicious scripts and downloads from websites
- Removable external media
10. Worms
Like viruses, worms are a type of malware that also spread from a host to other devices. However, unlike viruses, worms are more insidious because they don’t require the human element to activate or spread their malicious code. They’re standalone software that typically “worm” their way through your defenses by exploiting existing vulnerabilities on a target’s system.
CISA reports that these nasty little suckers can drain your computer or network of its valuable resources and bandwidth. However, CISA also says that modern worms do much more than that:
In the past, worms were designed primarily to propagate. The impact on victims and organizations was primarily a disruption of service resulting in loss of productivity and sometimes a loss in revenue. Now, many of the significant worms are designed to steal sensitive information such as credit card numbers, social security numbers, pin codes, and passwords and send the information to the attacker for nefarious purposes including identity theft.”
Some good news, though, is that worms might be falling out of favor with cybercriminals. Malwarebytes reports in their 2020 State of Malware report that detections of worms in their top 10 global business threat categories decreased 61% from 2018 to 2019. They also observed a 28% decrease in global consumer threat worm detections as well.
However, there still are big vulnerabilities that researchers, ethical hackers, and manufacturers are discovering that are highly susceptible to exploitation via worms. For example, CISA released an emergency directive back in July to address a critical vulnerability (CVE-2020-1350) that could take full control of systems and networks.
This release underscores the importance of keeping systems and software as up to date as possible.
Not All Malware Are Created Equally….
What if I were to tell you that there are different types of malware out there that actually adapt and change to avoid detection? We’ve written about polymorphic malware and metamorphic malware in the past, but it’s something that definitely bears repeating.
If you never got a chance to read that article last year (which we definitely encourage you to do), they are two fascinating — and worrisome — variants of malware that you should definitely know about. This is particularly true considering that Webroot reported in their 2019 Threat Report that “Polymorphic malware is here to stay: it continues to account for 93% of all malicious Windows executables.”
But what exactly is it? Polymorphic malware is defined as malware that changes part of its code with every new propagation of itself. Metamorphic malware, on the other hand, is malware that changes all of its code with each new iteration so that it no longer matches. We equated it to the difference between the two as a leopard changing its spots (polymorphic) as compared to a tiger becoming a lion (metamorphic).
As you can imagine, this makes it highly difficult — if not impossible — for signature-based cybersecurity tools to detect these threats. This is where behavior-based tools can be a real gamechanger.
Consumers vs Businesses: Is One More Appealing Than the Other to Attackers?
Malwarebytes reports that over the past two years, malware attacks are targeting organizations and businesses more frequently than consumers. Business malware threat detections increased 13% in 2019, whereas consumer-targeted detections decreased slightly by 2%.
Part of this change is thought to be because of anticipated larger payouts. After all, businesses have larger coffers, which means that they can likely pay larger ransoms than average consumers. Plus, they’re more likely to have large databases filled with sensitive data that can be exploited or sold.
Common Malware Delivery Methods
There are many ways that the bad guys can deliver their malicious software. They can do it through more direct methods — such as those that require physical access to servers, networks, and end user devices. Or they can do it virtually through malicious websites and email.
Phishing and Malicious Email Links and Attachments
But if you’re wondering what malware’s most common delivery method is, then look no further. We’ve shared with you (a lot) about the dangers of phishing. So, it probably doesn’t come as a surprise that Verizon’s 2020 DBIR states that most malware is delivered via email. However, they’re careful to hedge their statement with a caveat that the “average” doesn’t necessarily represent all organizations.
Social Phishing Messages
Social media is a great way to stay connected with friends and family. However, this category of platforms is also ripe with opportunities for hackers to send and spread malware to unsuspecting users.
The same can be said about SMS text messages…
Smishing (SMS Phishing)
Smishing is a growing alternative threat vector — but its level of concern varies depending on whom you ask. But it’s definitely happening — Proofpoint says in their 2020 State of the Phish annual report that 84% of organizations experienced smishing attacks in 2019.
Infected Detachable Devices
Another way to deliver malware is through the use of infected USB thumb drives and other detachable technologies. (If you ever got upset when your IT guy ever reprimanded you for plugging in a non-company-issued USB drive, now you know why they did.) Using malware-loaded devices is a big risk to your security because they can bypass many of your cybersecurity defenses.
Don’t believe me? Let’s not forget about good ol’ Stuxnet. That malware was able to get into an Iranian nuclear facility’s computers, after all, via infected USB sticks. (The USB sticks were used to infect machines at other companies to allow the worm to spread by proxy via their infected devices.)
Phishing and Malicious Legitimate Websites
You likely know that clicking on a phishing website can be dangerous. But as you learned earlier, your device can also get infected on legitimate websites, too, if they get compromised. For example, malicious advertisements (malvertising) can appear on legit websites. And if they’re loaded with drive-by malware, then it can infect your device without needing you to click on something!
What You Can Do to Protect Yourself Against Malware-Based Threats

From a cybersecurity standpoint, the best thing that you can do to protect your organization from malware-wielding cybercriminals is to make yourself as challenging a target as possible. This typically involves a layered approach to cybersecurity. While it’s not possible to block every single threat, you can make yourself a more challenging target than other businesses who don’t give a rat’s patootie about security.
Not only does this approach increase your chances of withstanding basic cyber attacks, it also makes you more resistant to lazy cybercriminals who are just looking for a quick payday.
Here are 12 things you can do to make your organization more secure against malware attacks:
- Keep all of your devices, operating systems, plugins, and browsers up to date. This should go without saying, but it bears repeating since people tend to let updates and patching slide. Roll out patches and updates as soon as possible! They’re a manufacturer’s way of fixing bugs and eliminating security gaps in their products (that, in turn, leave you vulnerable to many types of cyber attacks). If you’re bad at remembering to perform updates and patches, then maybe it’s time to turn on automatic updates. Do you remember WannaCry? That exploit was only so successful because so many organizations were running unpatched computers!
- Limit account access to only those who need it to do their jobs. Access is something that should be exclusive and not shared by everyone. What we mean is that not everyone needs access to your network, databases, servers, or other aspects of your IT infrastructure. We don’t care how much Tammy in accounting or Jed in HR complain — if they don’t need access to do their jobs, don’t give it to them. By limiting access, you’re reducing potential exposure in the event that their accounts become compromised.
- Require strong, unique passwords. Although there are many ways to approach passwords, the way I personally like to do it is by creating long, nonsensical passphrases instead of traditional passwords. This way, it’s a lot more difficult for cybercriminals to guess or try to brute force.
- Provide cyber awareness training to your non-customer users. If anyone has access to your devices, databases, or network, make sure that they’re trained and aware of a cyber threats (including social engineering). This includes everyone from your regular employees and contractors to your c-suite execs and even members of your board. Human error and negligence are among the biggest threats to your organization’s cybersecurity. This is why it’s important to use good cyber hygiene and to follow good security practices.
- Use anti-virus and anti-malware tools on your endpoint devices. Each of these tools serves its own purpose, and both are beneficial to use simultaneously (so long as they’re compatible).
- Use X.509 digital certificates to secure your domain and email. These types of certificates offer security through identity and encryption. For example:
- SSL/TLS certificates are website security certificates that enable the secure, encrypted transmission of data between users and your site’s web server. It also enables you to assert your identity and prove to browsers and users alike that your website is legit and isn’t a phishing website.
- Email signing certificates allow you to digitally sign your emails and send encrypted messages to others who use S/MIME certificates. Implementing a digital signature policy for corporate emails can make it a lot easier to detect and avoid phishing emails.
- Set email filters. Email filters are a great way to help prevent emails containing malicious attachments and links from reaching your inbox. However, they’re not foolproof; there are ways that cybercriminals can bypass email filters. This is one of many examples where cyber awareness training can help.
- Increase your network perimeter security with firewalls. Firewalls are a great way to filter the traffic that travels to and from your network. Of course, there are different categories these network security devices and software, so you’ll have to figure out which one best suits your needs.
- Use both signature-based and behavior-based detection tools. They’re like salt and pepper, or wine and cheese. Much like how this spice pair enhances the flavor of your food, using both of these tools increases your cyber defenses in different ways. While you technically can use one without the other, it wouldn’t be as comprehensive as what you’d get with the combination of the two.
- Put email security protocols to work. Domain-based message authentication reporting and conformance (DMARC), domainkeys identified mail (DKIM) and sender policy framework (SPF) are excellent ways to protect your organization and its identity from malicious emails.
- DKIM: The idea behind this email security mechanism is that you update your DNS entry to include a digital signature. It helps to prevent spoofing of outgoing messages from your domain. This helps to prevent bad guys from sending emails to others (or your own employees) while masquerading as you.
- SPF: This DNS record helps you to combat phishing and spam by specifying which IPs your organization can send emails from. If someone tries to send emails from your domain using an IP that’s not listed in your DNS SPF record, it’ll automatically be distrusted.
- DMARC: This protocol, which relies on both DKIM and SPF, helps to mitigate phishing and direct domain spoofing attacks by rejecting or spamming emails automatically. This helps to prevent the malicious emails that cybercriminals use to transmit malware from ever reaching your inbox.
- Eliminate legacy programs and devices — If it’s not something your organization uses, get rid of it. Any outdated programs and devices may be an attack vector that cybercriminals can exploit.
- Perform vulnerability assessments and penetrating testing. Both of these tactics are excellent way to discover any vulnerabilities that exist within your network and general IT infrastructure and how cybercriminals can be exploit them. This way, you can beat them to the punch and remediate these risks before they have a chance to exploit them.
Final Thoughts on the Malware Threats Facing Organizations Today
Although malware on its own as a single attack method isn’t as common now, it’s still widely used in combination with other tactics and technologies. And as much as we’d like to say that malware is going away, it’s still a very real threat to organizations and individuals. And that’s something that’s not likely to change. Rather than focusing on creating entirely new threats, many cybercriminals seem to be focusing their efforts on putting new twists on existing threat vectors. Malware is one of them.
This is why it’s crucial for businesses to harden their cybersecurity defenses and make themselves tougher targets. Many cybercriminals often go for the low-hanging fruit — they want the biggest payout with the least amount of effort.
We hope this has answered your questions about what malware is, the different types of malware that exists, and how malicious code can spread across your network and the internet in general.
As always, leave your comments and insights in the comments section below…


















































5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam – 2018
in Hashing Out Cyber SecurityHow to Fix ‘ERR_SSL_PROTOCOL_ERROR’ on Google Chrome
in Everything EncryptionRe-Hashed: How to Fix SSL Connection Errors on Android Phones
in Everything EncryptionCloud Security: 5 Serious Emerging Cloud Computing Threats to Avoid
in ssl certificatesThis is what happens when your SSL certificate expires
in Everything EncryptionRe-Hashed: Troubleshoot Firefox’s “Performing TLS Handshake” Message
in Hashing Out Cyber SecurityReport it Right: AMCA got hacked – Not Quest and LabCorp
in Hashing Out Cyber SecurityRe-Hashed: How to clear HSTS settings in Chrome and Firefox
in Everything EncryptionRe-Hashed: The Difference Between SHA-1, SHA-2 and SHA-256 Hash Algorithms
in Everything EncryptionThe Difference Between Root Certificates and Intermediate Certificates
in Everything EncryptionThe difference between Encryption, Hashing and Salting
in Everything EncryptionRe-Hashed: How To Disable Firefox Insecure Password Warnings
in Hashing Out Cyber SecurityCipher Suites: Ciphers, Algorithms and Negotiating Security Settings
in Everything EncryptionThe Ultimate Hacker Movies List for December 2020
in Hashing Out Cyber Security Monthly DigestAnatomy of a Scam: Work from home for Amazon
in Hashing Out Cyber SecurityThe Top 9 Cyber Security Threats That Will Ruin Your Day
in Hashing Out Cyber SecurityHow strong is 256-bit Encryption?
in Everything EncryptionRe-Hashed: How to Trust Manually Installed Root Certificates in iOS 10.3
in Everything EncryptionHow to View SSL Certificate Details in Chrome 56
in Industry LowdownA Call To Let’s Encrypt: Stop Issuing “PayPal” Certificates
in Industry Lowdown